ISO 27001 Annex A 5.7 Threat Intelligence is a security control that requires organizations to collect and analyze information regarding information security threats. The primary implementation requirement involves processing tactical, operational, and strategic data. This framework provides the business benefit of proactive defense, enabling preemptive mitigation against modern cyberattacks.
In this guide, I will show you exactly how to implement ISO 27001 Annex A 5.7 and ensure you pass your audit. You will get a complete walkthrough of the control, practical implementation examples, and access to the ISO 27001 templates and toolkit that make compliance easy.
I am Stuart Barker, an ISO 27001 Lead Auditor with over 30 years of experience conducting hundreds of audits. I will cut through the jargon to show you exactly what changed in the 2022 update and provide you with plain-English advice to get you certified.
Key Takeaways: ISO 27001 Annex A 5.7 Threat Intelligence
ISO 27001 Annex A 5.7 is a new control introduced in the 2022 update that requires organizations to collect and analyze information regarding information security threats. The goal is to shift from reactive firefighting to proactive defense. By gathering intelligence on the “who, how, and when” of modern cyberattacks, organizations can implement specific mitigations before a breach occurs. This control is essential for modern risk management, ensuring your defenses are based on real-world data rather than generic assumptions.
- Sources of threat intelligence information are readily available and many are free
- Management of threats is done by risk management
- You can do it yourself with How To Create an ISO 27001 Threat Intelligence Process and Report
Core requirements for compliance include:
- Layered Intelligence: You must address threat intelligence at three levels: Strategic (high-level trends for the Board), Tactical (attacker methodologies for IT managers), and Operational (technical indicators like malicious IPs for SOC teams).
- Source Identification: You must identify and vet both Internal (logs, incident reports) and External (government alerts, vendor feeds, news sites) sources of threat data.
- Analysis & Action: It is not enough to simply “receive” a newsletter. You must prove you have analyzed the data for relevance and taken mitigation action (e.g., updating a firewall rule or patching a specific vulnerability).
- Information Sharing: Where appropriate, organizations are encouraged to share threat information with industry peers or special interest groups to improve collective defense.
- Integration with Risk Management: Relevant threats identified through intelligence must be added to your Risk Register and managed via your formal risk treatment process.
Audit Focus: Auditors will look for “The Chain of Action”:
- The Source Inventory: “Show me your list of vetted threat intelligence sources. Are they reputable and up-to-date?”
- Reporting Proof: “Show me a recent Threat Intelligence Report. Who reviewed it and what was the outcome?”
- Direct Mitigation: “Can you show me a specific security change (e.g., a new blocklist or patch) that was triggered by a threat intelligence alert?”
The 3 Layers of Threat Intelligence (Audit Prep):
| Layer | Primary Audience | Core Focus | ISO 27001 Use Case | ISO 27001:2022 Control |
|---|---|---|---|---|
| Strategic | Board / C-Suite. | Global trends & financial risk. | Informing ISMS Scope & Budget. | Annex A 5.7 / Clause 4.1 |
| Tactical | IT Managers. | Attack Methods (TTPs). | Tuning Firewall rules & patching. | Annex A 5.7 / 8.8 |
| Operational | Tech / Software. | Specific Data (IOCs). | Blocking bad IPs & virus updates. | Annex A 5.7 / 8.16 |
Table of Contents
- What is ISO 27001 Annex A 5.7?
- Watch the ISO 27001 Annex A 5.7 Video Tutorial
- ISO 27001 Annex A 5.7 Podcast
- Why is ISO 27001 Threat Intelligence important?
- The 3 layers of threat intelligence
- ISO 27001 Annex A 5.7 Implementation Guidance
- How to implement ISO 27001 Annex A 5.7
- ISO 27001 Annex A 5.7 Implementation Checklist
- Selecting Threat Intelligence Sources: Internal vs. External
- The threat intelligence reporting process
- The contents of the threat intelligence report
- How to create a threat intelligence process and report in under 10 minutes
- Free vs. Paid Sources Table
- How to comply
- How to pass the audit of ISO 27001 Annex A 5.7
- How to audit ISO 27001 Annex A 5.7
- ISO 27001 Annex A 5.7 Audit Checklist
- Top 3 Mistakes Implementing Threat Intelligence
- Applicability of ISO 27001 Annex A 5.7 across different business models.
- Fast Track ISO 27001 Annex A 5.7 Compliance with the ISO 27001 Toolkit
- ISO 27001 Annex A 5.7 Applicable Laws and Related Standards
- ISO 27001 Annex A 5.7 FAQ
- Summary: Your ISO 27001 Annex A 5.7 Implementation Roadmap
- Further Reading
- Related ISO 27001 Controls
- ISO 27001 Controls and Attribute Values
- ISO 27001 Annex A 5.7 Mind Map
DO IT YOURSELF ISO 27001
All the templates, tools, support and knowledge you need to do it yourself.

What is ISO 27001 Annex A 5.7?
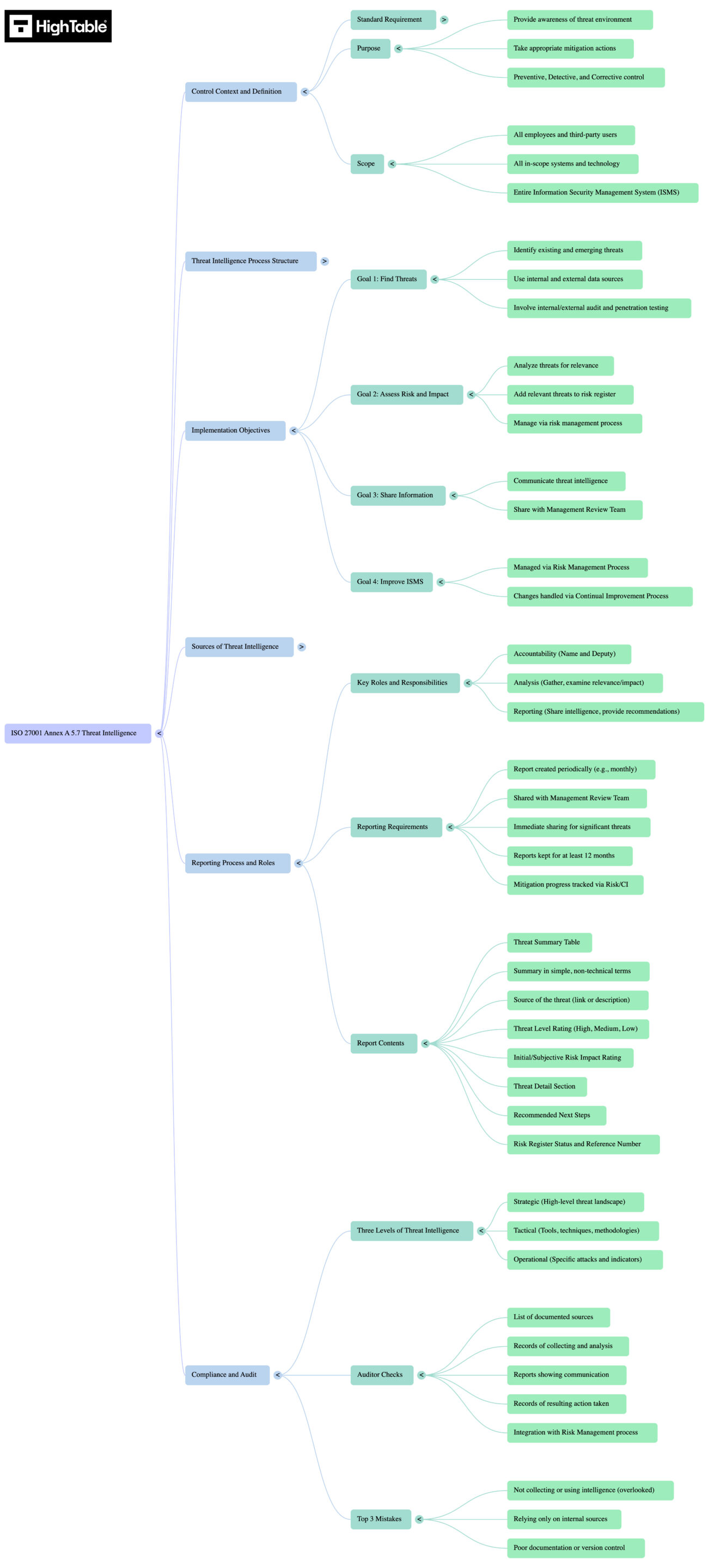
ISO 27001 Annex A 5.7 Threat Intelligence is an ISO 27001 control that requires an organisation to collect and analyse information relating to information security threats and use that information take mitigation action.
Threat intelligence is used to prevent, detect or respond to threats. You can produce your own threat intelligence but as a rule you will make use of threat intelligence produced by others. It is often provided by independent providers and advisors which can include government sources and more than likely products and services will spring up around this new control to offer you it as a service, at a cost of course.
Threat Intelligence is a new control is ISO 27001:2022 and is about understanding and managing the threats to your information security. Threats to the confidentiality, integrity and availability of data.
It can be confusing when you first come to this control but I will show you what is required and some simple, practical steps you can take to implement it.
ISO 27001 Threat Intelligence is the identification and management of information security threats.
In ISO 27001 this is known as ISO27001:2022 Annex A 5.7 Threat Intelligence .
ISO 27001 Annex A 5.7 Purpose
ISO 27001 Annex A 5.7 is preventive, detective and corrective control that ensure you provide awareness of the organisations threat environment so that the appropriate mitigation actions can be taken.
ISO 27001 Annex A 5.7 Definition
The ISO 27001 standard defines ISO 27001 Threat Intelligence: Annex A 5.7 as:
Information relating to information security threats should be collected and analysed to produce threat intelligence.
ISO 27001:2022 Annex A 5.7 Threat Intelligence
Watch the ISO 27001 Annex A 5.7 Video Tutorial
In the video ISO 27001 Annex A 5.7 Threat Intelligence Explained show you how to implement it and how to pass the audit. In this video, we cover:
- A walkthrough of the reporting template.
- The definition of Threat Intelligence for ISO 27001.
- How to distinguish between Internal and External sources.
ISO 27001 Annex A 5.7 Podcast
Listen to the ISO 27001 Threat Intelligence Deep Dive Podcast for the consultants blue print to implementing ISO 27001 Annex A 5.7.
Why is ISO 27001 Threat Intelligence important?
The purpose of this control is to provide awareness of the organisation’s threat environment so that the appropriate mitigation actions can be taken.
Taking collective knowledge of threats can lead to a collective response and that response can be based on collective best practice. If we share information we reduce the risk and impact of the emerging threats that are only ever going to increase. We cannot protect against what we do not know. As we start to know more we can increase our protection making for a safer, more secure working environment and protecting vital customer and employee data.
The 3 layers of threat intelligence
There are 3 layers to threat intelligence.
1. Strategic Threat Intelligence
High level information about the threat landscape.
Focus: High-level trends, financial impact, and global risk landscape.
Audience: Senior Management, the Board, and Policy Makers.
ISO 27001 Link: Feeds into Clause 4 (Context of the Organisation) and Clause 6.1 (Risk Assessment) to help leadership make budget and resource decisions.
2. Tactical Threat Intelligence
Intelligence on tools, techniques and attack methodologies
Focus: The “How.” It covers TTPs (Tactics, Techniques, and Procedures) used by attackers.
Audience: IT Managers, System Administrators, and Security Architects.
ISO 27001 Link: Feeds into Annex A 8.8 (Vulnerability Management) and Annex A 5.15 (Access Control) to configure defences against specific attack methods.
3. Operational Threat Intelligence
Intelligence on specific attacks and indicators.
Focus: The “Now.” It covers specific technical details like IOCs (Indicators of Compromise), malicious IP addresses, file hashes, and phishing domains.
Audience: SOC Analysts, Firewalls, and Spam Filters.
ISO 27001 Link: Feeds into Annex A 8.7 (Malware) and Annex A 8.23 (Web Filtering) for immediate blocking.
4. The 3 layers of threat intelligence comparison table
| Layer | Audience | Focus | ISO 27001 Use Case |
| Strategic | Board / C-Suite | Long-term trends & Risk | Informing the ISMS Scope & Budget |
| Tactical | IT Managers | TTPs (Attack Methods) | Tuning Firewall rules & patching priorities |
| Operational | Tech / Software | IOCs (Specific Data) | Blocking bad IPs & antivirus updates |
ISO 27001 Annex A 5.7 Implementation Guidance
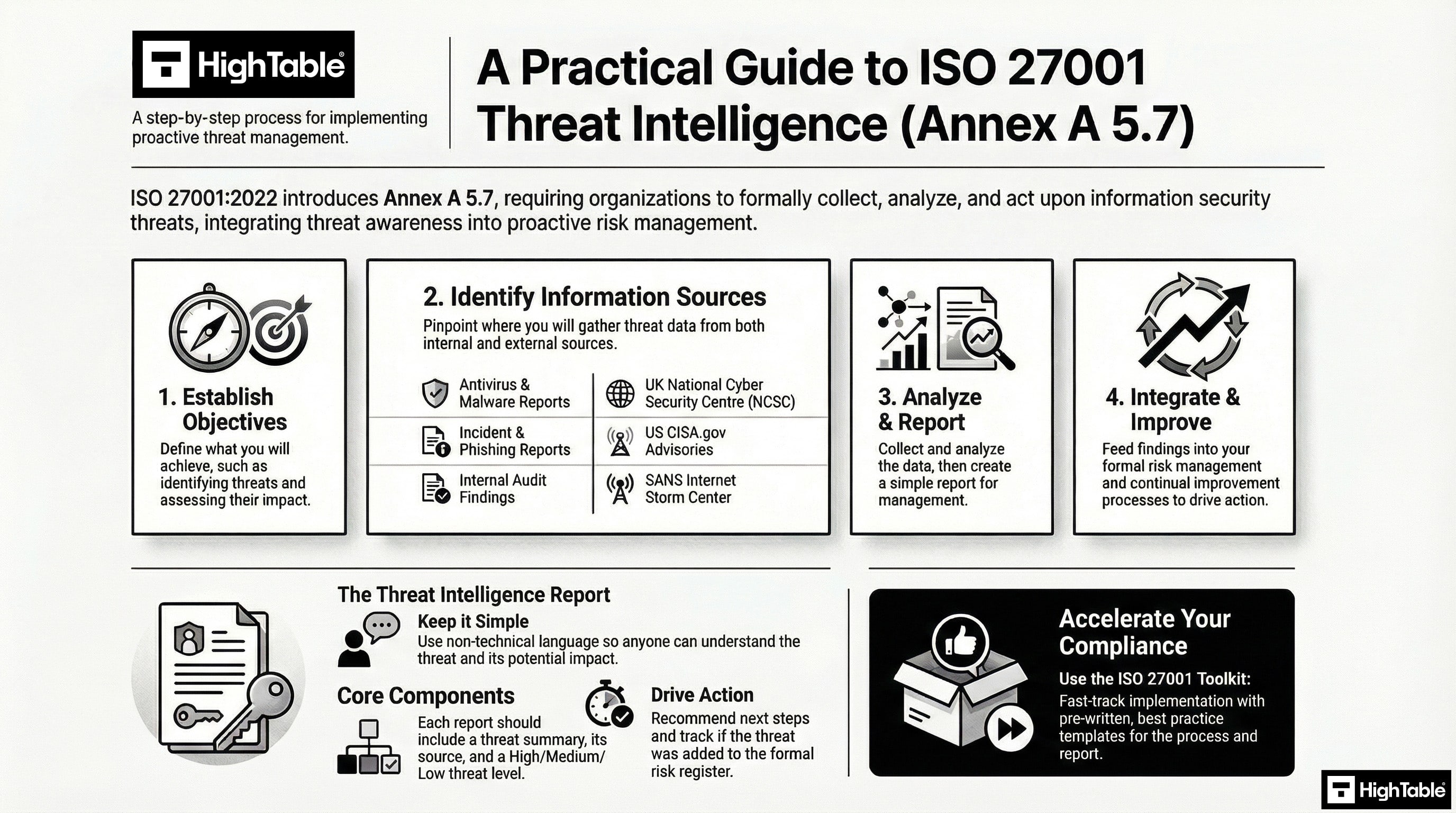
When implementing threat intelligence you are analysing and using information and including it in your risk management process. You are using it as input to inform how you implement and configure technical controls. You are adapting information security tests and techniques based on it.
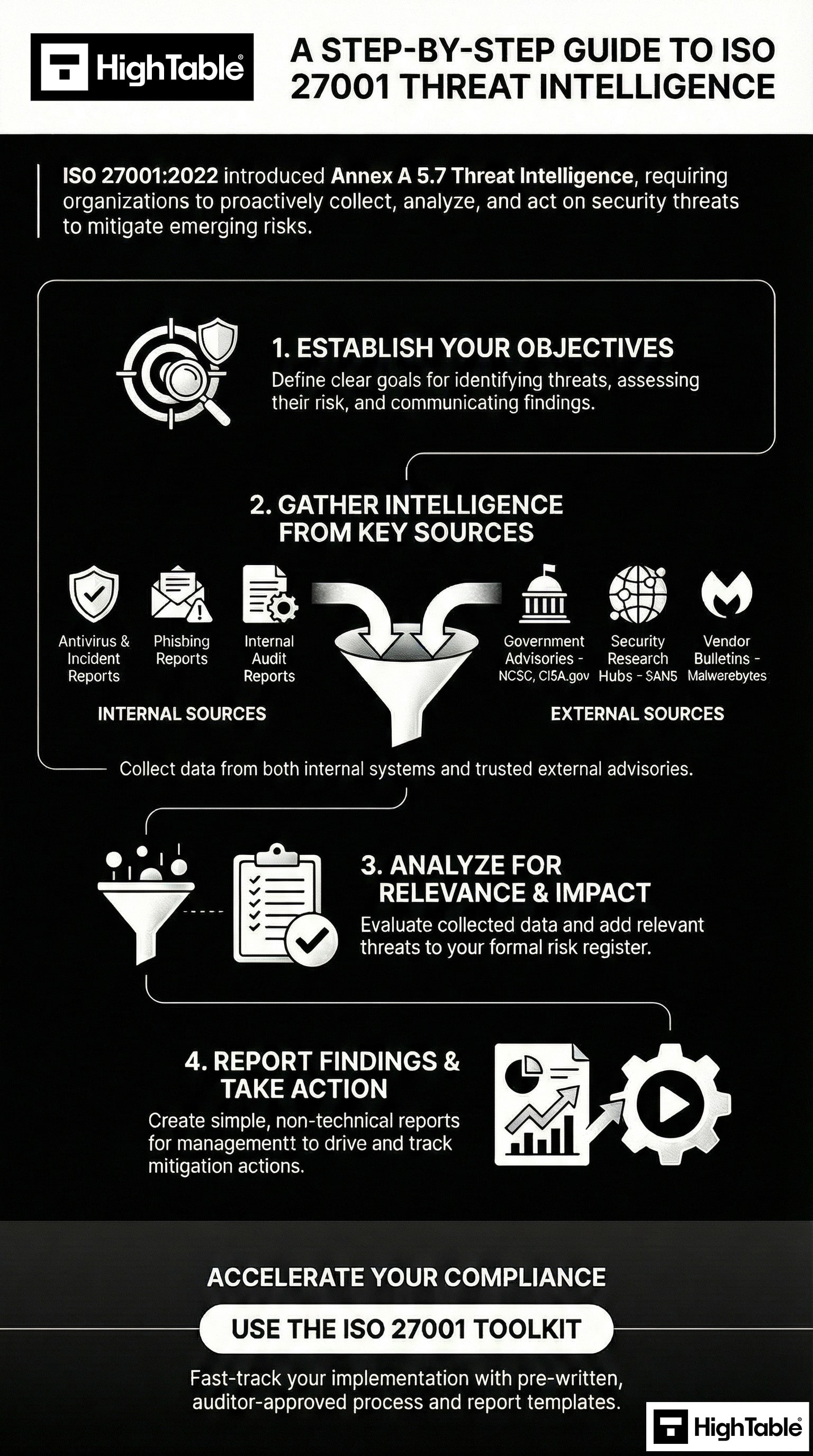
Threat intelligence is used to inform decisions and actions to precent these threats causing harm to the organisation and reduce the impact of such threats. The graphic below outlines the process from objectives to improvement.
You are going to have to ensure that
- objectives for threat intelligence production are established
- internal and external sources of information are identified, selected and vetted where necessary and appropriate
- information is collected from selected sources
- information is then prepared for analysis for example by formatting or translating it
- information is analysed to understand how it relates to you
- communication and sharing of information is done to relevant in people in a way they will understand it
Objectives of the ISO 27001 Threat Intelligence Process
When you write your threat intelligence process it will have objectives. Based on best practice real world experience the following are the objectives of the ISO 27001 Threat Intelligence process:
Identifying Existing and Emerging Threats
Through the use of internal and external data sources existing and emerging threats will be identified. In addition, the use of audit processes such as internal audit, external audit and penetration testing will be used.
Integrating Threat Intelligence into Risk Assessment
Threats will be analysed for relevance to the organisation. Where a relevant threat is identified it will be added to the risk register and managed via the risk management process.
Disseminating Threat Intelligence to Stakeholders
Threat Intelligence will be shared with the Management Review Team as part of the regular structured agenda.
Using Threat Intelligence for Continual Improvement
Threat Intelligence that identifies emerging and existing threats will be managed via the Risk Management Process and any changes or improvements will be managed via the Continual Improvement Process.
I’ve sat in the Auditor’s chair for 30 years. Use the exact system and tools I use to guarantee a pass.

How to implement ISO 27001 Annex A 5.7
Implementing threat intelligence requires a structured approach to identifying, analysing, and mitigating potential security risks before they impact your organisation. By following these ten steps, you will establish a robust framework that aligns with ISO 27001 requirements and enhances your overall security posture.
1. Define Threat Intelligence Objectives and Scope
- Establish the primary goals for the threat intelligence process, such as reducing incident response times or identifying industry-specific attackers.
- Document the scope of intelligence gathering, ensuring it covers tactical, operational, and strategic levels.
- Identify key stakeholders who require intelligence updates, including the IT team, senior management, and the Incident Response Team.
2. Identify and Categorise Information Assets
- Update your Asset Register to include all critical hardware, software, and data repositories that require protection.
- Classify assets based on their value and sensitivity to help prioritise threat monitoring efforts.
- Map dependencies between assets to understand how a threat to one component could impact the wider infrastructure.
3. Select and Validate Intelligence Sources
- Identify a mix of internal sources, such as SIEM logs and incident reports, and external sources, such as commercial feeds or government alerts.
- Evaluate the reliability and relevance of each source to ensure the data provided is accurate and timely.
- Formalise agreements with external providers where necessary, ensuring they meet your organisation’s data privacy standards.
4. Provision Collection and Processing Infrastructure
- Deploy technical tools, such as automated threat intelligence platforms or RSS aggregators, to centralise data collection.
- Configure IAM roles to ensure only authorised personnel can access or modify the threat intelligence feeds.
- Implement data sanitisation processes to remove noise and false positives from the raw data collected.
5. Formalise Analysis and Triage Procedures
- Define the methodology for analysing raw data to identify Trends, Techniques, and Procedures (TTPs) used by threat actors.
- Establish a triage system to categorise threats based on their potential impact and likelihood of occurrence.
- Document the criteria for escalating high-priority threats to the executive level or the security operations centre.
6. Integrate Intelligence with Incident Management
- Update incident response playbooks to include steps for incorporating real-time threat intelligence during an active breach.
- Link Indicators of Compromise (IoCs), such as malicious IP addresses or file hashes, directly into your security monitoring tools.
- Ensure the Incident Response Team has the necessary permissions to act upon intelligence-driven alerts immediately.
7. Implement Technical Safeguards and Mitigations
- Apply proactive controls, such as updating firewall rules or enhancing MFA requirements, based on identified emerging threats.
- Conduct vulnerability scans focused on the specific TTPs identified through your intelligence gathering.
- Ensure that patches for exploited-in-the-wild vulnerabilities are prioritised in the patch management cycle.
8. Distribute Actionable Intelligence Reports
- Create tailored communication templates for different audiences, ensuring technical teams receive tactical data while executives receive strategic overviews.
- Establish secure communication channels for distributing sensitive intelligence, avoiding plaintext emails for high-risk alerts.
- Define the frequency of reporting, ensuring that urgent threats are communicated via out-of-band methods if necessary.
9. Audit and Review Intelligence Effectiveness
- Monitor Key Performance Indicators (KPIs), such as the percentage of threats identified before they caused an incident.
- Conduct periodic audits of the threat intelligence process to ensure compliance with the ISO 27001 Annex A 5.7 control.
- Review the Rules of Engagement (ROE) documents to ensure intelligence gathering activities remain within legal and ethical boundaries.
10. Conduct Management Review and Continual Improvement
- Present a summary of the threat landscape and intelligence performance to the ISMS steering committee.
- Identify opportunities for improving the process, such as investing in better automation or expanding the scope of sources.
- Update the threat intelligence policy and procedures based on feedback and changes in the organisational risk profile.
ISO 27001 Annex A 5.7 Implementation Checklist
| Step | Implementation Requirement | Practical Examples & Technical Controls |
|---|---|---|
| 1 | Establish Threat Intelligence Policy | Define tactical, operational, and strategic objectives within the ISO 27001 Toolkit. |
| 2 | Identify and Validate Sources | Subscribe to diverse feeds including commercial CTI, open-source (OSINT), and industry-specific ISACs. |
| 3 | Update Asset Register Mapping | Cross-reference threat types against specific entries in the central Asset Register to prioritise risks. |
| 4 | Provision Collection Infrastructure | Deploy automated tools such as a Threat Intelligence Platform (TIP) or SIEM integration for data ingestion. |
| 5 | Formalise Analysis Procedures | Document the methodology for identifying adversary Tactics, Techniques, and Procedures (TTPs). |
| 6 | Implement Technical Safeguards | Apply proactive mitigations like updated firewall rules, DNS filtering, and enhanced MFA based on intelligence. |
| 7 | Integrate with Incident Response | Link Indicators of Compromise (IoCs) directly into incident playbooks for rapid containment. |
| 8 | Define IAM and Access Roles | Restrict access to sensitive intelligence data using Role-Based Access Control (RBAC) and strict IAM policies. |
| 9 | Distribute Actionable Reports | Establish secure communication channels to push tactical alerts to IT teams and strategic summaries to the board. |
| 10 | Audit and Review Effectiveness | Conduct periodic reviews of the Rules of Engagement (ROE) and measure KPIs like ‘Time to Detect’. |
Selecting Threat Intelligence Sources: Internal vs. External
There are free sources of threat intelligence information that you can use. These can be internal or external so let us take a look at examples of threat intelligence sources you can use:
Internal Sources of Threat Intelligence
- Anti-Virus and Malware Protection Reports
- Information Security Incident Reports
- Phishing Reports
- Internal Audit Reports
- Helpdesk Tickets
- Log Files
External Sources of Threat Intelligence
- UK National Cyber Security Centre
- CISA.gov – Official website of the U.S. Department of Homeland Security
- SANS™ Internet Storm Center
- Vendor feeds
- Government alerts
- News sites
Comparing Threat Intelligence Sources
| Source Type | Examples | Best For |
| Strategic (External) | CISA Alerts, ENISA Reports | High-level risk planning |
| Tactical (External) | Vendor Feeds (CrowdStrike, etc.) | Blocking specific attacks |
| Internal | Firewall Logs, SIEM Alerts | Detecting active breaches |
| Community | ISACs, Industry Forums | Peer-to-peer warning |
The threat intelligence reporting process
- A Threat Intelligence Report is created.
- The Threat Intelligence Report is shared with The Management Review Team.
- The Threat Intelligence Report is shared at least at the Management Review Team Meeting and if a significant threat is identified.
- Threat Intelligence Reports are kept for at least 12 months.
- Progress of Threat Mitigation is reported via the Risk Management Process and Continual Improvement Process as relevant.
The contents of the threat intelligence report
- Threat Summary: A summary in simple of terms of the threat that can be understood by someone with no technical knowledge.
- Source: The source of the threat. Either a link or a description in words of how the threat was identified.
- Threat Level: Using a simple, easy to understand rating of High / Medium and Low the initial rating is a subjective rating on the potential risk and impact to the organisation. The objective rating will be derived as part of the risk management process.
How to create a threat intelligence process and report in under 10 minutes
Free vs. Paid Sources Table
| Layer | Focus | Free Source Example | Paid Source Example |
| Strategic | High-level trends for C-Suite. | ENISA Threat Landscape, Verizon DBIR. | Gartner Reports. |
| Tactical | Attack methods (TTPs) for IT Admins. | MITRE ATT&CK, Vendor Blogs (CrowdStrike). | Mandiant Advantage. |
| Operational | IP addresses/hashes for Firewalls. | AlienVault OTX, Abuse.ch. | Anomali, Recorded Future. |
How to comply
- Establish and document objectives for threat intelligence production
- Identify, vet, list and document internal and external sources of information
- Collect the information
- Prepare the information for analysis for example by formatting or translating it
- Analyse information to understand how it relates to you
- Communicate and share information to relevant people in a way they will understand it
How to pass the audit of ISO 27001 Annex A 5.7
1. That you are gathering threat intelligence and analysing it
What this means is that you need to show that you have a list of sources of threat intelligence information, have records of collecting and show reports where you have shared and communicated it.
2. That you have taken action as a result of threat intelligence
The process may be straightforward. You may have updated a system, changed a configuration, introduced or removed a tool, had an incident that was managed via the incident management process. What ever the course of action you will have records of action taken and audit trails.
3. That threat intelligence forms part of risk management and operations
Your risk management process will factor in and evidence threat intelligence. Your risk register may take account of threat intelligence and emerging or realised risks.
How to audit ISO 27001 Annex A 5.7
Auditing threat intelligence requires a methodical review of how your organisation identifies, processes, and utilises information regarding external and internal threats. This 10 step audit process ensures that your implementation of Annex A 5.7 is robust, compliant, and integrated into your wider Information Security Management System (ISMS).
1. Review the Threat Intelligence Policy and Objectives
- Verify the existence of a documented policy that defines the objectives for threat intelligence gathering.
- Confirm that the scope is clearly defined: covering tactical, operational, and strategic intelligence requirements.
- Check for evidence of management approval and regular review cycles to ensure the policy remains aligned with the business risk appetite.
2. Inspect Information Source Reliability and Diversity
- Analyse the list of internal and external sources, such as SIEM logs, commercial feeds, and industry sharing groups.
- Evaluate the criteria used to validate the reliability and relevance of these sources to prevent data fatigue or false positives.
- Verify that the organisation does not rely on a single point of failure by ensuring a diverse range of intelligence inputs.
3. Audit Asset Register Synchronisation
- Examine the Asset Register to ensure all critical hardware and software assets are identified for threat monitoring.
- Verify that threat intelligence is mapped against specific assets, allowing for prioritised risk mitigation based on asset value.
- Check for documented dependencies between assets that could be affected by a single threat vector.
4. Examine IAM Roles and Access Permissions
- Inspect the Identity and Access Management (IAM) configurations for the threat intelligence platform.
- Verify that the principle of least privilege is applied: ensuring only authorised analysts can modify intelligence feeds or triage alerts.
- Audit the joiner, mover, and leaver process to ensure access is revoked immediately when roles change or employment terminates.
5. Verify Rules of Engagement (ROE) and Legal Compliance
- Review the Rules of Engagement (ROE) documents to ensure all intelligence collection activities are legal and ethical.
- Confirm that data privacy requirements, such as GDPR or local legislation, are adhered to during the collection of external threat data.
- Check for formal agreements with third-party intelligence providers that outline data ownership and confidentiality.
6. Analyse Threat Triage and Classification Procedures
- Review the methodology for identifying and categorising Trends, Techniques, and Procedures (TTPs) used by threat actors.
- Verify that a formal triage system is in place to prioritise threats based on their potential impact and likelihood.
- Check for documented escalation paths for high-priority threats that require immediate executive or technical intervention.
7. Evaluate Incident Management and IoC Integration
- Sample recent security incidents to confirm if threat intelligence was utilised effectively during the identification and containment phases.
- Verify that Indicators of Compromise (IoCs): such as malicious IPs and file hashes, are integrated into active monitoring and blocking tools.
- Confirm that the Incident Response Team has documented procedures for updating intelligence feeds following a successful mitigation.
8. Audit Technical Safeguards and MFA Implementation
- Verify that Multi-Factor Authentication (MFA) is strictly enforced for all administrative access to threat intelligence systems.
- Inspect the security configuration of the tools used to process intelligence, ensuring they are patched and hardened against attack.
- Review vulnerability scan results for the infrastructure supporting the threat intelligence function.
9. Inspect Intelligence Reporting and Communication Channels
- Review a sample of threat intelligence reports to ensure they are tailored to the appropriate audience: technical, operational, or strategic.
- Verify that secure communication channels are used for distributing sensitive intelligence to prevent interception by threat actors.
- Confirm that reporting frequencies meet the requirements defined in the initial objectives and policy.
10. Confirm Evidence of Continual Improvement and Review
- Examine minutes from management review meetings where threat intelligence performance and the threat landscape were discussed.
- Verify that Key Performance Indicators (KPIs) are tracked, such as the speed of detection or the reduction in successful attacks.
- Check for evidence that the threat intelligence process has been updated based on previous audit findings or changing organisational needs.
The Tools We Use.
100% Audit Success. Zero AI Guesswork.

ISO 27001 Annex A 5.7 Audit Checklist
| Ref | Audit Checkpoint | Evidence & Technical Examples | GRC Platform Verification |
|---|---|---|---|
| 1 | Policy Alignment | Review the Threat Intelligence Policy for strategic, operational, and tactical definitions. | Documented policy linked to Annex A 5.7 control in the ISO 27001 Toolkit. |
| 2 | Source Validation | Inspect the list of internal/external feeds (e.g., MISP, commercial CTI) for relevance and reliability. | Asset/Source register updated with validation dates. |
| 3 | Analysis Methodology | Examine evidence of TTP (Tactics, Techniques, and Procedures) analysis performed on raw data. | Risk assessment logs showing threat actor profiling. |
| 4 | Actionable Output | Sample recent intelligence reports and verify they reached the intended internal stakeholders. | Distribution lists and communication logs within the GRC tool. |
| 5 | Technical Integration | Verify Indicators of Compromise (IoCs) are automatically or manually ingested into SIEM/Firewalls. | Change management tickets for firewall/WAF rule updates. |
| 6 | IAM & RBAC | Audit access permissions for the threat intelligence platform to ensure the principle of least privilege. | User access review logs mapped to intelligence roles. |
| 7 | Incident Response Link | Confirm that threat intelligence was utilised in at least one recent security incident triage. | Incident reports citing specific intelligence feeds. |
| 8 | Legal & Regulatory | Check Rules of Engagement (ROE) for intelligence gathering to ensure GDPR/legal compliance. | Legal review sign-off stored in the compliance folder. |
| 9 | Vulnerability Mapping | Cross-reference intelligence on “exploited-in-the-wild” vulnerabilities with the patch management schedule. | Vulnerability register showing prioritisation based on CTI. |
| 10 | Continuous Review | Verify that the threat landscape is reviewed at least annually by senior management. | Management Review Meeting (MRM) minutes with CTI agenda item. |
Top 3 Mistakes Implementing Threat Intelligence
- 1. You are not collecting or using threat intelligence: This is a new control so one that is easy to overlook. Make sure to follow the control requirements and be able to evidence its operation.
- 2. You rely only on internal threat intelligence: Internal threat intelligence is easy to collect but does not provide for the wider picture. Be sure to include external sources of threat intelligence data.
- 3. Your document and version control is wrong: Keeping your document version control up to date, making sure that version numbers match where used, having a review evidenced in the last 12 months, having documents that have no comments in are all good practices.
The Cyber Threat Intelligence Lifecycle
To satisfy an auditor, you must demonstrate that your threat intelligence is a recursive process, not a one-off subscription. The ISO 27001 Threat Intelligence Lifecycle ensures that data is refined into actionable insight through six distinct stages.
- Direction: Defining the specific technical goals and “Intelligence Requirements” based on your Asset Register.
- Collection: Gathering raw data from internal SIEM logs and external OSINT or commercial feeds.
- Processing: Normalising data into standard formats such as STIX (Structured Threat Information eXpression) for tool interoperability.
- Analysis: Converting processed data into “Actionable Intelligence” by identifying TTPs (Tactics, Techniques, and Procedures).
- Dissemination: Delivering tailored reports via TAXII (Trusted Automated eXchange of Intelligence Information) or secure internal channels.
- Feedback: Reviewing the impact of the intelligence to refine future collection requirements.
Technical Standards for Intelligence Exchange
Modern implementations of Annex A 5.7 rely on standardised languages to share threat data. Using these increases your Information Security Maturity and ensures your tools can “speak” to each other without manual intervention.
| Standard | Full Name | Auditor Context & Purpose |
|---|---|---|
| STIX | Structured Threat Information eXpression | The language used to describe “What” the threat is: including actor motives, TTPs, and campaign patterns. |
| TAXII | Trusted Automated eXchange of Intelligence Information | The transport protocol used to share STIX data: ensuring “How” the data is moved securely between your TIP and SIEM. |
| CybOX | Cyber Observables eXpression | A standardised schema for describing the “Observable” data: such as specific file hashes, registry keys, or HTTP headers. |
Measuring Threat Intelligence Effectiveness (KPIs)
If you cannot measure it, you cannot audit it. Use these Key Performance Indicators to prove the business benefit of your Annex A 5.7 implementation during your certification audit.
| Metric | Target Outcome | Evidence for Auditor |
|---|---|---|
| False Positive Rate | Reduction over time | Refinement logs showing “tuned” feeds based on internal context. |
| Mean Time to Detect (MTTD) | Decrease in detection time | Incident reports showing threats identified by intel before they caused an alert. |
| Actionable Intel Ratio | Increased % of useful alerts | Monthly report showing the % of feeds that resulted in a firewall or WAF rule change. |
ISO 27001 Threat Intelligence Maturity Model
| Maturity Level | Capability Description | Auditor Expectation |
|---|---|---|
| Level 1: Basic | Subscribed to 1-2 free newsletters (e.g., NCSC). | Proof of email subscription. |
| Level 2: Managed | Vetted internal and external sources: monthly reports. | Formal Threat Intelligence Report. |
| Level 3: Automated | Feeds integrated via API into SIEM or TIP. | Automated alert logs and tuning records. |
| Level 4: Advanced | Proactive “Threat Hunting” based on actor TTPs. | Evidence of hunt results and pre-emptive hardening. |
Common Implementation Failure Points
Even with the best tools, threat intelligence can fail if not properly governed. As an auditor, I frequently see these three mistakes that lead to Major Non-Conformities:
- Feed Inundation: Subscribing to too many feeds without a triage process, leading to “Alert Fatigue” where critical threats are missed.
- Lack of Context: Collecting data that has no relevance to your specific technology stack (e.g., monitoring Linux threats when you are a 100% Windows environment).
- The “Fire and Forget” Error: Receiving intelligence but never updating the Risk Treatment Plan or technical controls.
The Threat Intelligence-to-Action Pipeline
To pass an ISO 27001 audit, you must show the “Chain of Action.” Threat intelligence is useless unless it triggers a change in your security controls. The Action Pipeline ensures that every relevant threat is mitigated systematically.
- Ingestion: Automatic or manual collection of data from your vetted source list.
- Relevance Filter: Comparing the threat against your Asset Register (e.g., does this exploit affect the versions of SQL we actually run?).
- Control Adjustment: Updating technical controls such as Web Application Firewalls (WAF), EDR policies, or MFA conditional access rules.
- Risk Documentation: If the threat cannot be immediately patched, it must be recorded as a new risk in the Risk Treatment Plan.
- Operational Validation: Using a vulnerability scanner to verify that the mitigation successfully blocked the threat vector.
Technical Architecture for Threat Intelligence
Organisations reaching Level 3 or 4 maturity typically deploy a specific stack of tools to manage the volume of data associated with Annex A 5.7. This architecture ensures that intelligence is processed at machine speed.
| Tool Category | Purpose in Annex A 5.7 | Example Function |
|---|---|---|
| TIP (Threat Intelligence Platform) | Centralisation & Aggregation | Aggregating 20+ commercial and OSINT feeds into one deduplicated dashboard. |
| SIEM (Security Information & Event Management) | Correlation & Alerting | Matching incoming IoCs (IPs, Hashes) against your real-time traffic logs. |
| SOAR (Security Orchestration & Response) | Automated Mitigation | Automatically blocking an IP address on the firewall the moment it is flagged as “High Risk” by a feed. |
Threat Actor Taxonomy
To produce meaningful intelligence, you must categorise threats based on their origin and motive. An auditor will look for evidence that you distinguish between a generic automated botnet and a targeted campaign against your industry vertical.
| Actor Category | Primary Motive | Technical Focus |
|---|---|---|
| Nation-State (APT) | Espionage & IP Theft. | Long-term persistence, custom malware, and zero-day exploits. |
| Cybercrime Syndicates | Financial Gain. | Ransomware-as-a-Service (RaaS), credential harvesting, and BEC. |
| Hacktivists | Ideology & Disruption. | DDoS attacks, web defacement, and data leaking. |
| Insider Threats | Sabotage or Profit. | Data exfiltration using legitimate credentials (Internal Intel). |
Intelligence for the AI Era
In the current threat landscape, Annex A 5.7 must extend to your AI and LLM infrastructure. Standard threat feeds rarely cover “Adversarial Machine Learning,” making this a high-priority area for modern ISMS management.
- Model Poisoning: Intelligence regarding datasets being manipulated to introduce bias or backdoors into AI models.
- Prompt Injection: Monitoring for emerging “jailbreak” strings used to bypass LLM safety guardrails.
- AI-Generated Phishing: Using tactical intelligence to identify highly-sophisticated, AI-crafted social engineering campaigns.
Stuart Barker’s Auditor “Pro-Tips”
“The secret to a perfect A.5.7 audit is showing the ‘Negative Result’. Show the auditor a threat alert you received, analysed, and rejected because it didn’t fit your Asset Register. That proves your process actually works and you aren’t just a passive consumer of data.” – Stuart Barker, Lead Auditor
Applicability of ISO 27001 Annex A 5.7 across different business models.
| Business Type | Applicability & Interpretation | Examples of Control |
|---|---|---|
| Small Businesses |
Vendor-Led Intelligence. You don’t need a SOC. Your “Threat Intel” is simply listening to your vendors (Microsoft, Apple, Xero) when they tell you to patch. Ignorance is no longer an excuse. |
• Newsletter Subscription: Subscribing to a basic alert feed like the NCSC (UK) or CISA (US) for “Critical” warnings only. • Vendor Notifications: Enabling “Security Alerts” from your primary SaaS providers (e.g., Google Workspace Admin alerts) to know if your industry is being targeted. |
| Tech Startups |
Dependency Scanning. Your biggest threat is likely a vulnerability in an open-source library you use. “Tactical” intelligence means knowing which |
• Automated Feeds: Using tools like GitHub Dependabot or Snyk to pull real-time CVE data directly into your Pull Requests. • Stack-Specific News: Monitoring sources specific to your framework (e.g., “Ruby on Rails Security Mailing List”) rather than generic cyber news. |
| AI Companies |
Adversarial AI Intel. Standard firewalls don’t catch “Prompt Injection” attacks. You need intelligence on how attackers are manipulating models similar to yours. |
• MITRE ATLAS: Monitoring the “Adversarial Threat Landscape for Artificial-Intelligence Systems” (ATLAS) for new attack vectors. • Arxiv Monitoring: Assigning a researcher to review new papers on “Model Poisoning” or “Extraction Attacks” to update your defensive system prompts. |
Fast Track ISO 27001 Annex A 5.7 Compliance with the ISO 27001 Toolkit
| Compliance Factor | SaaS Compliance Platforms | High Table ISO 27001 Toolkit | Audit Evidence Example |
|---|---|---|---|
| Strategy Ownership | Rents access to threat data; if you cancel the subscription, your documented threat reports and source list history vanish. | Permanent Assets: Fully editable Word/Excel Threat Intelligence Processes and Templates you own forever. | A localized “Threat Intelligence Source List” identifying specific government (CISA/NCSC) and vendor alert feeds. |
| Analytic Utility | Attempts to “automate” intelligence via generic feeds that cannot interpret how a global exploit affects your specific business risk. | Governance-First: Provides the framework for your team to triage and analyze threats that actually matter to your stack. | A completed “Threat Intelligence Report” proving that an emerging vulnerability was analyzed and mitigated. |
| Cost Efficiency | Charges an “Intelligence Feed Tax” for automated alerts that are often available for free from government and vendor sources. | One-Off Fee: A single payment covers your threat governance for 3 sources or 30, with zero recurring costs. | Allocating budget to actual security patching or firewall upgrades rather than monthly “SIEM-lite” dashboard fees. |
| Operational Freedom | Mandates rigid reporting formats that often fail to align with agile business models or unique, custom technical stacks. | 100% Agnostic: Procedures adapt to your workflow—from weekly manual reviews to dedicated security team analysis. | The ability to evolve your threat strategy (e.g., adding dark web monitoring) without reconfiguring a rigid SaaS module. |
ISO 27001 Annex A 5.7 Applicable Laws and Related Standards
| Standard / Law | Relevant Section / Requirement | Mapping Context & Implementation Detail |
|---|---|---|
| NIST CSF 2.0 | ID.RA-02, ID.RA-03, DE.AE-02 | Directly maps to the “Threat and Vulnerability” sub-categories. NIST requires using threat intelligence to identify potential targets and anticipate attacker TTPs. |
| SOC2 (Trust Services) | CC3.2, CC7.1, CC7.2 | The “Points of Focus” for Risk Assessment and System Monitoring require the identification of threats. Evidence of external threat feeds supports the “Detection” criteria. |
| NIS2 (EU) | Article 21(2)(e) & (f) | Mandates supply chain security and “vulnerability handling”. Threat intelligence is essential for the proactive reporting requirements under the directive. |
| UK Cyber Security & Resilience Bill | Managed Service Provider (MSP) Reporting | The UK’s evolution of NIS2. Requires MSPs to use intelligence to monitor for systemic risks that could impact the UK’s critical infrastructure. |
| DORA (EU) | Articles 7, 13, and 17 | Financial entities must maintain “detection and response” capabilities. Threat intelligence is a core component of ICT risk management and TLPT (Threat-Led Penetration Testing). |
| GDPR / UK Data (Use and Access) Act 2025 | Article 32 (Security of Processing) | Requires “appropriate technical and organisational measures”. CTI provides the “state of the art” context needed to justify security choices to the ICO or EDPB. |
| EU AI Act & AI Standards | Article 15 (Cybersecurity) | High-risk AI systems must be resilient against “adversarial examples” and “data poisoning”. Threat intelligence must specifically monitor for AI-specific attack vectors. |
| CIRCIA (USA) | 72-Hour Reporting Mandate | Requires critical infrastructure to report incidents. Threat intelligence feeds are the primary mechanism used to determine if an anomaly constitutes a reportable “significant incident”. |
| HIPAA (USA) | § 164.308(a)(1)(ii)(A) | The Security Rule requires Risk Analysis. Threat intelligence identifies the “threats to the confidentiality, integrity, and availability” of ePHI. |
| CCPA / CPRA (California) | Section 1798.100 | Requires “reasonable security procedures”. Failure to ingest threat data regarding known credential stuffing or data exfiltration techniques may be deemed “unreasonable”. |
| EU Product Liability Directive (PLD) | Cybersecurity Flaw Liability | Software providers are strictly liable for flaws. Using threat intelligence proves “due diligence” in identifying and patching vulnerabilities before they are exploited. |
| ECCF (European Cybersecurity Cert) | Harmonised Security Labels | High-assurance labels require products to be tested against current threat landscapes, necessitating a robust Annex A 5.7 process. |
ISO 27001 Annex A 5.7 FAQ
What is ISO 27001 Annex A 5.7?
ISO 27001 Annex A 5.7 is a new organisational control introduced in the 2022 update that requires organisations to collect and analyse information about information security threats to provide situational awareness.
- Focuses on identifying threat actors, their motives, and their methods.
- Requires information to be categorised into strategic, operational, and tactical levels.
- Aims to shift security posture from reactive to proactive.
- Mandates that collected intelligence is used to inform risk assessments and technical controls.
Is threat intelligence mandatory for ISO 27001:2022?
Yes, Annex A 5.7 is mandatory if it is identified as a necessary control within your Statement of Applicability (SoA) following a formal risk assessment.
- Most organisations handling digital data will find this control applicable.
- Auditors expect to see a documented process for how intelligence is gathered.
- Exclusions must be strictly justified in the SoA.
- Compliance is required for all organisations transitioning from the 2013 to the 2022 standard.
What are the three levels of threat intelligence required?
To comply with Annex A 5.7, organisations should ideally process intelligence at three distinct levels: Strategic, Operational, and Tactical.
- Strategic: High-level information about the changing threat landscape (e.g., new regulations or types of threat actors).
- Operational: Specific information about the TTPs (Tactics, Techniques, and Procedures) used by attackers.
- Tactical: Real-time technical indicators of compromise (IoCs), such as malicious IP addresses, URLs, or file hashes.
What are examples of threat intelligence sources?
Organisations can gather threat intelligence from a variety of internal, external, and community-based sources to satisfy ISO 27001 requirements.
- Government advisories such as the NCSC (UK) or CISA (US).
- Industry-specific ISACs (Information Sharing and Analysis Centres).
- Commercial threat intelligence feeds and security vendor reports.
- Open-source intelligence (OSINT) and community forums.
How do auditors check ISO 27001 Annex A 5.7 compliance?
Auditors look for evidence that threat intelligence is not just being collected, but is actually being used to drive security decisions and mitigate risks.
- Verification of subscriptions to relevant threat feeds or advisory lists.
- Documented procedures for the collection and analysis of threat data.
- Evidence of meeting minutes showing threat intelligence was discussed by management.
- Proof of technical changes (e.g., firewall rule updates) made in response to specific intelligence.
What is the difference between threat intelligence and vulnerability management?
The primary difference is that vulnerability management (Annex A 8.8) focuses on internal weaknesses, while threat intelligence (Annex A 5.7) focuses on external threats.
- Threat Intelligence identifies who might attack and how they operate.
- Vulnerability Management identifies the holes in your systems that could be exploited.
- The two controls work together: TI helps prioritise which vulnerabilities to patch first.
- TI is proactive (looking outward), whereas VM is often preventative (looking inward).
Summary: Your ISO 27001 Annex A 5.7 Implementation Roadmap
Further Reading
- How to Implement ISO 27001:2022 Annex A 5.7: Turning Information into Defence
- How to Audit ISO 27001:2022 Annex A 5.7: Threat Intelligence
- ISO 27001:2022 Annex A 5.7 for Small Business: Security Smarts on a Budget
- ISO 27001:2022 Annex A 5.7 for AI Companies: Knowing Your Enemy
- ISO 27001:2022 Annex A 5.7 for Tech Startups: Smart Defense, Not Just Data
Related ISO 27001 Controls
| Related ISO 27001 Control | Stuart Barker’s Auditor Perspective: The Topic Relationship |
|---|---|
| ISO 27001 Annex A 5.7 Implementation Guide | This is your core operational hub. It defines exactly how to collect, analyse, and distribute data to shift your posture from reactive firefighting to proactive situational awareness. |
| ISO 27001 Annex A 8.8 Management of Technical Vulnerabilities | This is the “so what” of threat intelligence. Tactical intelligence identifies which vulnerabilities are being exploited in the wild, allowing you to prioritise patching based on real-world risk rather than just CVSS scores. |
| ISO 27001 Annex A 5.24 Information Security Incident Management | Intelligence provides the context for detection. By integrating threat feeds into your incident process, you can identify malicious patterns faster and reduce the time to containment during an active breach. |
| ISO 27001 Annex A 8.15 Logging | Logs are your primary internal source of threat intelligence. Without robust logging, you cannot perform the trend analysis required to identify internal attack patterns or validate external threat alerts. |
| ISO 27001 Annex A 8.7 Protection Against Malware | Operational intelligence provides the specific Indicators of Compromise (IoCs), such as file hashes and malicious domains, that your malware protection systems need to block emerging threats in real time. |
| ISO 27001 Annex A 8.23 Web Filtering | Intelligence feeds provide the list of known malicious URLs and phishing sites. This control acts as the technical enforcement point for the tactical data collected under the threat intelligence process. |
| ISO 27001 Annex A 5.25 Assessment of Security Events | Threat intelligence acts as the filter here. It helps security teams decide if a suspicious event is a false positive or a legitimate threat based on known attacker methodologies and TTPs. |
| ISO 27001 Annex A 5.28 Collection of Evidence | When an intelligence-led detection leads to a forensic investigation, this control ensures that the indicators and data used to identify the threat are preserved for legal and regulatory requirements. |
| ISO 27001 Annex A 7.5 Protecting Against Physical Threats | Strategic threat intelligence is not just about code. It includes monitoring for physical threats, such as regional instability or social engineering trends, that could impact your physical office locations and staff. |
| The Ultimate ISO 27001 Toolkit | This is the practical execution layer. It provides the templates for threat intelligence reporting and the risk register integration that I, as an auditor, want to see to grant your certification. |
ISO 27001 Annex A 5.7 Mind Map
ISO 27001 Controls and Attribute Values
| Control type | Information security properties | Cybersecurity concepts | Operational capabilities | Security domains |
|---|---|---|---|---|
| Preventive | Confidentiality | Identify | Threat and vulnerability management | Defence |
| Corrective | Integrity | Detect | Resilience | |
| Detective | Availability | Respond |
