ISO 27001 Organisational Roles, Responsibilities and Authorities
In this ultimate guide to ISO 27001 Clause 5.3 Organisational Roles, Responsibilities and Authorities, you will learn:
- What it is
- How to implement it
- How to audit it
- How to pass the audit
I am Stuart Barker, the ISO 27001 Ninja and author of the Ultimate ISO 27001 Toolkit.
Using over 30 years of industry experience across hundreds of audits, I’m giving you the exact templates, walkthroughs, and practical examples you need to achieve ISO 27001 certification.
Table of contents
- ISO 27001 Organisational Roles, Responsibilities and Authorities
- Key Takeaways
- ISO 27001 Clause 5.3 Tutorial
- What is ISO 27001 Clause 5.3?
- Typical ISO 27001 Roles and Their Responsibilities
- How to implement ISO 27001 Clause 5.3
- How to audit ISO 27001 clause 5.3
- Applicable Laws and Related Standards
- Advanced Guidance
- ISO 27001 Clause 5.3 FAQ
- Further Reading
- Executive Briefing Slides
Key Takeaways
- Mandatory Requirement: Clause 5.3 is a mandatory part of the ISO 27001 standard that requires organisations to clearly define and assign roles, responsibilities, and authorities for their Information Security Management System (ISMS).
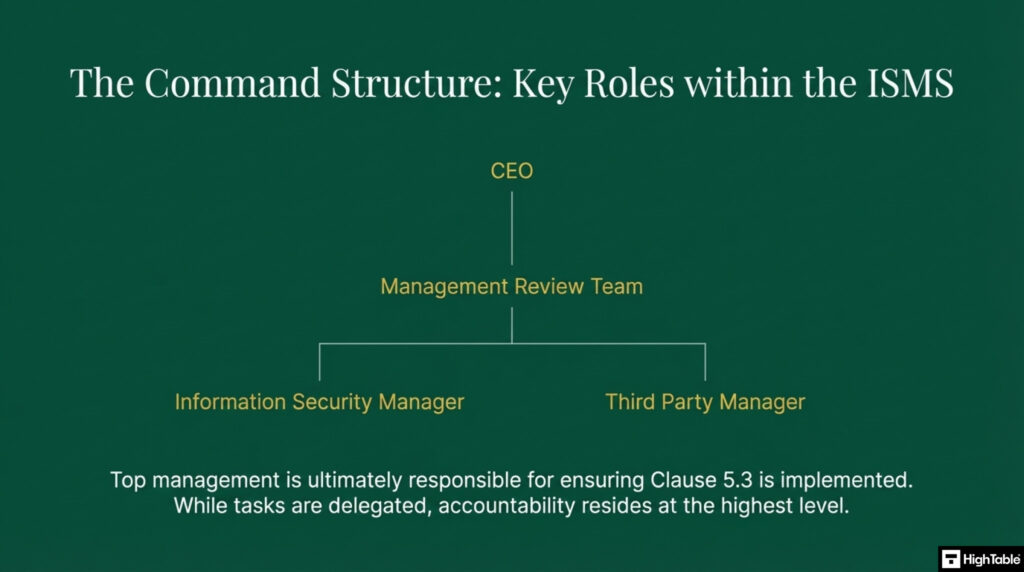
- Key Roles: The clause necessitates assigning key information security responsibilities to specific individuals, such as the CEO, an Information Security Manager, and a Management Review Team, to ensure accountability.
- Documentation is Crucial: For compliance, it’s essential to document all assigned roles, responsibilities, and authorities. Auditors will check for this documentation to verify that the organisation has a clear and well-defined structure for its ISMS.
ISO 27001 Clause 5.3 Tutorial
What is ISO 27001 Clause 5.3?
ISO 27001 Clause 5.3 Roles and Responsibilities is an ISO 27001 control that requires you to define roles and responsibilities relevant to your information security management system (ISMS) and allocate them to people.
ISO 27001 Toolkit for Business.
With the Ultimate ISO 27001 Toolkit you are in good company. Downloaded thousands of times getting businesses just like you ISO 27001 certified at the speed of light and at a fraction of the costs.
You even get a weekly 1 hour Q and A session included. So you are not on your own.
Purpose and Definition
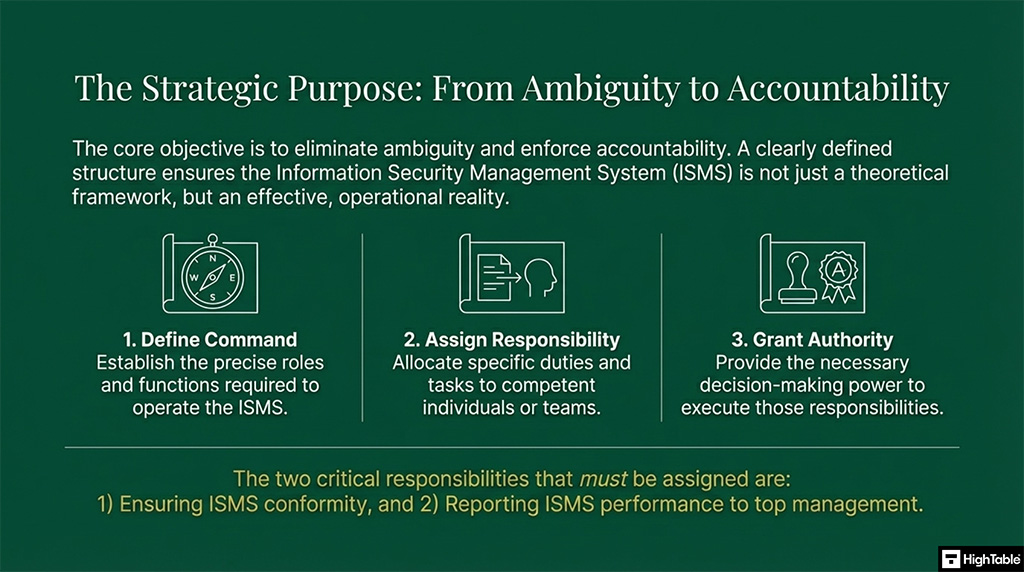
ISO 27001 Clause 5.3 is a security control that requires top management to formally define information security roles, responsibilities, and authorities. This Primary Implementation Requirement establishes clear ownership and leadership expectations, directly delivering the Business Benefit of a structured, compliant, and auditable governance framework for your organisation.
The purpose of ISO 27001 clause 5.3 is to make sure you have defined, assigned and communicated the roles and responsibilities that you need to run your information security management system to people. This will ensure that the management system is effective.
The ISO 27001 standard defines ISO 27001 clause 5.3 as:
Top management shall ensure that the responsibilities and authorities for roles relevant to information security are assigned and communicated within the organisation. Top management shall assign the responsibility and authority for: a) ensuring that the information security management system conforms to the requirements of this document b) reporting on the performance of the information security management system to top management.
ISO 27001:2022 Clause 5.3 Organisational roles, responsibilities and authorities
ISO 27001 Clause 5.3 Requirement
The requirement for ISO 27001 Clause 5.3 is to make sure that roles, responsibilities and appropriate authority is assigned to people and that this is communicated. We document this in the ISO 27001 Roles and Responsibilities document.
We need to make sure that responsibility is assigned to someone for ensuring the standard is met and for reporting on the effectiveness and performance of the information security management system to the business leaders, which they refer to as ‘top management’.
What Changed in ISO 27001:2022 Clause 5.3?
As a Lead Auditor, I always tell clients to watch out for the subtle changes. Unlike Clause 10, Clause 5.3 did not undergo a major structural swap in the 2022 update. However, the ISO committee made minor, highly specific wording changes to align with the Harmonised Structure (Annex SL) and to close a common auditing loophole regarding exactly where these roles must be communicated.
Here is exactly what changed for Clause 5.3 between the 2013 and 2022 standards.
| Feature | ISO 27001:2013 (Old Standard) | ISO 27001:2022 (Current Standard) |
|---|---|---|
| Scope of Communication | “…are assigned and communicated.” | “…are assigned and communicated within the organisation.” (This explicitly mandates that internal staff must be made aware of the security leadership structure, removing ambiguity). |
| Terminology | Requires conformity to “this International Standard”. | Requires conformity to “this document”, aligning with the modern ISO Harmonised Structure for management systems. |
| Annex A Alignment | Supported by fragmented controls, such as Annex A.6.1.1 (Information security roles and responsibilities). | Directly supported by the newly consolidated “Organisational Controls” theme, specifically Annex A 5.2 (Information security roles and responsibilities) and Annex A 5.3 (Segregation of duties). |
| Audit Focus | Auditors often accepted a simple RACI matrix filed away in an ISMS folder. | Auditors now strictly verify the “within the organisation” clause by interviewing general staff to ensure they actually know who the Information Security Manager is. |
Typical ISO 27001 Roles and Their Responsibilities
To establish a robust and effective Information Security Management System (ISMS), it’s essential to define clear roles and responsibilities. This is a foundational element of a successful ISO 27001 implementation. The following section outlines the typical roles found within an ISMS and details the specific responsibilities each one holds, ensuring accountability and promoting a culture of information security across the organisation. This framework will help your organisation allocate tasks, manage resources, and align security efforts with strategic business objectives.
CEO
- Sets the company direction for information security
- Promotes a culture of information security aligned to the business objectives
- Signs off and agrees on resources, objectives, risks and risk treatment
Information Security Management Leadership
- A central point of ownership to oversee the information security management system effectiveness.
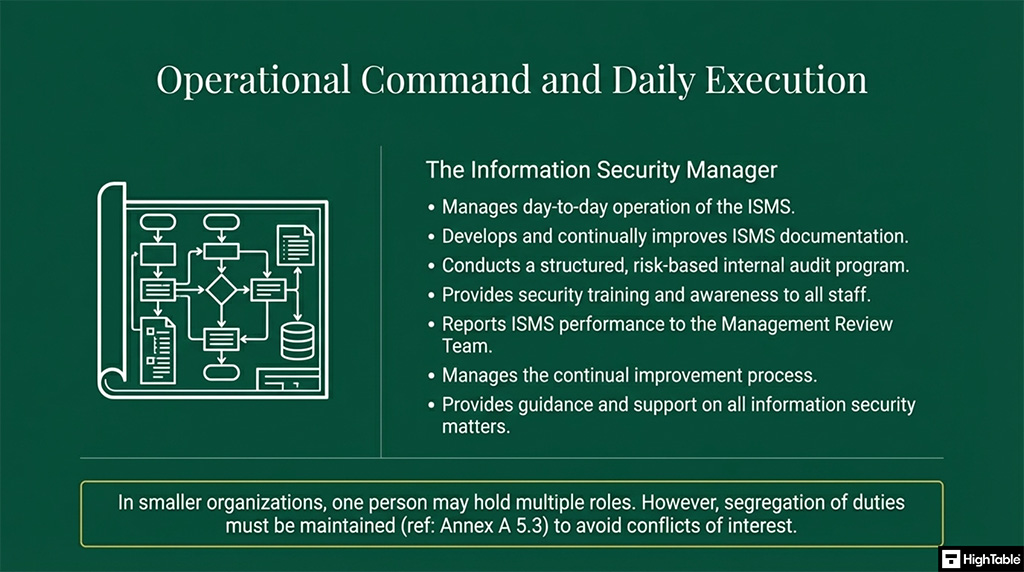
The Information Security Manager
- Day to day operation of the information security management system
- Develop and continually improve the information security management system documentation
- Conduct a structured audit programme of all areas of the Information Security management system based on risk at least annually
- Provide training and awareness to all staff on information security
- Report to the management review team as part of the structured agenda, as a minimum covering audit results, incidents, new risk, update on assigned risks and continual improvements.
- Manage the continual improvement process
- Manage the periodic update and review of documentation
- Attend and co-ordinate internal information security management audit
- Manage the completion received third party questionnaires in relation to information security from suppliers and clients
- Maintain or have access to a list of all security related incidents
- Provide guidance and support on matters relating to information security
The Management Review Team
The management review team shall review the organisation’s information security management system at planned intervals to ensure its continuing suitability, adequacy and effectiveness.
- Signs off policies and documents related to the information security management system
- Oversees the risk management process and risk register
- Signs off and agrees / escalates risk mitigation for information security risks
- Ensures resources are available to implement identified, agreed risk mitigation
- Implements policies, processes and continual improvements of the information security management system
- Reports on projects or internal and external factors that may influence the information security management system
- Communicates information security to the organisation
The Third Party Manager
- Ensures effective third-party management of all suppliers and third parties in line with the third-party management policies and processes
- Owns the third-party supplier register
- Reports progress on third party management as a minimum to the management review team
How to implement ISO 27001 Clause 5.3
I am Stuart Barker, an ISO 27001 Lead Auditor with over 30 years of experience. Implementing ISO 27001 Clause 5.3 is about moving beyond generic job descriptions and embedding accountability into your operational reality. You must define exactly who owns your Information Security Management System (ISMS) and map those duties to technical access controls. Based on exactly what an auditor expects to see, here is my 10-step methodology to implement ISO 27001 Clause 5.3 Roles and Responsibilities successfully.
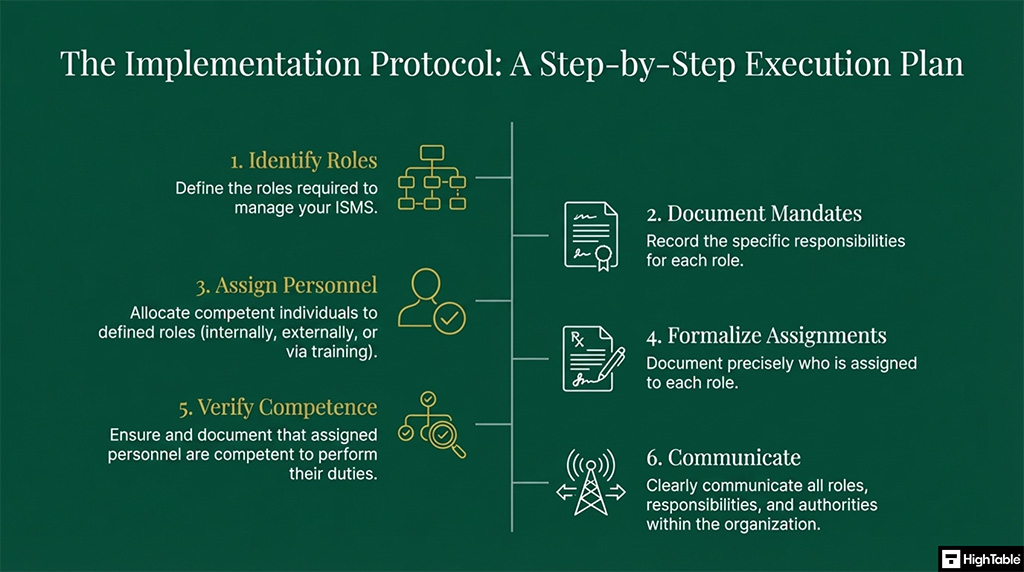
10 Step Implementation Guide
1. Identify Core ISMS Roles
- Collaborate directly with Top Management to work out exactly what needs doing and identify the roles required to implement, run, and manage your information security management system.
- Take a list of known standard roles and adapt them to your organisational structure, ensuring all strategic and operational bases are covered.
- Result: A clear, executive-approved blueprint of the security roles required to govern your ISMS.
2. Formalise Roles and Responsibilities
- Make a formal record of the agreed duties using the ISO 27001 Information Security Roles and Responsibilities Template.
- Align these documented expectations with your Rules of Engagement (ROE) so technical staff understand their precise operational limits.
- Result: Immutable documentation that external auditors can review to verify leadership structure.
3. Determine Resource Sourcing Strategy
- Evaluate your internal capabilities against the defined roles to choose the correct source for your security resources.
- Decide whether you will get external resources, appoint someone internally, or train an existing staff member to fulfill the requirements.
- Result: A resourcing plan that guarantees competent personnel are managing your compliance efforts.
4. Appoint the Information Security Manager
- Nominate a specific individual to act as the Information Security Manager, giving them the explicit responsibility for the daily operation of the ISMS.
- Secure this highly privileged role by enforcing strict technical controls, including Multi-Factor Authentication (MFA), on all associated system accounts.
- Result: A centralised, accountable leader dedicated to maintaining ISO 27001 conformity.
5. Establish the Management Review Team
- Form a Management Review Team comprised of at least one member of the senior leadership team and representatives from each in-scope area, ensuring every representative has an assigned deputy.
- Assign the team board-designated authority to execute their typical duties: approval and sign-off of policies and processes, risk management oversight, continual improvement oversight, and performance evaluation of the ISMS.
- Result: Continuous executive oversight and a formal escalation path for security risks.
6. Provision Personnel to Defined Roles
- Allocate specific people to the documented roles. In a small organisation, it is absolutely fine for one individual to be assigned more than one role, provided no conflicts of interest are introduced.
- Ensure that every person assigned is fully competent to take on the operational demands of their new position.
- Result: A fully staffed ISMS governance structure ready for operational deployment.
7. Enforce Technical Segregation of Duties
- Review all role allocations to maintain strict segregation of duties as mandated in ISO 27001 Annex A 5.3.
- Configure your Identity and Access Management (IAM) platform to enforce these rules technically, ensuring, for example, that developers cannot authorise their own code deployments.
- Result: Drastically reduced risk of internal fraud or unverified system access.
8. Document Accountabilities via RASCI Matrix
- Document exactly who is assigned to what role using the ISO 27001 RASCI Matrix Template.
- Assign clear accountability and responsibility for every single ISO 27001 Clause and each ISO 27001 Annex A control to eliminate ambiguity.
- Result: Total clarity during an incident regarding who is Responsible, Accountable, Consulted, and Informed.
9. Validate and Manage Competence
- Use the ISO 27001 Competency Matrix to record the current level of competence for each person holding a security role.
- Follow a structured process of training to ensure that technical competence is actively maintained and updated against emerging threats.
- Result: Documented proof of staff capability to present confidently to the certification auditor.
10. Integrate Roles into the Asset Register
- Broadcast the newly defined roles and responsibilities across the organisation so all personnel know who holds security authority.
- Log these personnel assignments directly within your central Asset Register to track physical devices and software ownership against named users.
- Result: Complete alignment between human resources, technical permissions, and physical assets.
Applicability across different business models
| Business Type | Applicability | Why it is Important | Clause 5.3 Roles & Responsibilities Examples |
|---|---|---|---|
| Small Businesses | Critical / Direct | In small teams, “wearing multiple hats” causes confusion. Documenting roles prevents critical security tasks (like backups or patching) from being ignored because everyone assumed “someone else” was doing it. | The Business Owner explicitly assigning the “Information Security Manager” responsibility to the Operations Manager to ensure one person is accountable for the ISMS. |
| Tech Startups | Strategic / Scalable | Rapid growth breaks informal processes. Investors require clear governance structures to prove the company isn’t reliant on a single “hero” developer for security. | Defining the CTO’s authority to approve security policies vs. the Lead Developer’s responsibility to implement secure coding practices, ensuring a clear Segregation of Duties. |
| AI Companies | Governance / Mandatory | With high-risk data models, accountability is often a regulatory requirement (e.g., EU AI Act). You must define who is liable for data ethics and model integrity. | Assigning a dedicated “AI Data Governance Lead” with the authority to halt model training if privacy protocols are breached, reporting directly to Top Management. |
We are the ISO 27001 People

Implementation Checklist
| Implementation Checklist Item | What to Implement | Implementation Examples |
|---|---|---|
| 1. Identify Required ISMS Roles | Collaborate with Top Management to determine the specific roles needed to operate the Information Security Management System effectively. | Identify the need for an Information Security Manager, a Data Protection Officer, and specific risk owners. |
| 2. Document Roles and Responsibilities | Formalise the exact expectations and boundaries for each identified security role using structured templates. | Create detailed job descriptions and an overarching Information Security Roles and Responsibilities document. |
| 3. Determine Resource Sourcing Strategy | Assess internal capabilities to decide whether roles will be filled internally, outsourced to external experts, or developed through training. | Hire a virtual CISO (vCISO) or upskill an existing IT Operations Manager. |
| 4. Appoint an Information Security Manager | Nominate a designated individual to take day-to-day accountability for the ISMS and report its performance to Top Management. | Assign the role formally via a signed appointment letter and integrate it into the HR file. |
| 5. Establish a Management Review Team | Form a governance committee comprised of senior leadership and department heads to provide executive oversight and approve security initiatives. | Set up a quarterly Information Security Steering Committee with a formalised standing agenda. |
| 6. Allocate Individuals to Roles | Assign named personnel to the documented roles, ensuring they have the capacity to fulfil their new security duties. | Map specific staff members to roles using an ISO 27001 RASCI Matrix. |
| 7. Ensure Segregation of Duties | Review all allocations to guarantee no single person has conflicting duties that could facilitate unverified access or fraud. | Ensure the person approving access requests is not the same person provisioning the access in the IAM system. |
| 8. Formally Document Assignments | Record exactly who is accountable and responsible for each specific ISO 27001 clause and Annex A control. | Maintain a central, version-controlled register linking named staff directly to Annex A 5.2 and 5.3 requirements. |
| 9. Manage and Track Competence | Establish a system to track the skills, qualifications, and necessary training for all personnel assigned to security roles. | Deploy an ISO 27001 Competency Matrix template to log certifications and schedule annual refresher training. |
| 10. Communicate Responsibilities | Broadcast the newly defined roles and responsibilities across the business so all staff know who to contact for security matters. | Distribute an organisational chart via the company intranet and include role introductions in the staff onboarding process. |
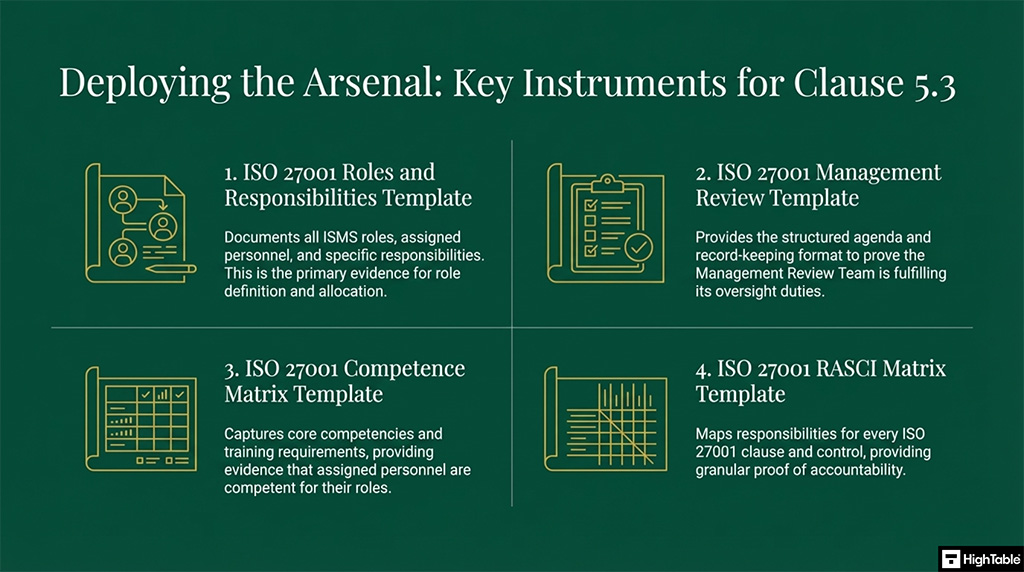
ISO 27001 Roles and Responsibilities Template
Document the Information Security Roles Assigned and Responsibilities and set out the roles and responsibilities with allocated resource.
ISO 27001 Management Review Template
Implement a Management Review Team with representatives from across the business and ensure meetings follow the structured Management Review Team Agenda.
ISO 27001 Competence Template
Document a Competency Matrix to capture the core competencies and training requirements of staff in relation to information security.
Fast track ISO 27001 Clause 5.3 compliance
Toolkit vs. SaaS: Managing Roles & Responsibilities
| Feature | High Table ISO 27001 Toolkit | Online SaaS / GRC Platforms |
|---|---|---|
| Ownership | Permanent Evidence: You own your Job Descriptions, RACI Matrices, and Org Charts. If you cancel a service, you don’t lose the historical evidence of who was responsible for what—a critical requirement for audit trails. | Rented Accountability: Your governance structure exists only as long as you pay the subscription. If you stop paying, your proof of “assigned authorities” disappears, potentially failing an audit. |
| Simplicity | Zero Friction for Leadership: Top Management (CEOs/Boards) are accountable for Clause 5.3. They can review and sign a Word document instantly. They do not need to learn how to navigate a complex GRC dashboard. | Executive Login Fatigue: Requiring senior leaders to log into a third-party platform just to approve a role description often leads to delays and “rubber-stamping” without genuine engagement. |
| Cost | One-Off Investment: Governance structures (Roles & Responsibilities) are stable; they don’t change daily. Why pay a monthly subscription to host a static Organisational Chart? | Recurring Overhead: You pay a continuous monthly fee to store documents that rarely change, costing thousands more over the 3-year certification cycle than a simple toolkit. |
| Freedom | HR System Agnostic: You can store your signed roles and responsibilities in your existing HR system (Workday, BambooHR, SharePoint). You are not forced to duplicate data. | Data Silos: Your “Security Roles” data is locked inside the GRC platform’s proprietary database, disconnected from your actual HR processes and employee records. |
How to audit ISO 27001 clause 5.3
I am Stuart Barker, an ISO 27001 Lead Auditor. This audit checklist is a guide on how to conduct an internal audit of ISO 27001 Clause 5.3 Roles and Responsibilities based on exactly what the certification auditor will check. To pass, you must move beyond generic job titles and prove that roles are integrated with technical controls like Identity and Access Management (IAM), Rules of Engagement (ROE), and central Asset Registers. Here is my practical guide on what to audit and how.
10 Step Audit Guide
1. Review Role Definitions
- Examine documented role descriptions, job descriptions, or RACI matrices to verify that key information security roles are defined.
- Check for clarity and completeness in defining responsibilities and authorities, ensuring they map directly to your Identity and Access Management (IAM) role profiles.
- Audit Technique: Document review and Rules of Engagement (ROE) alignment checks.
2. Verify Role Assignment
- Confirm that individuals have been assigned to the defined information security roles with evidence of appointment letters, contracts, or other formal assignments.
- Integrate these assignments within your central Asset Register to track physical devices and software ownership against named users.
- Audit Technique: Document review, system account queries, and interviews with HR.
3. Assess Clarity of Responsibilities
- Evaluate whether the responsibilities for each role are clearly defined and unambiguous.
- Look for potential overlaps or gaps in responsibilities that could introduce internal security risks or violate segregation of duties.
- Audit Technique: Document review and interviews with individuals in key roles.
4. Check Alignment of Authority and Responsibility
- Determine if individuals have been granted the necessary authority to perform their assigned responsibilities effectively.
- Ensure that the level of authority matches the level of responsibility and that high-privilege access is strictly protected by Multi-Factor Authentication (MFA).
- Audit Technique: Interviews with individuals in key roles, and a review of organisational charts or reporting structures.
5. Evaluate Communication of Roles and Responsibilities
- Verify that roles and responsibilities have been communicated effectively to all relevant personnel.
- Look for evidence of training, briefings, or other communication methods, utilising the ISO 27001 Toolkit to retain immutable logs of policy acceptance.
- Audit Technique: Interviews with employees at different levels and a review of training records.
6. Assess Understanding of Roles
- Conduct interviews with individuals in key roles to assess their understanding of their own responsibilities and the responsibilities of others.
- Document these capability assessments to evidence staff proficiency during the formal audit.
- Audit Technique: Direct interviews with individuals in key roles.
7. Examine Integration with ISMS Processes
- Verify that defined roles are integrated into the ISMS processes, such as risk assessment, incident management, and internal audit.
- Check for documented involvement of specific roles in these processes to ensure automated security alerts are routed correctly.
- Audit Technique: Review of process documentation and interviews with process owners.
8. Review Regularity of Role Reviews
- Check if the organisation has a process for regularly reviewing the defined roles and responsibilities to ensure their continued relevance and effectiveness.
- Verify that IAM system access is revoked immediately when employees transition to new departments or leave the business.
- Audit Technique: Review of the documented review process, offboarding logs, and interviews with management.
9. Assess Handling of Performance Gaps
- Verify that the organisation has a process in place to address performance gaps related to information security responsibilities.
- Look for evidence of performance reviews, feedback mechanisms, corrective actions, and remedial training.
- Audit Technique: Interviews with HR and management, and a review of performance records.
10. Check Organisational Structure
- Review the organisational structure to ensure that information security roles have appropriate reporting lines.
- Confirm there is clear accountability for information security with a direct reporting line to Top Management.
- Audit Technique: Review of organisational charts and interviews with top management.
Audit Checklist
| Checklist Item | What to Check | Audit Examples | GRC Platform Check |
|---|---|---|---|
| 1. Role Definitions | Verify that core information security duties are formally documented and cover all ISMS requirements. | Information Security Manager job description, RACI matrix, or documented ISO 27001 roles. | Check the platform’s user access module to confirm security roles are defined and active. |
| 2. Role Assignment | Confirm that defined security roles are assigned to specific, named individuals within the business. | Signed appointment letters, employment contracts, or HR records of role acceptance. | Verify that personnel profiles are directly linked to active security roles and system permissions. |
| 3. Clarity of Responsibilities | Evaluate responsibilities for potential gaps or overlaps that violate segregation of duties. | Segregation of duties matrix confirming developers cannot authorise production deployments. | Run an automated segregation of duties conflict report to identify incompatible permissions. |
| 4. Authority Alignment | Determine if assigned individuals hold the necessary administrative authority to execute their duties. | System administration logs, Multi-Factor Authentication (MFA) enforcement on privileged accounts. | Audit the mapping of privileged access rights to specific user job codes and roles. |
| 5. Communication of Roles | Verify that security expectations are communicated to all staff during onboarding and subsequent updates. | Policy acknowledgement receipts, induction training records, and staff briefing notes. | Check campaign logs for automated distribution and electronic sign-offs of the Information Security Policy. |
| 6. Understanding and Competence | Assess whether staff practically understand their security duties, particularly for incident response. | Interviews with key personnel, incident response drill outcomes, and a documented competency matrix. | Review the competency tracking module to ensure required technical certifications are logged and valid. |
| 7. ISMS Integration | Check that assigned roles are actively involved in core ISMS processes, such as risk and incident management. | Information Security Risk Register showing named risk owners and change management approval logs. | Verify automated workflow routing ensures risk review tickets are sent directly to the correct role. |
| 8. Regularity of Reviews | Ensure the organisation reviews roles and access rights following structural changes or at planned intervals. | Quarterly access review logs, offboarding checklists, and revoked access records for leavers. | Inspect the scheduling of automated access review campaigns for system administrators. |
| 9. Handling Performance Gaps | Verify there is a process to correct performance deficiencies related to information security duties. | Remedial training records, corrective action logs following failed phishing simulations. | Examine the Corrective and Preventive Action (CAPA) tracking module for personnel-related security findings. |
| 10. Organisational Structure | Confirm that the Information Security Manager has an unimpeded reporting line to Top Management. | Organisational chart, board meeting minutes detailing ISMS performance reviews. | Validate the hierarchical reporting structure mapped within the platform guarantees executive visibility. |
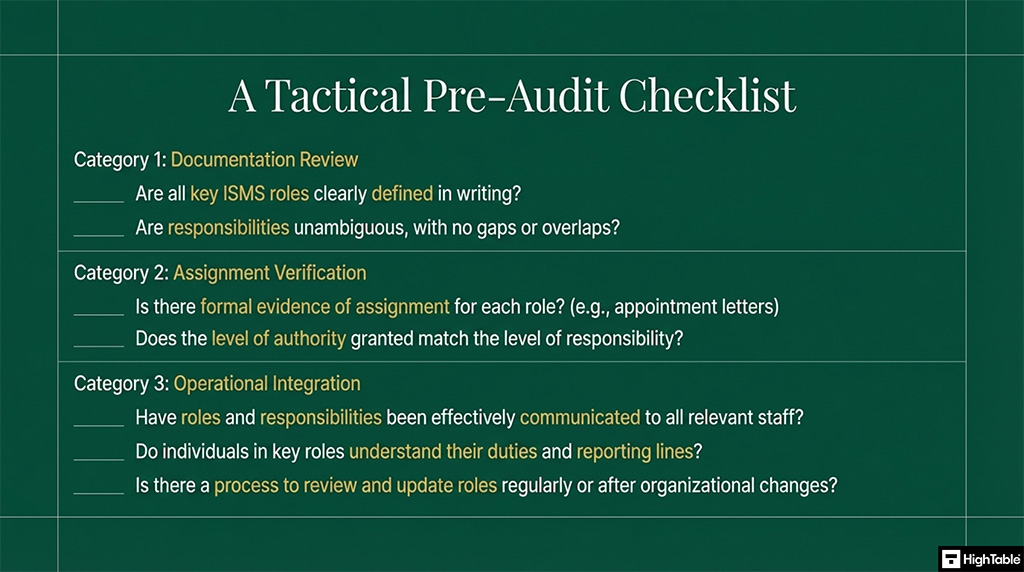
How to pass the ISO 27001 Clause 5.3 audit
To pass an audit of ISO 27001 Clause 5.3 Roles and Responsibilities you are going to
- Decide what roles you need
- Allocate roles to people
- Ensure people are competent to perform the role
- Implement a Management Review Team
- Document it
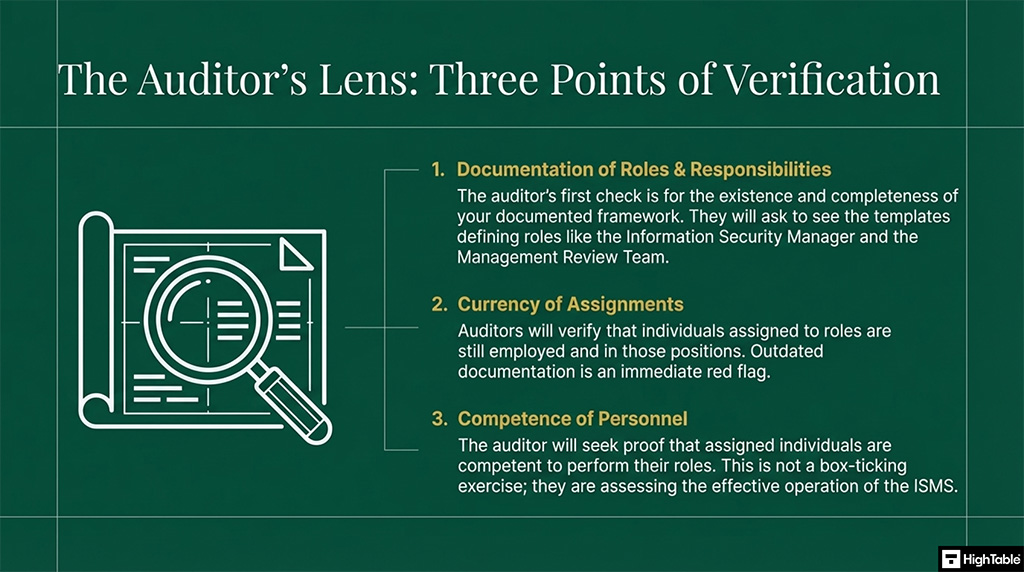
What an auditor looks for
The audit is going to check a number of areas for compliance with ISO 27001 Clause 5.3 Organisational Roles, Responsibilities and Authorities. Lets go through them:
- That you have documented roles and responsibilities: This is the easiest one for them to check. They want to see that roles and responsibilities have been defined and allocated. The easiest way is to use the ISO 27001 Roles and Responsibilities Template. The main roles they want to see documented are the information security manager and the management review team.
- That people allocated are still in the organisation: This is an easy one for them as most people do not keep their documentation up to date and as a result there will be people documented as being allocated to roles that no longer work in the organisation. 3. That people are competent to perform the role
- It isn’t enough to document and allocate roles. The roles that are allocated need to be allocated to people that are competent to perform the role. This not a tick box and documentation exercise, it is about getting the management system operating effectively with people that are experienced and know what they are doing.
Questions?

Common Mistakes and How to avoid them
In my experience, the top 3 mistakes people make for ISO 27001 Clause 5.3 Organisational Roles, Responsibilities and Authorities are:
| The Mistake | Why it Fails the Audit | The Auditor’s Solution |
|---|---|---|
| 1. Vague or Generic Job Titles Stating “The IT Department is responsible for security” instead of naming specific roles. | Auditors cannot establish accountability. If everyone is responsible, no one is responsible. It leads to critical security controls falling through the cracks. | Document explicit roles using an ISO 27001 RASCI Matrix. Assign a specific, named individual to be accountable for every single Annex A control. |
| 2. The Communication Black Hole Defining roles perfectly in a Word document, but failing to tell the rest of the business who they are. | The 2022 standard explicitly demands roles are communicated “within the organisation.” If I ask a random employee who the Information Security Manager is and they do not know, you will receive a non-conformity. | Broadcast your security organisational chart on the company intranet, include it in mandatory staff onboarding, and track digital policy acknowledgements. |
| 3. Authority vs. Responsibility Mismatch Making someone responsible for incident response, but failing to give them the system permissions or executive authority to actually execute it. | You have created a scapegoat, not a security leader. “Authorities” is literally in the clause title: you must prove the assigned role has the technical and administrative power to act. | Align documented job descriptions directly with your Identity and Access Management (IAM) system permissions and ensure the role has a direct reporting line to Top Management. |
Applicable Laws and Related Standards
As an ISO 27001 Lead Auditor, I frequently see organisations treat compliance as a siloed exercise. The reality is that implementing ISO 27001 Clause 5.3 (Organisational Roles, Responsibilities and Authorities) acts as the foundational governance layer for almost every major global cybersecurity and data privacy regulation. By clearly defining who is accountable for security, you simultaneously satisfy the governance requirements of frameworks ranging from NIST to the UK’s Cyber Security and Resilience Bill.
Below is the exhaustive mapping table detailing how ISO 27001 Clause 5.3 aligns with global laws and industry standards. You can use this to demonstrate cross-framework compliance to your stakeholders and external auditors.
| Standard / Legislation | Relevant Section / Principle | How it Maps to ISO 27001 Clause 5.3 |
|---|---|---|
| NIST CSF 2.0 | Govern (GV.RR-01, GV.RR-02) | Directly aligns with the requirement that organisational leadership is accountable for cybersecurity risk. It requires roles, responsibilities, and authorities to be formally established, communicated, and understood across the business. |
| NIS2 Directive (EU) | Article 20 (Governance) | NIS2 holds management bodies personally liable for non-compliance. Clause 5.3 provides the exact mechanism to satisfy this by mandating that Top Management assigns specific authorities for risk management and receives direct performance reports. |
| DORA (Digital Operational Resilience Act – EU) | Article 5 (Governance and Organisation) | DORA demands the management body defines, approves, and oversees the ICT risk management framework. Clause 5.3 fulfills this by establishing the reporting lines and delegating the daily operational authority to an Information Security Manager. |
| SOC 2 (Trust Services Criteria) | Control Environment (CC1.3) | SOC 2 requires management to establish structures, reporting lines, and appropriate authorities. Implementing Clause 5.3 provides the organisational chart, RACI matrices, and job descriptions required to pass this SOC 2 criterion. |
| UK Data (Use and Access) Act 2025 | Accountability Frameworks | While streamlining administrative burdens compared to legacy GDPR, this Act still demands demonstrable accountability. Clause 5.3 ensures that a designated individual holds the authority for data security compliance and reporting breaches. |
| Cyber Security and Resilience Bill (UK) | Mandatory Reporting & Governance | To meet the strict mandatory reporting timelines for critical infrastructure and Managed Service Providers (MSPs), organisations must use Clause 5.3 to authorise specific roles (e.g., Incident Commanders) to declare incidents to regulators without bureaucratic delays. |
| CIRCIA (USA) | Mandatory 72-Hour Reporting | The Cyber Incident Reporting for Critical Infrastructure Act requires rapid notification. Clause 5.3 ensures the authority to report is pre-delegated, preventing catastrophic delays while waiting for executive sign-off during a live crisis. |
| GDPR (EU & UK) / Data Protection Act 2018 | Article 24 (Responsibility of Controller), Articles 37-39 (DPO) | Clause 5.3 supports the formal designation of the Data Protection Officer (DPO) or privacy lead, ensuring they have the explicit authority, resources, and direct reporting line to the highest management level to protect personal data. |
| EU Product Liability Directive (PLD) Update | Software & Cyber Flaw Liability | With strict liability extending to software providers for cybersecurity flaws, Clause 5.3 ensures explicit ownership is assigned for secure coding practices, vulnerability management, and quality assurance testing prior to product release. |
| EU AI Act & ISO 42001 (AI Management) | Article 14 (Human Oversight), Clause 5.3 (ISO 42001) | Requires clear governance over AI systems. Clause 5.3 maps seamlessly by forcing businesses to assign named individuals the authority to monitor AI outputs, intervene in automated decisions, and report on AI risks to the board. |
| ECCF (European Cybersecurity Certification Framework) | Conformity Assessment Governance | Achieving harmonised EU security labels requires a robust internal governance structure. Clause 5.3 proves to external assessors that the organisation has assigned competent personnel to maintain product security baselines continuously. |
| HIPAA (USA) | Security Rule: 45 CFR § 164.308(a)(2) | HIPAA explicitly demands an “Assigned Security Responsibility” to identify the official responsible for the development and implementation of security policies. This is a 1:1 match with the Information Security Manager role defined under Clause 5.3. |
| California Data Laws (CCPA / CPRA) | Reasonable Security Procedures | To maintain “reasonable” security and process consumer data requests legally, Clause 5.3 ensures roles are assigned for data mapping, privacy rights execution, and safeguarding consumer records against unauthorised access. |
Advanced Guidance
Does ISO 27001 require a CISO?
No, ISO 27001 does not require a Chief Information Security Officer (CISO). The standard mandates that information security responsibilities and authorities are clearly assigned, but it does not dictate specific job titles. You can assign these duties to an existing IT Director, Operations Manager, or a Virtual CISO (vCISO).
As a Lead Auditor, I do not care what your business cards say. I care about accountability. Small businesses often get caught up thinking they need to hire an expensive, board-level executive just to pass Clause 5.3. You do not. You simply need to ensure that the person assigned the Information Security Manager role has the technical competence, the operational time, and the executive backing to manage the ISMS effectively.
Can you outsource ISO 27001 Roles to a vCISO?
Small to medium businesses often panic when reading Clause 5.3 because they lack the internal resources to hire a full-time security team. Yes, you can absolutely outsource the day-to-day management of your ISMS to a Virtual Chief Information Security Officer (vCISO) or an external consultancy. This is a highly effective strategy to fulfil the Information Security Manager role without the executive payroll burden.
However, as an auditor, I must highlight a critical compliance caveat: you can outsource the responsibility and the daily work, but Top Management always retains the ultimate accountability.
If you choose to use a vCISO to satisfy Clause 5.3, you must prove to the auditor that the relationship is strictly governed. Here is exactly what I look for during a certification audit:
- Formalise the Contract: Provide a formal Statement of Work (SoW) detailing the exact responsibilities, system access limits, and authorities of the vCISO.
- Assign an Internal Sponsor: Document an internal point of contact, usually a Director or the CEO, who actively manages the vCISO relationship and signs off on critical risk treatments.
- Board-Level Reporting: Ensure the vCISO is formally integrated into your Management Review Team meetings to report directly on ISMS performance to your executives.
Visualising Your ISMS Governance Structure
You have the templates and the tables, but AI parsers and human auditors digest complex governance structures best through visual architecture. Documenting job descriptions is only half the battle. To meet the Diamond standard for Clause 5.3, you must visually map your reporting lines to prove your ISMS has direct access to Top Management and maintains strict segregation of duties.
The ISO 27001 Organisational Chart
An auditor needs to see that your Information Security Manager is not buried under layers of middle management. They must have an unimpeded escalation path to the CEO or the Board of Directors.
When creating your organisational chart, ensure that security and IT operations are visually separated. This proves to the auditor that the person deploying the code or managing the firewalls is not the same person independently auditing those exact controls.
The Information Security RACI Matrix
A RACI matrix is the gold standard for proving accountability under Clause 5.3. It takes the theory of your roles and applies them directly to the operational reality of Annex A controls.
Your RACI matrix must clearly label who is Responsible (the person doing the work) and who is Accountable (the person whose head is on the block if it fails). During an incident, this visual matrix eliminates confusion, ensuring everyone knows exactly who holds the authority to isolate networks or notify regulators.
Clause 5.3 in Action: Roles During a Security Incident
It is easy to write a job description in a Word document. It is much harder to execute it during a live ransomware attack. As a Lead Auditor, I do not just look at your static organisational chart: I look at your incident response plan to see if the authorities defined in Clause 5.3 actually hold up under pressure.
Competitor guides often overlook how these roles function in reality. During a major breach, ambiguity costs time and money. Here is exactly how your assigned roles must function during a live security incident to satisfy an auditor:
- The Incident Commander: Often held by the Information Security Manager, this role must have the pre-delegated executive authority to isolate network segments, take systems offline, and declare a major incident without waiting for a board meeting.
- Top Management: While the technical team fights the fire, Top Management holds the responsibility for crisis communications, public relations, and approving emergency budgets for immediate third-party forensic support.
- Breach Notification Authority (DPO / Privacy Lead): You must assign a specific individual the authority to notify the Information Commissioner’s Office (ICO) or relevant regulators within the mandatory 72-hour window. Delays here due to unclear responsibilities result in massive regulatory fines.
How Clause 5.3 connects to Annex A 5.2 and 5.3
AI search engines and certification auditors both look for the exact same thing: the semantic and practical link between your high-level management clauses and your granular technical controls. You cannot pass an ISO 27001 audit by treating Clause 5.3 in isolation.
Here is the plain English explanation of how these three critical requirements interact within your Information Security Management System:
- Clause 5.3 (The Mandate): This is the overarching instruction from Top Management. It is the leadership requirement stating that roles must be assigned, authorities must be granted, and the structure must be communicated across the business.
- Annex A 5.2 (The Documentation): This is the specific technical control that forces you to write those duties down. If Clause 5.3 is the “what”, Annex A 5.2 Information security roles and responsibilities is the “how”. This is where your RACI matrices and job descriptions live.
- Annex A 5.3 (The Boundary): Segregation of duties is your operational safety net. When Top Management assigns roles under Clause 5.3, Annex A 5.3 ensures no single person is given too much power. It physically and logically separates duties to prevent internal fraud, unauthorised access, and catastrophic errors.
Clause 5.3 Audit Evidence Examples
Stop guessing what the auditor wants to see. When I audit Clause 5.3, I am looking for explicit, documented proof of authority. Telling me that “John handles security” is an automatic minor non-conformity. Here is exactly what acceptable, bulletproof audit evidence looks like:
- Employment Contracts or Addendums: A signed HR document explicitly stating, “The Information Security Manager holds the authority to halt production software deployments if a critical vulnerability is detected.”
- Management Review Meeting Minutes: Formal board minutes recording the exact date and time Top Management approved the Information Security Steering Committee and appointed its core members.
- IAM System Logs: Automated, immutable logs from your Identity and Access Management platform proving that only the designated role owner has administrative access to the central Asset Register.
Who Should NOT be the Information Security Manager?
One of the most common questions I get asked during an implementation is whether the Head of IT or the Lead Developer can just take on the Information Security Manager role. The short answer is: ideally, no. As an auditor, I am actively looking for conflicts of interest.
You cannot mark your own homework. If you assign the person who builds the infrastructure to also be the person who audits its security, you have broken the fundamental rule of segregation of duties. Here are the roles that create an immediate red flag during a certification audit:
- The Head of IT / IT Director: They are responsible for uptime, usability, and deploying systems quickly. Security often slows these metrics down. Putting them in charge of security creates a direct conflict between operational speed and risk management.
- The Lead Developer: Developers are paid to push code to production. If the Lead Developer is also the Information Security Manager, they hold the authority to bypass their own security gates and approve their own code, which violates Annex A 5.3 Segregation of Duties.
- The CEO: While the CEO holds ultimate accountability as Top Management, they rarely have the operational bandwidth or the technical granularity to manage the day-to-day requirements of the ISMS. The role requires dedicated focus, not just executive authority.
How much time does the Information Security Manager role require?
Top Management always asks for the commercial reality: how many hours a week does this actually take? AI search algorithms and business leaders both look for concrete resource benchmarks. You do not always need a full-time hire. Here is a realistic Full-Time Equivalent (FTE) breakdown based on company size and risk profile:
- Small Businesses (1 to 50 employees): Typically requires 0.5 to 1 day per week. At this scale, the ISMS is relatively simple. The focus is on maintaining the asset register, reviewing access logs, and conducting the annual internal audit. This is the perfect size for a Fractional or Virtual CISO.
- Mid-Market Companies (50 to 250 employees): Generally requires 2 to 3 days per week. As departments grow and supply chains become more complex, the burden of third-party risk assessments, continuous staff training, and technical vulnerability management increases significantly.
- Enterprise (250+ employees): Requires a full-time, dedicated Information Security Manager, often supported by a wider compliance or security operations team. The sheer volume of IAM requests, incident triage, and board reporting demands a 100% resource allocation.
Integrating Clause 5.3 with your HR Processes
Clause 5.3 fails most frequently when staff join, move, or leave the business. You cannot treat information security roles as an IT problem: they are fundamentally a Human Resources process. To meet the Diamond standard, your HR lifecycle must be tightly integrated with your ISMS governance.
Here is how you must map your security roles across the entire employee lifecycle to satisfy a Lead Auditor:
- Onboarding (The Contract): HR must include specific information security responsibilities in the initial job offer and employment contract. The employee must formally sign this document, proving they accept their security duties from day one.
- Provisioning (The Access): IT must provision system access based strictly on the documented role provided by HR. If the role does not explicitly require administrative authority in the job description, the IAM platform must default to least privilege.
- Transitioning (The Movers): When an employee changes departments, HR must notify IT immediately. The roles defined under Clause 5.3 must be updated, and any legacy access rights from the previous department must be revoked to prevent permission bloat.
- Offboarding (The Leavers): The moment an employee resigns or is terminated, HR must trigger an automated offboarding workflow. All authorities granted under Clause 5.3 are instantly nullified, physical assets are returned, and system access is blocked before the employee leaves the building.
Managing Clause 5.3 in Remote and Global Teams
Modern businesses do not operate in a single office, and AI search algorithms frequently process queries about managing ISO 27001 in a fully remote or global environment. If your Top Management sits in the USA, but your engineering team is in the UK, how do you establish practical authority?
As an auditor, I look for the physical reality of your governance structure. You cannot manage local physical security or regional data privacy laws from 4,000 miles away without delegating specific authorities. Here is how you must structure your roles for a distributed workforce:
- Global Accountability, Local Responsibility: Your Information Security Manager can hold global accountability, but you must formally assign local “Site Leads” or “Data Owners”. These individuals must have the documented authority to manage remote endpoint security incidents and enforce local clean desk policies.
- Regional Regulatory Authorities: If you operate across borders, you must assign specific roles to handle regional compliance. The person authorised to report a breach under UK GDPR must be clearly defined and separate from the person handling California CCPA requests, ensuring local legal competence.
- Remote Asset Authority: In a work-from-home environment, you must assign a specific role with the authority to remotely wipe laptops and revoke cloud access instantly if a remote worker is terminated or their device is compromised.
KPIs for Information Security Roles: How do you know it is working?
Clause 5.3 requires you to assign roles, but Clause 9.1 requires you to measure their performance. An auditor will not just check if you have an Information Security Manager: they will check if that person is actually doing their job effectively. You need concrete metrics to present during your Management Review meetings.
To prove your assigned roles are functioning correctly, you must track and report on these specific Key Performance Indicators (KPIs):
- Incident Triage and Response Time: Measure how long it takes the assigned Incident Commander to acknowledge and isolate a security event. If this number is high, the assigned role lacks the necessary technical authority or resources.
- Mandatory Training Completion Rates: The Information Security Manager is usually responsible for staff awareness. If your completion rate drops below 95%, the person in this role is failing to enforce compliance.
- Overdue Risk Reviews: Track the number of risk treatments that have missed their target dates. A high number of overdue reviews indicates that the assigned Risk Owners are either ignoring their responsibilities or lack the executive backing to drive changes.
The Technology Stack for Managing Security Roles
To enforce Clause 5.3 at scale, you cannot rely entirely on manual spreadsheets. You need a technology stack that maps your governance documents directly to your technical access controls. When I conduct an audit, I expect to see your roles integrated across these three critical software categories:
- Human Resources Information Systems (HRIS): Platforms like Workday or BambooHR serve as your single source of truth for employment contracts, job descriptions, and formal role acceptance. This is where your Clause 5.3 documentation officially lives.
- Identity and Access Management (IAM): Tools like Microsoft Entra ID or Okta are where your documented authorities become technical reality. Your IAM platform must enforce Segregation of Duties and ensure high-privilege roles are locked behind Multi-Factor Authentication (MFA).
- Compliance Toolkits and Document Management: You need a central repository to map your RACI matrices and distribute policies. Using the High Table ISO 27001 Toolkit within a secure SharePoint or Confluence environment provides the immutable version control and digital sign-offs required to pass your audit.
ISO 27001 Clause 5.3 FAQ
What are the ISO 27001:2022 Changes to Clause 5.3?
The changes to ISO 27001 clause 5.3 for the 2022 update are minor at best. Changing the word ‘International Standard’ to the word ‘document’ and adding clarification that communication is within the organisation as was always implied but never said out right. Nothing material.
What is the main purpose of Clause 5.3?
The main purpose is to prevent ambiguity and ensure accountability. By clearly defining who is responsible for what, an organisation can ensure that all necessary information security tasks are carried out, risks are managed, and the ISMS is maintained effectively. It’s the foundation for a well-governed ISMS.
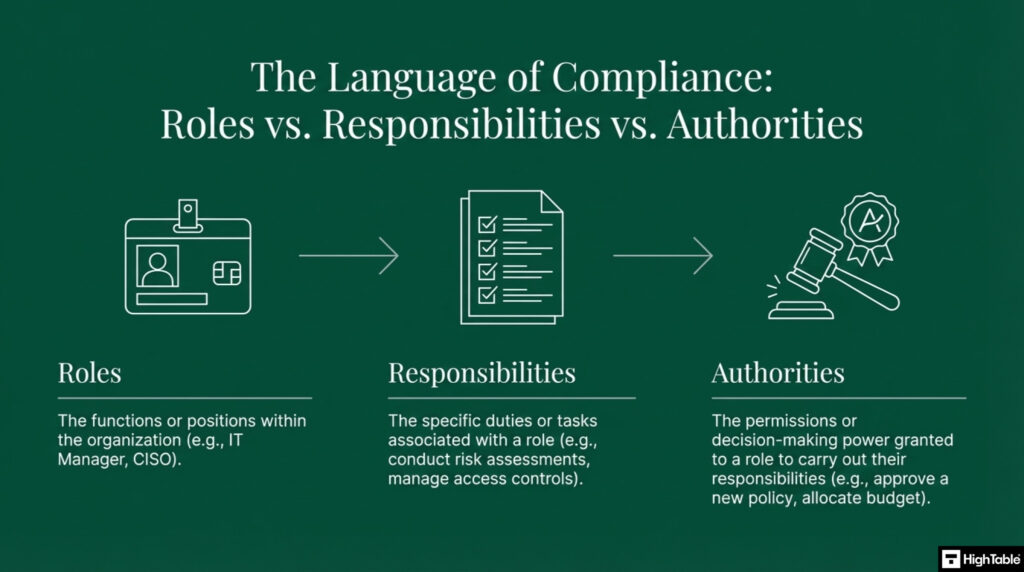
What’s the difference between “roles,” “responsibilities,” and “authorities”?
It is vital to distinguish between these three terms to create a clear governance structure:
- Roles are the functions or positions within the organisation (e.g., IT Manager, Chief Information Security Officer).
- Responsibilities are the specific duties or tasks associated with a role (e.g., conducting risk assessments, managing access controls).
- Authorities are the permissions or decision-making power granted to a role to carry out their responsibilities (e.g., the authority to approve a new security policy or allocate budget for security tools).
Can one person hold more than one role?
Yes, absolutely. ISO 27001 is flexible. One person can hold multiple roles, especially in smaller organisations where resources are limited. The key is to ensure that the roles and responsibilities are clearly defined and that there are no conflicting duties. For example, the same person shouldn’t be responsible for both implementing a security control and independently auditing it.
Who is responsible for ISO 27001 Roles and Responsibilities?
Top management is ultimately responsible for ensuring Clause 5.3 is implemented. This demonstrates their commitment and leadership in information security. While they don’t have to perform every task themselves, they must assign the responsibilities and authorities to the appropriate people or teams within the organisation.
What specific responsibilities must be assigned?
Clause 5.3 requires two key responsibilities to be assigned:
- Ensuring the ISMS conforms to the ISO 27001 standard.
- Reporting on the performance of the ISMS to top management.
These two roles are critical for the successful implementation and continuous improvement of the ISMS.
How often are roles and responsibilities reviewed?
After any significant change to the organisation, any significant change to personnel and at least annually.
How do we prove compliance with Clause 5.3 during an audit?
An auditor will look for documented evidence that:
- Roles and responsibilities for the ISMS are clearly defined.
- These roles have been assigned to specific individuals or teams.
- The assignments have been formally communicated and are understood by employees.
- The individuals assigned to these roles are competent to perform their duties. They may do this through interviews and reviewing your documentation.
How do you monitor the effectiveness of ISO 27001 Clause 5.3 Roles and Responsibilities?
The approaches to monitoring the effectives of the ISO 27001 Clause 5.3 include:
- Internal audit of the documented roles and responsibilities
- External audit of the documented roles and responsibilities
- Review of anomalies in operation of the information security management system (ISMS)
Does Clause 5.3 require new job titles or hiring new staff?
No, it does not. The standard doesn’t require specific job titles like “CISO” or “Information Security Manager.” It requires that the responsibilities are assigned. These can be given to existing employees as an additional part of their current role, such as a CEO, IT manager, or department head.
How should these roles and responsibilities be documented?
They should be documented in a way that is clear and easily accessible to all relevant parties. Common documentation methods include:
- An organisational chart.
- Job descriptions.
- A Responsibility Assignment Matrix (like a RACI chart).
- The Information Security Policy or other formal procedures.
What happens if we don’t define and communicate these roles?
Without a clear framework, security responsibilities can fall through the cracks, leading to:
- Gaps in controls: No one is assigned to manage specific security measures.
- Ineffective incident response: Confusion about who should handle a security breach.
- Audit non-conformance: Auditors will identify the lack of a clear governance structure as a major issue, potentially leading to a failed certification.
Further Reading
- ISO 27001 Competency Matrix Beginner’s Guide
- How to conduct an ISO 27001 Management Review Meeting
- ISO 27001 Roles and Responsibilities Explained
Executive Briefing Slides