ISO 27001 Change Management
In this ultimate guide to ISO 27001 Annex A 8.32 Change Management, you will learn:
- What it is
- How to implement it
- How to audit it
- How to pass the audit
I am Stuart Barker, the ISO 27001 Ninja and author of the Ultimate ISO 27001 Toolkit.
Using over 30 years of industry experience across hundreds of audits, I’m giving you the exact templates, walkthroughs, and practical examples you need to achieve ISO 27001 certification.
Table of contents
- ISO 27001 Change Management
- Key Takeaways
- Core requirements for compliance
- Audit Focus
- What is ISO 27001 Change Management?
- What is ISO 27001 Annex A 8.32?
- Is ISO 27001 Annex A 8.32 Mandatory?
- Why you need ISO 27001 Annex A 8.33
- When you need ISO 27001 Annex A 8.32
- Where you need ISO 27001 Annex A 8.32
- How to write ISO 27001 Annex A 8.32
- Who needs to be involved
- Implementation Guide
- How to implement ISO 27001 Annex A 8.32 Step-by-Step
- How to audit ISO 27001 Annex A 8.32
- ISO 27001 Change Management Policy Template
- Applicability to Small Businesses, Tech Startups, and AI Companies
- Fast-Track ISO 27001 Annex A 8.32 Compliance
- Information security standards that need ISO 27001 Annex A 8.32
- List of relevant ISO 27001:2022 controls
- What are the guidelines for change management?
- Frequently Asked Questions: ISO 27001 Annex A 8.32
- ISO 27002:2022 Control 8.32
- Further Reading
- ISO 27001 Annex A 8.32 Attributes Table
- ISO 27001 Annex A 8.32 Strategic Briefing Slides
Key Takeaways
ISO 27001 Annex A 8.32 mandates that any changes to your information processing facilities (IT systems, networks, software) or the Information Security Management System (ISMS) itself must be managed, not ad-hoc. Its purpose is to stop “good intentions” from causing security incidents, ensuring that every upgrade, patch, or configuration tweak is assessed for risk before it happens.
Core requirements for compliance
- The “Stop and Check” Rule: Before you change a firewall rule, update a server, or migrate to a new cloud provider, you must formally ask: “Will this break our security?”
- Segregation of Duties: The person who writes the code or requests the change should ideally not be the same person who approves it. You need a “second pair of eyes.”
- Fall-back Procedures: You must have a “Plan B.” If the change fails (e.g., the software update crashes the server), you need a documented, tested way to roll back to the previous working state immediately.
- Testing: Changes must be tested in a non-production environment first. “Testing in production” is a major red flag for auditors.
ISO 27001 Toolkit for Business.
With the Ultimate ISO 27001 Toolkit you are in good company. Downloaded thousands of times getting businesses just like you ISO 27001 certified at the speed of light and at a fraction of the costs.
You even get a weekly 1 hour Q and A session included. So you are not on your own.
Audit Focus
- Authorization: Who said “Yes” to this? (Was it the System Owner?)
- Risk Assessment: Did you consider the impact?
- Success Criteria: How did you know the change worked?
What is ISO 27001 Change Management?
ISO 27001 Annex A 8.32 Change Management is an ISO 27001 control that requires you to manage changes to both the information security management system (ISMS) and to the information processing facilities.
In ISO 27001 this is known as ISO 27001:2022 Annex A 8.32 Change Management. It is one of the 93 ISO 27001 Annex A controls.
This rule is a simple idea: You must manage changes in a safe, controlled way.
It means that whenever you plan to change something important about your IT systems, networks, or business processes, you need to check first to see if that change will hurt your security.
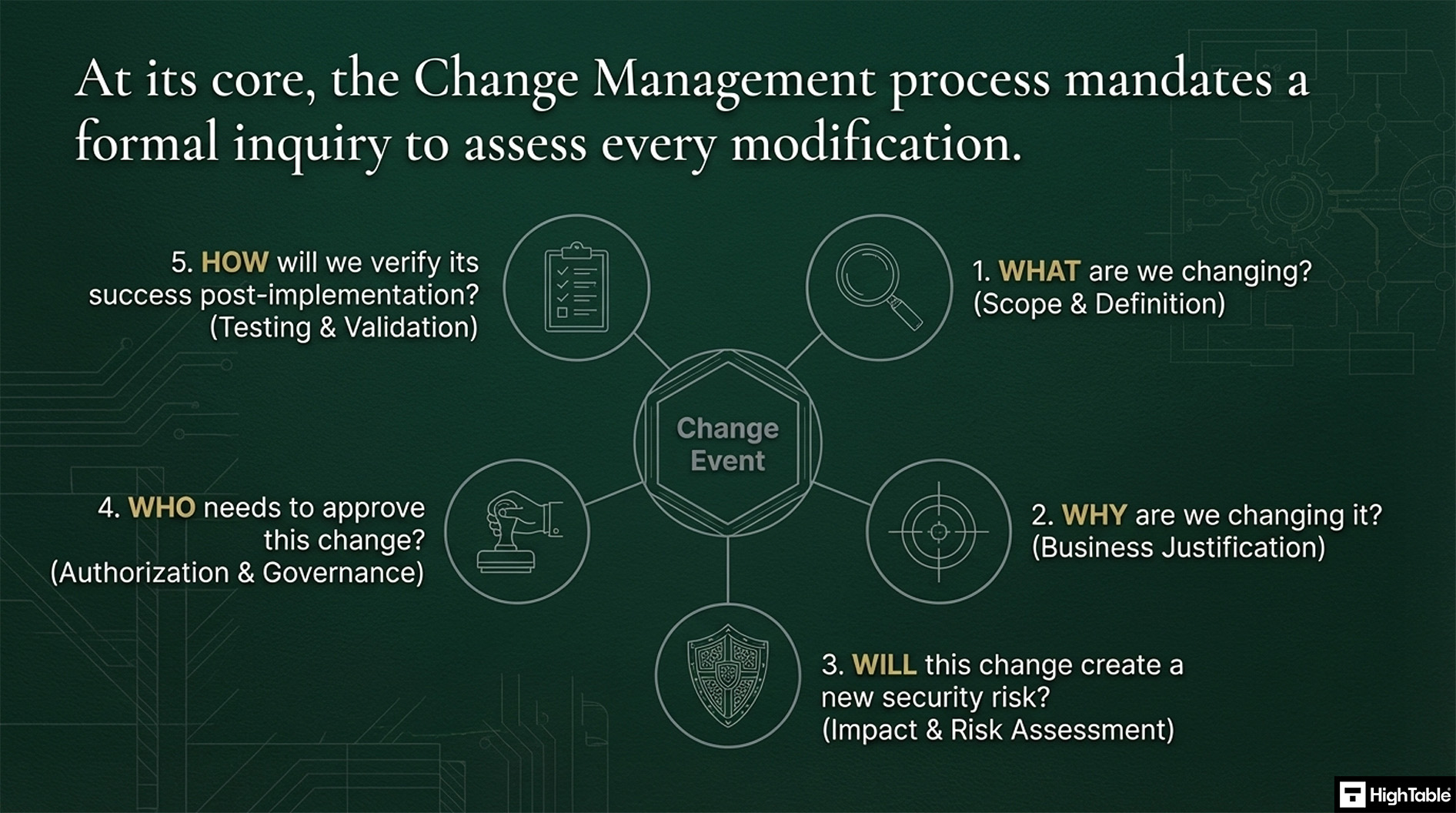
You need a clear plan or process that makes you stop and ask:
- What are we changing?
- Why are we changing it?
- Will this change create a new security risk?
- Who needs to say “yes” before we start?
- How will we check it works afterward?
What is ISO 27001 Annex A 8.32?
ISO 27001 Annex A 8.32 Change Management is a security control that mandates formal procedures for modifying information processing facilities and systems. It ensures that changes are controlled, risk-assessed, and authorized to prevent service disruptions. This requirement guarantees a documented audit trail and preserves the confidentiality, integrity, and availability of data during updates.
The latest version of the ISO 27001 standard is ISO/IEC 27001:2022 (published in October 2022).
In the ISO/IEC 27001:2022 Standard the control is titled “Change Management”.
The ISO 27001 standard defines ISO 27001 Annex A 8.32 as:
Changes to information processing facilities and information systems should be subject to change management procedures.
ISO27001:2022 Annex A 8.32 Change Management
ISO 27001 Annex A 8.32 Purpose
The purpose of ISO 27001 Annex A 8.32 is a preventive control to preserve information security when executing changes.
Is ISO 27001 Annex A 8.32 Mandatory?
ISO 27001 Annex A control 8.32 (Change Management in the 2022 standard) is not automatically mandatory in the same way the clauses in the main body of the standard (clauses 4 through 10) are.
The mandatory part of the standard requires you to consider ISO 27001 Annex A 8.32 and all other Annex A controls, but you have the flexibility to exclude it if it is not applicable to your organisation’s specific risks and context.
Why you need ISO 27001 Annex A 8.33
You need this rule because it helps you keep your information secure and your business running smoothly. Good Change Management helps you:
- Avoid mistakes: Stop small changes from causing big security failures or system crashes.
- Stay secure: Make sure any new system or process is just as safe as the old one – or even safer!
- Be accountable: Know who approved what and when, which is great for audits.
When you need ISO 27001 Annex A 8.32
You should use your Change Management process any time you are changing something that could affect your information security.
- You are installing a new server or a piece of software.
- You are updating your firewall rules.
- You are changing who has access to important customer data.
- You are rolling out a new security policy for your staff.
- You are moving your systems to a different cloud provider.
Where you need ISO 27001 Annex A 8.32
It applies to all parts of your Information Security Management System (ISMS).
Think of it this way: Change Management is the safety belt you wear whenever you change the “driving instructions” (your ISMS). It applies to your IT systems, your policies, your physical office security (like installing a new lock system), and how your staff works.
How to write ISO 27001 Annex A 8.32
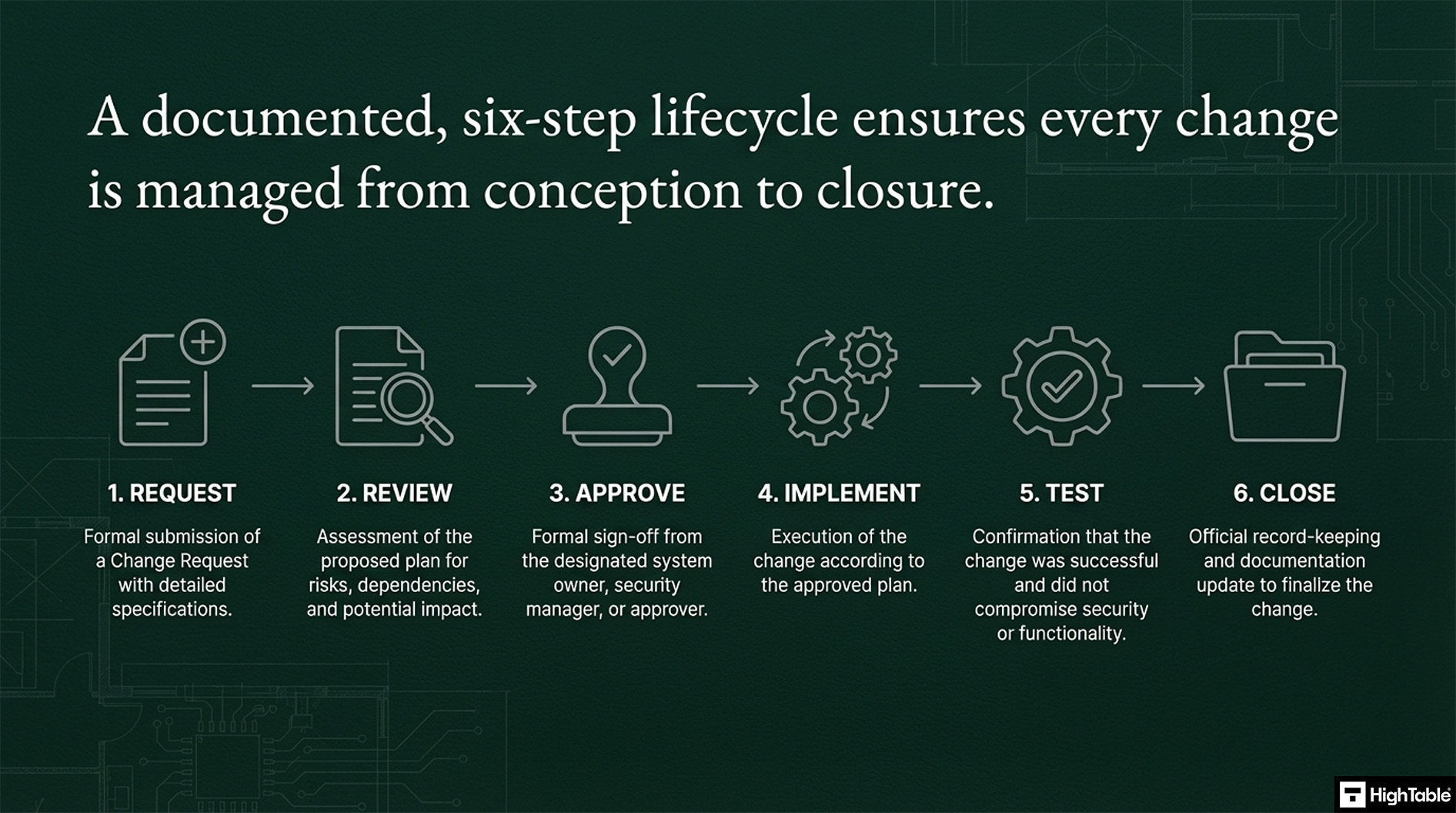
Keep it simple! You need to document a clear path for every change. Your document should cover these main steps:
- Request: You fill out a form (a Change Request) with details.
- Review: You check the plan for risks and confirm it won’t break anything.
- Approve: You get the necessary manager or security person to sign off.
- Implement: You make the change.
- Test: You confirm the change worked and the system is safe.
- Close: You officially record that the change is done and documented.
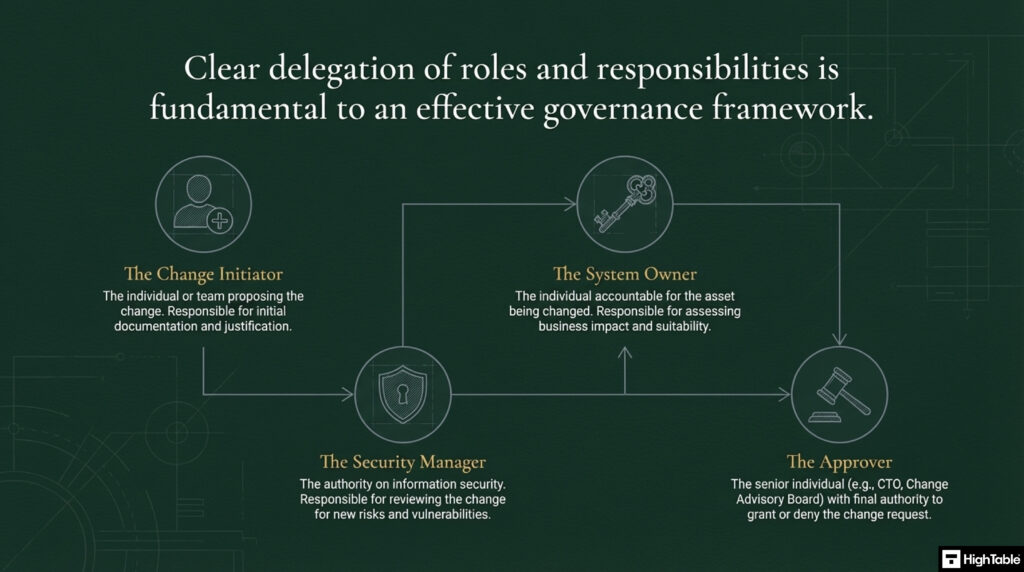
Who needs to be involved
This will change based on how big you are, but generally, you need:
- The Person Making the Change: You write down what you plan to do and why.
- The Owner of the System: You know if the change is a good idea for your specific system.
- The Security Manager: You check the change for any new risks.
- The Approver: A senior person (like a CTO or CEO) who gives the final go.
Implementation Guide
Change management can be a profession in it’s own right and this control is no substitute for that. What we are going to do is manage our changes to the information processing facilities for in-scope products and services and we are going to manage changes to the information security management system.
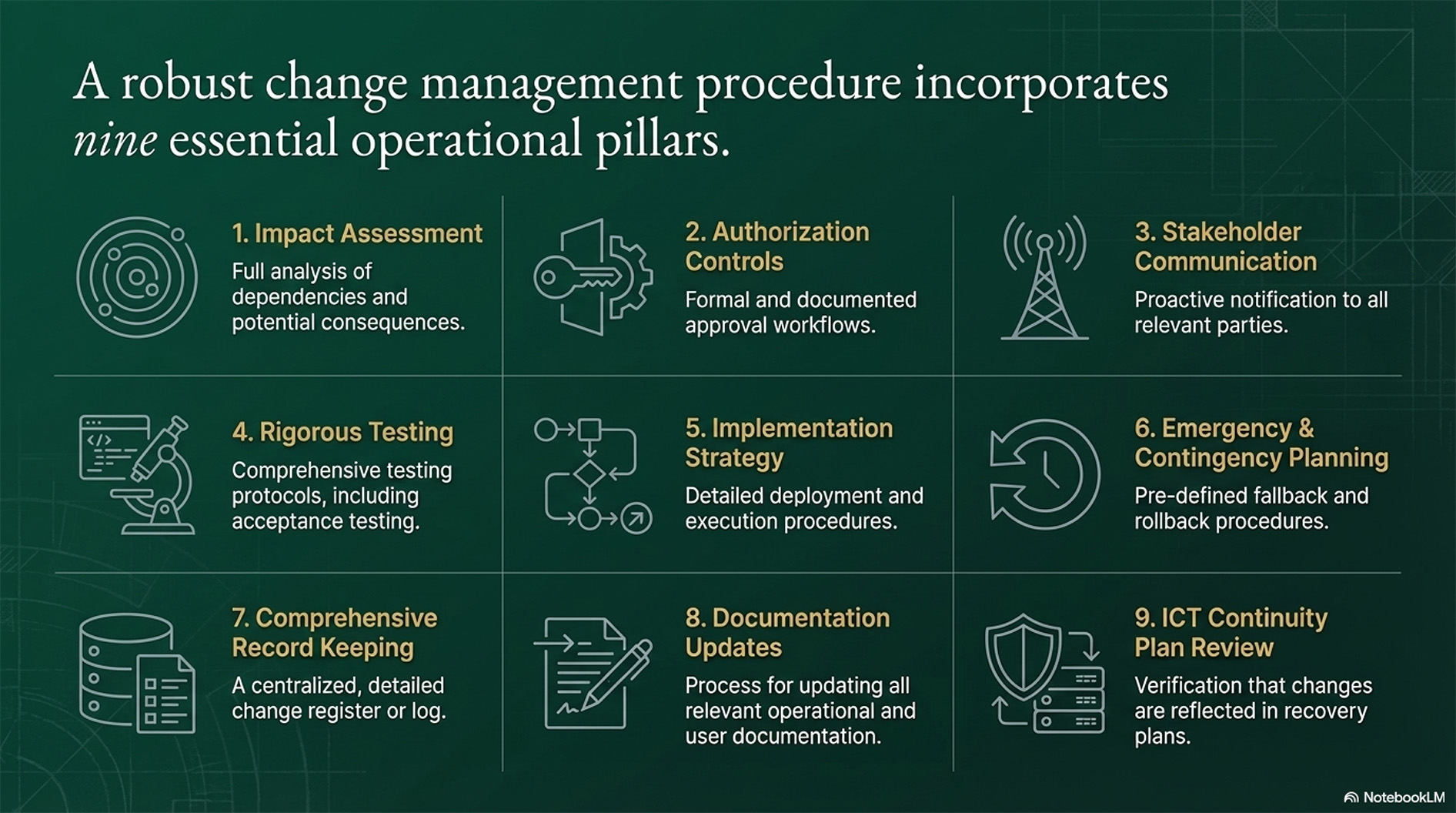
There are nine essential elements of a comprehensive Change Management procedure:
- Impact Assessment: Thoroughly assess and plan for the potential impact of all planned changes, considering all dependencies.
- Authorisation Controls: Implement robust authorisation controls for all proposed changes.
- Stakeholder Communication: Effectively communicate planned changes to all relevant internal and external stakeholders.
- Rigorous Testing: Establish and execute rigorous testing and acceptance testing processes for all changes.
- Implementation Strategy: Define a clear and detailed implementation strategy, including practical deployment procedures.
- Emergency and Contingency Planning: Develop and maintain comprehensive emergency and contingency plans, including a fallback procedure.
- Comprehensive Record Keeping: Maintain detailed records of all changes and related activities.
- Documentation Updates: Review and update all relevant operating documentation and user procedures to reflect the changes.
- ICT Continuity Plan Review: Review and revise all ICT continuity plans, recovery, and response procedures to accommodate the changes.
How to implement ISO 27001 Annex A 8.32 Step-by-Step
In this step by step implementation checklist to ISO 27001 Change Management I show you, based on real world experience and best practice, the best way to implement Annex A 8.32.
Implementing ISO 27001 Annex A 8.32 ensures that changes to information processing facilities and systems are controlled, documented, and risk-assessed. Following these technical steps guarantees system integrity and minimizes the security impact of infrastructure or application updates.
1. Formalize the Change Management Policy and Scope
Define the governance framework for what constitutes a “change” versus “business as usual” maintenance to prevent unauthorized modifications.
- Define criteria for Standard, Normal, and Emergency changes.
- Appoint a Change Advisory Board (CAB) with cross-functional representation.
- Document a clear “Definition of Ready” for production deployments.
2. Establish a Centralized Request for Change (RFC) Workflow
Provision a technical system of record to capture all modification requests, ensuring a complete audit trail for external compliance audits.
- Implement a ticketing system (e.g., Jira Service Management or ServiceNow) to track RFC status.
- Mandate technical descriptions, business justification, and primary stakeholders for every request.
- Assign unique identifiers to every change to link commits in version control to specific RFCs.
3. Conduct Technical Impact and Security Risk Assessments
Analyze the potential security degradation resulting from a change by evaluating dependencies and vulnerability surfaces.
- Perform automated dependency scanning and SAST/DAST testing for software changes.
- Evaluate the impact on existing IAM roles and network segmentation (VLANs/Firewall rules).
- Execute a formal risk assessment for high-impact changes to identify potential availability or confidentiality breaches.
4. Execute Testing, Validation, and Quality Assurance
Validate the technical integrity of the change in a segregated staging environment that mirrors production configurations.
- Execute User Acceptance Testing (UAT) and document sign-offs from system owners.
- Run regression testing to ensure existing security controls remain effective post-implementation.
- Verify that audit logging remains active and correctly formatted during the testing phase.
5. Authorize and Deploy with Rollback Protocols
Transition changes to production using Principle of Least Privilege (PoLP) and a verified “back-out” strategy.
- Formalize a “Point of No Return” and document detailed rollback procedures for failed deployments.
- Provision temporary elevated access (Just-In-Time access) for engineers performing the deployment.
- Schedule deployments during low-impact windows and communicate the maintenance window to stakeholders.
6. Perform Post-Implementation Review (PIR) and Logging
Finalize the change lifecycle by verifying successful implementation and closing the feedback loop for continuous improvement.
- Analyze system logs and performance metrics to confirm the change achieved the intended result.
- Conduct a Post-Implementation Review (PIR) for any change that resulted in an incident or required a rollback.
- Update configuration management databases (CMDB) and technical documentation to reflect the new state.
Guaranteed ISO 27001 Certification

How to audit ISO 27001 Annex A 8.32
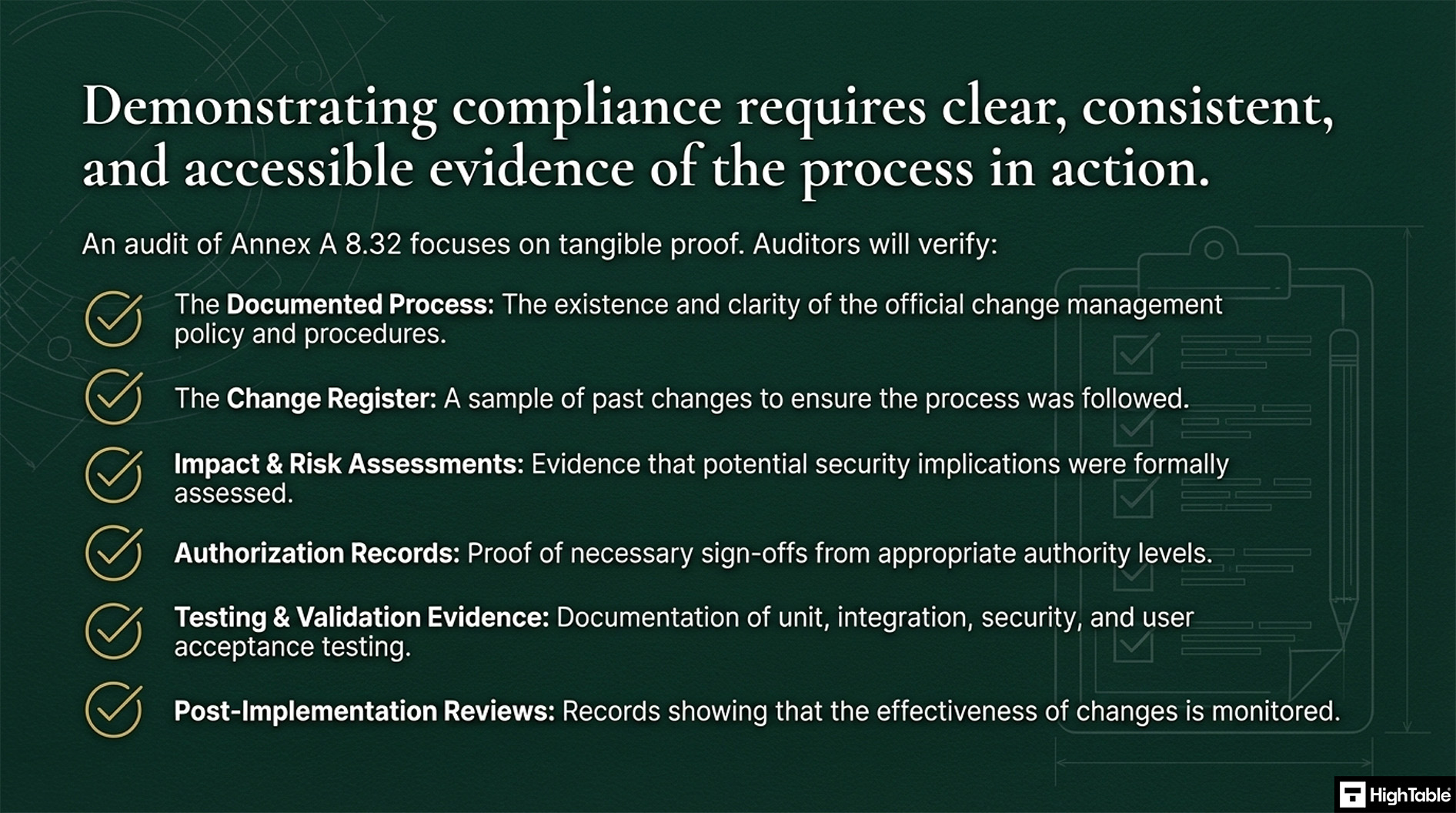
To conduct an internal audit of ISO 27001 Annex A 8.32 Change Management use the following audit checklist which sets out what to audit and how to audit it.
The Ultimate ISO 27001 Change Management Audit Guide
Effective change management is critical for maintaining the integrity of an ISO 27001 compliant Information Security Management System (ISMS). This guide provides a detailed checklist for auditors to evaluate the effectiveness and maturity of change controls.
1. Verify the Change Management Process Documentation
A compliant ISMS must have a clearly defined framework for managing change. Confirm the existence of documented procedures and standardized forms.
- Is there a documented ISO 27001 change management policy?
- Are roles and responsibilities (e.g., Change Advisory Board) clearly defined?
- Do current practices match the documented procedures during a walkthrough?
Professional Implementation Note
Auditors should look for a “Change Management Matrix” that defines what constitutes a ‘Major’, ‘Minor’, or ‘Emergency’ change, as each requires different levels of scrutiny.2. Gather Substantive Evidence of Changes
Verify that the process is actively used and not just “shelf-ware.” Identify recent changes through various ISMS inputs.
- Review internal audit logs and management review minutes for change inclusions.
- Seek evidence that changes were identified through regular risk assessments.
- Cross-reference technical logs with the official Change Log.
Professional Implementation Note
Use “Sampling” to pick 3-5 changes from the last six months. Don’t let the auditee choose the samples for you; pull them directly from the ticketing system or Git logs.3. Assess the Rigor of Impact Assessments
Every change must be evaluated for its potential impact on information security. This is a core requirement of Annex A 8.32.
- Review the risk assessment methodology specifically used for change.
- Ensure relevant stakeholders (Security, IT, and Business Owners) are involved in the process.
Professional Implementation Note
A high-quality impact assessment should include a “Back-out” or “Roll-back” strategy. If a change fails, the organization must be able to restore the previous secure state immediately.4. Check for Formal Authorisations
Unauthorized changes represent a significant breakdown in controls. Audit the approval trail for consistency.
- Walkthrough approval workflows within your management system (e.g., Jira, ServiceNow).
- Confirm that delegation of authority is at the appropriate seniority level.
Professional Implementation Note
Check the date/time stamps of approvals. Approvals that occur after the change was implemented are a major non-conformity.5. Audit the Implementation and Technical Testing
Implementation must be proven through technical evidence of testing. A simple “it works” statement is insufficient.
- Review evidence of unit testing, integration testing, and security testing.
- Verify User Acceptance Testing (UAT) sign-off before production deployment.
Professional Implementation Note
Security testing should include vulnerability scans for any infrastructure changes or static code analysis for application changes.6. Review Communication to Stakeholders
Changes often fail because those affected weren’t informed. Review the communication plan for high-impact changes.
- Check for evidence of regular updates and training sessions.
- Review meeting minutes (Change Advisory Board or Risk Reviews) for inclusion of change notifications.
- Review the communication plan and evidence of regular updates and training.
Professional Implementation Note
Effective communication includes notifying the Service Desk. If users call with issues after a change, the help desk must know exactly what was modified.7. Audit Post-Implementation Reviews (PIR)
The “Monitor and Review” phase confirms that the change achieved its objectives without introducing new risks.
- Examine PIR reports for major changes to identify areas for improvement.
- Verify the success criteria applied to changes were actually measured.
Professional Implementation Note
A PIR shouldn’t just be a tick-box. It should specifically address whether the change caused any unexpected security incidents.8. Review Documented Changes to the ISMS
Ensure that the documentation itself (e.g., Network Diagrams, Asset Registers) was updated to reflect the new state.
- Assess documentation for changes and the subsequent version control of those documents.
Professional Implementation Note
Often, the system is changed but the “Statement of Applicability” or “Asset Register” is forgotten. This discrepancy is a common audit finding.9. Evaluate Integration with Key ISMS Processes
Change management does not exist in a vacuum. It must be integrated with other processes like Incident and Problem Management.
- Assess if changes are triggered by problem management or risk treatment plans.
- Check for consistency and efficiency in how data flows between these processes.
Professional Implementation Note
The Auditor should check the “Emergency Change” process specifically for its integration with Incident Management—this is where security risks are highest.10. Assess Continual Improvement of the Process
Finally, verify that the Change Management process itself is being regularly evaluated for effectiveness.
- Seek evidence of regular reviews and evaluations of the change management framework.
- Verify that necessary adjustments were implemented to address identified weaknesses.
Professional Implementation Note
Look for “Change Success Rate” KPIs. A declining success rate should trigger a formal review within the Continual Improvement program.ISO 27001 Change Management Policy Template
It can be confusing to work out what to include in a change management policy or where to start. An ISO 27001 Policy Template that is pre written and ready to go can save you a lot of heart ache so that is why we have done the heavy lifting with the ISO 27001:2022 Change Management Policy Template.
For a deeper understanding of the change management policy read ISO 27001 Change Management Policy Explained + Template
ISO 27001 Change Management Policy Example
Applicability to Small Businesses, Tech Startups, and AI Companies
Change Management is useful for businesses of all sizes, including small businesses, tech startups, and AI companies. Examples of using this control include:
| Industry Context | Change Scenario (The Trigger) | Security & Compliance Actions (The Control) | Key ISO 8.32 Benefit |
|---|---|---|---|
| Small Business | Migration: Switching email providers (Google Workspace to Microsoft 365). | • Comparison: Verified new settings match or exceed old security rules. • Authorization: Obtained formal sign-off from the CEO prior to migration. | Prevents accidental security degradation during software migration. |
| Tech Startup | Deployment: Pushing a new feature code to the main application server. | • Testing: Ran security scans on code before deployment. • Configuration: Verified firewall rules remain correct. • Validation: Used automated tools to confirm no new vulnerabilities were introduced. | Ensures rapid development does not introduce new attack vectors. |
| AI Company | Data Operations: Introducing a large new dataset for AI model training. | • Due Diligence: Audited data source and screened for sensitive PII. • Protection: Confirmed the new storage location utilizes strong encryption. • Impact Assessment: Evaluated risks associated with data ingestion. | Protects data integrity and prevents privacy violations in AI models. |
Fast-Track ISO 27001 Annex A 8.32 Compliance
For ISO 27001 Annex A 8.32 (Change management), auditors do not require expensive software; they require evidence of control. The High Table Toolkit offers a permanent, simplified governance structure compared to the recurring costs and complexity of SaaS platforms.
| Compliance Factor | SaaS Platform Risk | High Table Toolkit Advantage |
|---|---|---|
| Ownership | Rented Evidence. Your audit trail lives on the vendor’s server. Canceling the subscription often means losing access to historical approval logs, leaving you vulnerable. | Permanent Asset. You receive the Change Management Policy and Request Logs in Word/Excel. You own the files and history forever on your own systems. |
| Simplicity | Over-Engineering. Often forces developers into 15-step automated workflows that cause “tool fatigue” and administrative bottlenecks. | Lean Governance. Uses simple Change Request Forms and Checklists. No training required—just a clear process to document risk assessments and approvals. |
| Cost | Scaling Costs. Pricing often scales per “agent” or “admin,” with premium tiers required just to export compliance reports. | One-Off Fee. A single payment covers the entire governance suite. No monthly subscriptions, no per-seat licensing, and no hidden upgrade fees. |
| Freedom | Vendor Lock-In. Rigid “Change Workflows” force you to adapt your agile or DevOps cycles to fit the tool’s limitations. | Full Flexibility. Fully editable templates allow you to define a rigor (e.g., CAB vs. Weekly Deploy) that matches your specific business speed and tech stack. |
Summary: For Annex A 8.32, the auditor is looking for evidence of control, not a screenshot of a dashboard. The High Table ISO 27001 Toolkit provides the governance framework to document risk assessments, authorisations, and test results simply and effectively. It allows you to satisfy the requirement with verifiable documentation that you own, control, and understand.
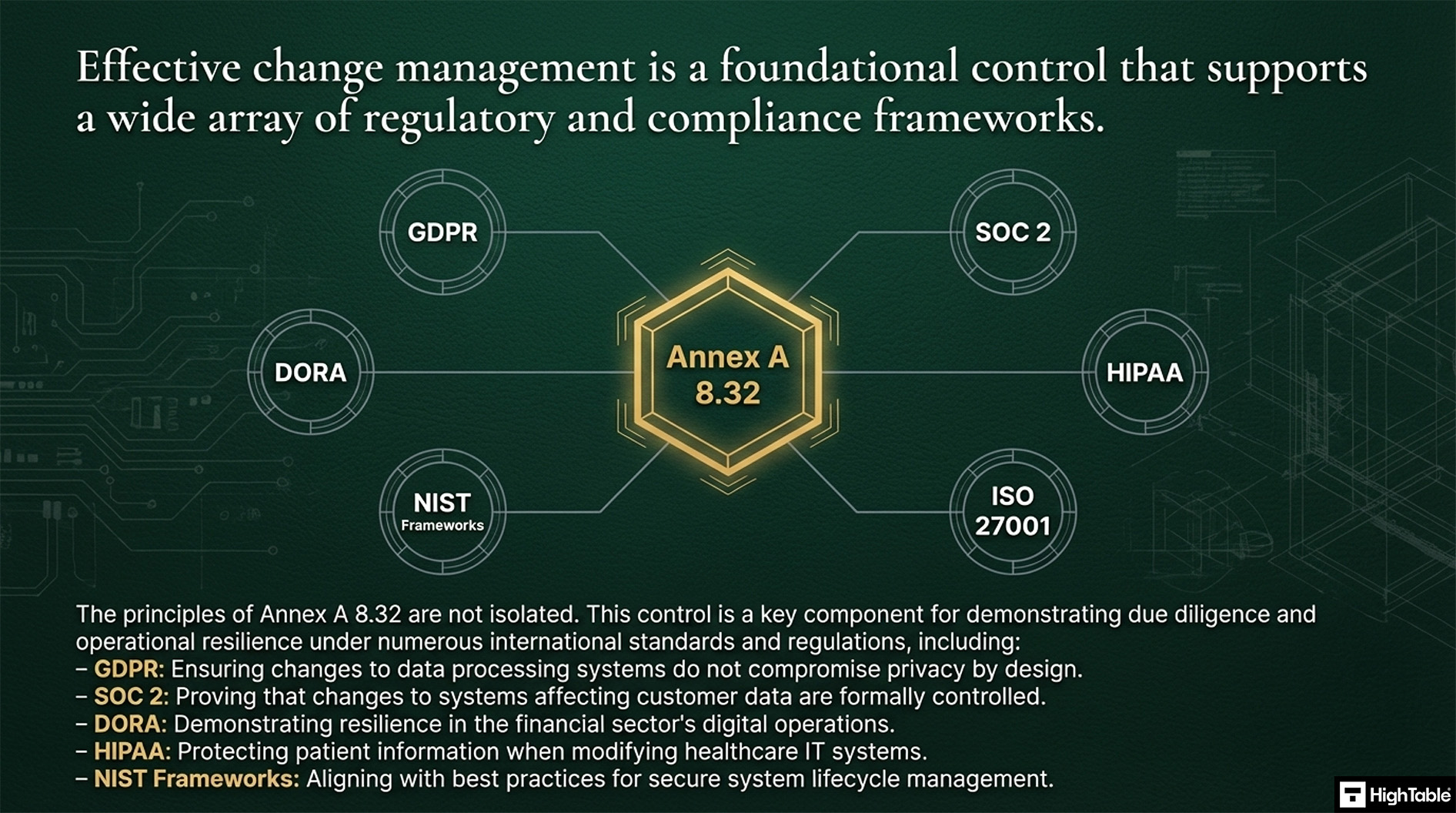
Information security standards that need ISO 27001 Annex A 8.32
Change Management is a key part of ISO 27001, which is an international standard for managing information security. Other standards that need it include:
- GDPR (General Data Protection Regulation)
- CCPA (California Consumer Privacy Act)
- DORA (Digital Operational Resilience Act)
- NIS2 (Network and Information Security (NIS) Directive)
- SOC 2 (Service Organisation Control 2)
- NIST (National Institute of Standards and Technology)
- HIPAA (Health Insurance Portability and Accountability Act)
List of relevant ISO 27001:2022 controls
The ISO 27001:2022 standard has specific controls that relate to change management:
- ISO 27001:2022 Annex A 8.29 Security Testing in Development and Acceptance
- ISO 27001:2022 Annex A 5.25 Assessment And Decision On Information Security Events
- ISO 27001: Annex A 8.34 Protection of Information Systems During Audit Testing
What are the guidelines for change management?
You are going to make sure that you have documented change guidelines. These can be standard guidelines or industry best practice, and you likely already do this today, just make sure that this written down, communicated and available to those that need it.
Included in your change management will be consideration for the following:
- Planning of Change
- Impact Assessment of Change
- Risk Assessment of Change
- Communication of Change
- Test and Acceptance of Change
- Deployment Plans for Changes
- Back out/ rollback Procedures for failed changes
- Records of Change
- Updated Documentation as a result of change
- Updated Business Continuity and Disaster Recovery as a result of change
For change management you need documented roles, responsibilities, processes and procedures.
Change management is not overly complex although it can be a documentation overhead. Be sure to document everything and have evidence of past changes for the auditor to review.
Frequently Asked Questions: ISO 27001 Annex A 8.32
What is the primary requirement of ISO 27001 Annex A 8.32?
ISO 27001 Annex A 8.32 requires that all changes to information processing facilities and information systems are subject to formal change management procedures. The primary goal is to ensure that changes (whether to IT systems, software, or physical security) are planned, tested, and authorized to prevent security incidents or service disruptions.
What will an ISO 27001 auditor ask regarding Change Management?
Auditors will look for a “paper trail” that proves changes were controlled rather than ad-hoc. Be prepared to answer questions such as:
- “Show me the Change Request ticket for your last major server update.”
- “Who authorized this change, and can you prove they have the authority to do so?”
- “Where is the risk assessment that was conducted before this change was implemented?”
- “Did you test this change in a non-production environment first?”
How should Emergency Changes be handled under ISO 27001?
Emergency changes are permitted but must still be controlled and documented, often retrospectively. You cannot simply bypass the process. For compliant emergency changes:
- Fast-Track Approval: Use a designated “Emergency CAB” (Change Advisory Board) or a senior manager for verbal approval.
- Post-Implementation Review: Document the change details and authorization immediately after the incident is resolved.
- Audit Trail: Clearly tag the ticket as “Emergency” to justify why normal testing lead times were shortened.
What are the mandatory steps in an ISO 27001 Change Management process?
While you can adapt the process to your size, a compliant workflow must include these five core stages:
- Request: Formally documenting what needs to change and why (e.g., a Jira ticket).
- Assess: Evaluating the security risks and impact (e.g., “Will this break encryption?”).
- Approve: Getting formal sign-off from a system owner or CAB.
- Implement & Test: Applying the change (ideally in staging first) and verifying success.
- Review/Close: Updating documentation and closing the audit trail.
What documents are required for Annex A 8.32 compliance?
You do not necessarily need a 50-page policy, but you do need evidence of the process. Essential documentation includes:
- Change Management Policy: A high-level document defining who can approve changes and the difference between Standard, Normal, and Emergency changes.
- Change Log/Register: A database (or service desk tool) showing the history of all changes, approvals, and outcomes.
- Rollback Plan: Evidence that you considered how to revert the change if it failed.
Does ISO 27001 Change Management apply to Cloud/SaaS applications?
Yes, it applies to any configuration changes you control within the cloud environment. While you cannot control when a provider like AWS updates their hardware, you are responsible for:
- Changes to your user access rights and roles.
- Modifications to virtual firewall rules or security groups.
- Integrations or APIs you connect to the SaaS platform.
ISO 27002:2022 Control 8.32
ISO 27002 Control 8.32 provides implementation guidance for Change Management.
Further Reading
ISO 27001 Change Management Policy Beginner’s Guide
ISO 27001 Annex A 8.32 Attributes Table
| Control type | Information security properties | Cybersecurity concepts | Operational capabilities | Security domains |
|---|---|---|---|---|
| Preventive | Confidentiality | Protect | Information Protection | Protection |
| Integrity | Application Security | |||
| Availability | System and Network Security |
ISO 27001 Annex A 8.32 Strategic Briefing Slides