ISO 27001 Annex A 8.2 Privileged Access Rights is a security control that mandates the strict restriction and management of administrative accounts to prevent unauthorized system changes. Organizations must implement a formal authorization process, ensure accountability for privileged actions, and strictly enforce the Principle of Least Privilege to mitigate insider threats and data breaches.
In this guide, I will show you exactly how to implement ISO 27001 Annex A 8.2 and ensure you pass your audit. You will get a complete walkthrough of the control, practical implementation examples, and access to the ISO 27001 templates and toolkit that make compliance easy.
I am Stuart Barker, an ISO 27001 Lead Auditor with over 30 years of experience conducting hundreds of audits. I will cut through the jargon to show you exactly what changed in the 2022 update and provide you with plain-English advice to get you certified.
Key Takeaways: ISO 27001 Annex A 8.2 Privileged Access Rights
ISO 27001 Annex A 8.2 requires organizations to strictly manage and restrict privileged access rights. Privileged access (often called “Admin,” “Super User,” or “Root” access) allows users to bypass security controls, install software, and change system configurations. Because these accounts pose the highest risk of misuse or compromise, they must be governed by an authorization process that follows the principles of Least Privilege and Need-to-Know.
Core requirements for compliance include:
- Account Separation: Admins must not use their privileged accounts for day-to-day tasks like checking email or browsing the web. They should have two accounts: a standard one for daily work and a privileged one used only when performing administrative tasks.
- Banning Generic Accounts: You must eliminate generic accounts (e.g.,
admin,support,root). Every privileged action must be traceable to a specific, identifiable individual to ensure accountability. - Formal Authorization: Granting admin rights should never be “informal.” There must be a documented request and approval process that is reviewed at least monthly.
- Segregation of Duty: The person who needs the access should not be the same person who authorizes the access. This prevents “Self-Approval” and reduces the risk of internal fraud.
- Logging and Monitoring: All actions performed using privileged accounts must be logged and reviewed. This creates an audit trail for high-impact changes.
Audit Focus: Auditors will look for “The Admin Bloat”:
- The Count: “Show me a list of everyone with ‘Global Admin’ rights. Why is this list so long?”
- Traceability: “Here is a system change from last Tuesday made by the ‘Administrator’ account. Who exactly was logged in at that time?” (Hint: If you can’t prove who it was, you fail).
- Laptop Admin Rights: One of the most common failures is giving all employees local admin rights on their laptops. Auditors will expect a strong risk-based justification for this.
Account Separation (The Golden Rule):
| Activity | Standard User Account | Privileged (Admin) Account |
|---|---|---|
| Email / Web Browsing | ✓ Allowed | ❌ FORBIDDEN |
| Daily Documentation | ✓ Allowed | ❌ FORBIDDEN |
| Installing Software | ❌ Blocked | ✓ Allowed |
| Modifying Firewall Rules | ❌ Blocked | ✓ Allowed |
Table of Contents
- Key Takeaways: ISO 27001 Annex A 8.2 Privileged Access Rights
- What is ISO 27001 Annex A 8.2?
- ISO 27001 Annex A 8.2 Free Training Video
- ISO 27001 Annex A 8.2 Explainer Video
- ISO 27001 Annex A 8.2 Podcast
- ISO 27001 Annex A 8.2 Implementation Guidance
- How to implement ISO 27001 Annex A 8.2
- Account Separation Table
- ISO 27001 Access Control Policy Template
- How to pass an audit of ISO 27001 Annex A 8.2
- Top 3 ISO 27001 Annex A 8.2 mistakes and how to avoid them
- ISO 27001 Annex A 8.2 FAQ
- Related ISO 27001 Controls
- Applicability of ISO 27001 Annex A 8.2 across different business models.
- Fast Track ISO 27001 Annex A 8.2 Compliance with the ISO 27001 Toolkit
- Further Reading
- ISO 27001 Controls and Attribute Values
- ISO 27001 Annex A 8.2 Strategic Briefing Slides
DO IT YOURSELF ISO 27001
All the templates, tools, support and knowledge you need to do it yourself.

What is ISO 27001 Annex A 8.2?
ISO 27001 Annex A 8.2 Privileged Access Rights is an ISO 27001 control that wants you to make sure you have controls in place to manage privileged access rights.
There are users that will be granted privileged access such as administer (admin) accounts, super user accounts, global admin accounts and even service accounts.
ISO 27001 Privileged Access Rights is the control of those accounts. This ISO 27001 annex a control sets out the requirement to restrict access to those accounts and to properly manage them.
In ISO 27001 this is known as ISO27001:2022 Clause 8.2 Privileged Access Rights.
It is important because these accounts have the ability to gain unlimited access and make unlimited changes and they need to be carefully considered and controlled to protect against misuse and compromise.
ISO 27001 Annex A 8.2 Purpose
The purpose of ISO 27001 Annex A 8.2 Privileged Access Rights is to ensure only authorised users, software components and services are provided with privileged access rights.
ISO 27001 Annex A 8.2 Definition
The ISO 27001 standard defines ISO 27001 Annex A 8.2 Privileged Access Rights as:
The allocation and use of privileged access rights should be restricted and managed.
ISO 27001:2022 Annex A 8.2 Privileged Access Rights
ISO 27001 Annex A 8.2 Free Training Video
In the video ISO 27001 Privileged Access Rights Explained – ISO27001:2022 Annex A 8.2 I show you how to implement it and how to pass the audit.
ISO 27001 Annex A 8.2 Explainer Video
In this beginner’s guide to ISO 27001 Annex A 8.2 Privileged Access Rights, ISO 27001 Lead Auditor Stuart Barker and his team talk you through what it is, how to implement in and how to pass the audit.
ISO 27001 Annex A 8.2 Podcast
In this episode: Lead Auditor Stuart Barker and team do a deep dive into the ISO 27001 Annex A 8.2 Privileged Access Rights. The podcast explores what it is, why it is important and the path to compliance.
ISO 27001 Annex A 8.2 Implementation Guidance
Now let me share with you some best practice when it comes to implementation.
General Guidance
Privileged access is the access that people, software or services have that allows them to do things that normal users cannot do and that could cause the most harm. This level of access is used to manage and configure systems and to allow people to perform administrative tasks. We need people to have this level of access but we do not want everyone to have it. The risk of granting this level of access to someone that doesn’t know what to do with it or should not have it is that they could break something, stop something working or carry out activities that are, shall we say, bad.
Implement a Topic Specific Policy
Your starting point for this control is to implement a topic specific policy on access control and include in that policy your approach to privilege access. The ISO 27001 Access Control Policy Template is already written for you and ready to go and includes a great free Access Control Policy Example PDF.
Implement an authorisation process
An authorisation process is required for all requests for access to organisational assets. Implement a process of authorisation that separates those requiring access from those that grant it. Keep a record of all accounts with privilege access. Consider placing time limits on their use or allocating expiry dates.
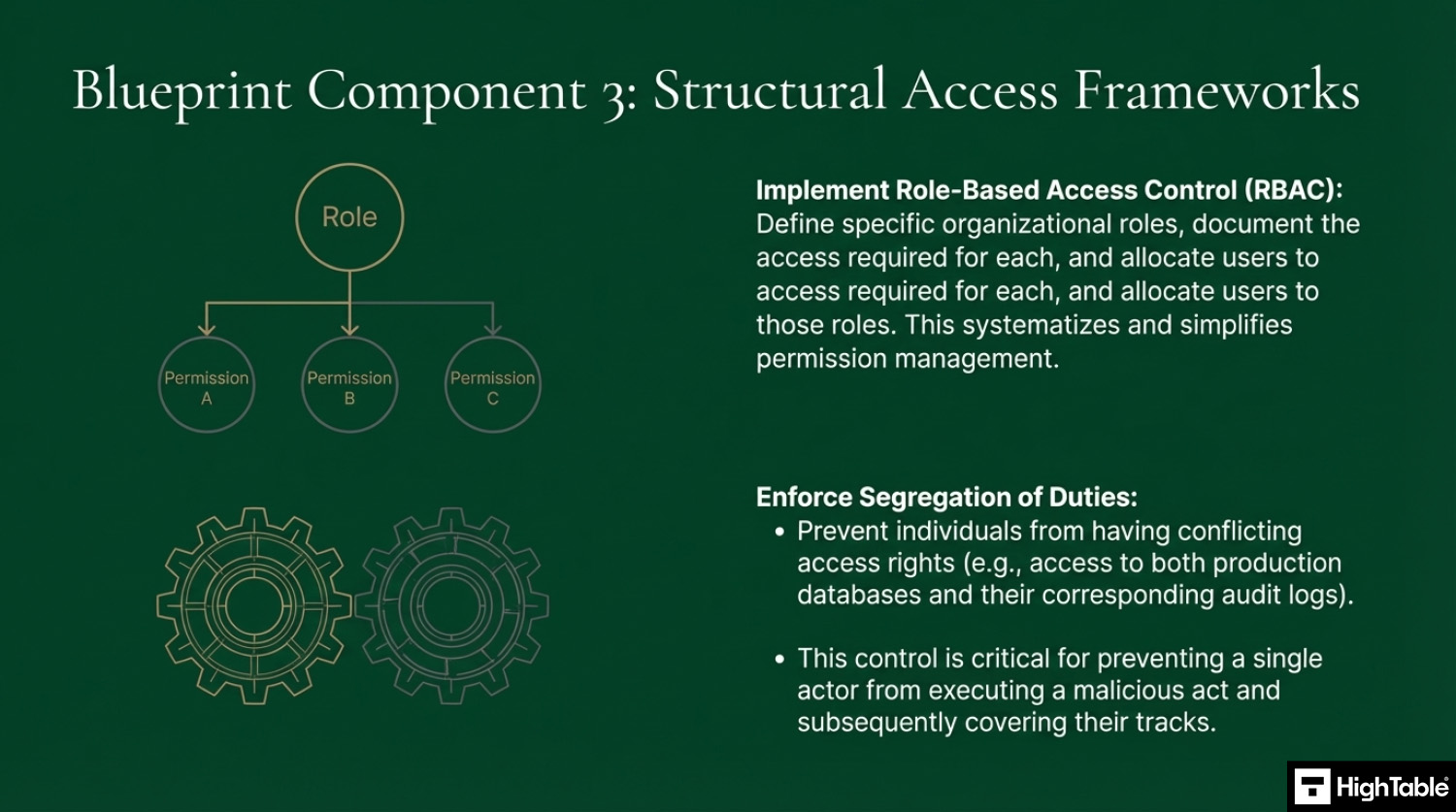
Implement Role Based Access
I find the use of role based access as a technique is a great tool here. Understanding what roles you need, defining them and then allocating people to roles based on need.
Ensure there is segregation of duty
When implementing this control use common sense and be practicable. We are working here on the principle of segregation of duty. We do not want the person with the access to authorise the access and where possible the person with access should not have conflicting access. Rather, separate out your privilege accounts logically where it makes sense and you are able to do so. An example would be to separate out those with the access to the databases from those with access to the logging and monitoring. This prevents things like that ability to do something then change the logs to cover it up.
Adopt the principle of Least Privilege
Access should be granted based on the principle of least privilege, meaning users only get the minimum access necessary for their role.
Adopt the principle of Need-to-Know
Users should only have access to information they need to perform their duties.
Enforce Access Control
Learning from previous tutorials and in particular ISO 27001 Annex A 5.18 Access Rights you will ensure proper access control proportionate to the risk posed by the access that is required.
Review access requirements
Regular reviews of people’s access should form part of your normal operating rhythm. This also applies to privilege accounts. A process to check who has what and if they still need it. Ideally this will be performed at least monthly.
Restrict the use of privilege accounts
Ideally we want a situation where privilege accounts are only used when needed to perform privileged actions and normal accounts are used in normal day to day operations for the user. It doesn’t have to be this, as this is best practice, but the ideal is some way to distinguish when the user is in privilege mode. It will reduce the likelihood of an information security incident.
This level of account really should be logged and monitored for audit purposes.
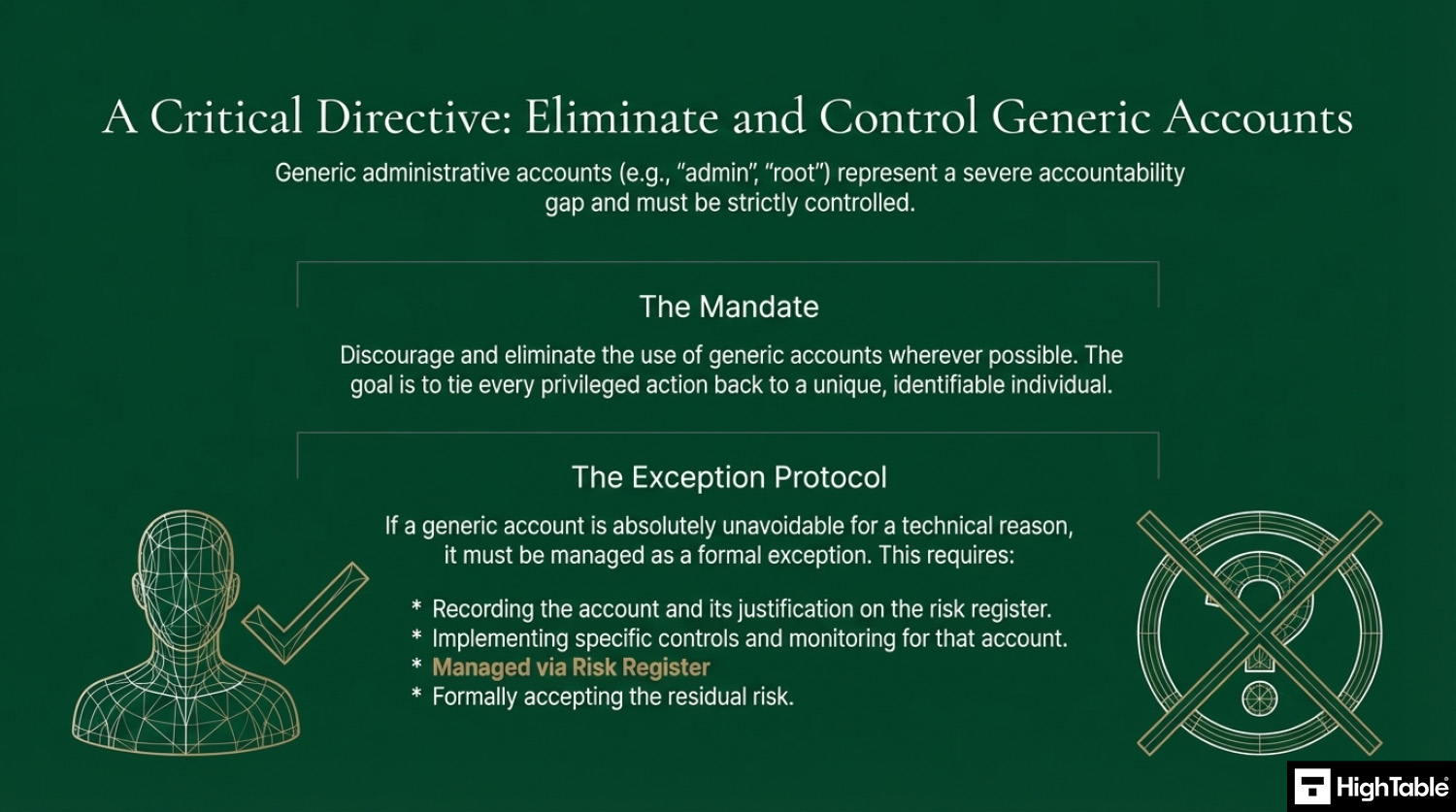
Remove generic privileged accounts
You should really discourage the use of generic administrative accounts. We want to be able to tie actions back to an individual. If you simple have to have a generic account then my recommendation is to manage it as an exception and record it in the risk register. Mange it via risk management, even if that is accepting the risk.
How to implement ISO 27001 Annex A 8.2
Managing privileged access rights is a vital technical control for preventing unauthorised system-wide changes and mitigating the impact of potential security breaches. By following these action-oriented steps, your organisation can establish a robust privileged access framework that satisfies ISO 27001 Annex A 8.2 requirements while ensuring high-level administrative accountability.
1. Formalise Privileged Access Policies and Rules of Engagement
- Identify and document all systems, applications, and network services that require elevated administrative privileges.
- Establish a “Rules of Engagement” (ROE) document that defines the specific scenarios and approval workflows required for granting privileged access.
- Result: A transparent governance framework that ensures all administrative power is granted based on verified business necessity.
2. Provision Granular Identity and Access Management (IAM) Roles
- Enforce the Principle of Least Privilege (PoLP) by creating distinct IAM roles for different administrative functions, such as “Network Admin,” “Database Admin,” or “Security Auditor.”
- Revoke generic “Root” or “Superuser” access, ensuring that every privileged action is attributable to a unique, verified user identity.
- Result: A reduced attack surface where administrative users can only access the specific technical components required for their job.
3. Implement Just-In-Time (JIT) and Ephemeral Access
- Deploy a Privileged Access Management (PAM) solution to provide Just-In-Time elevation, granting administrative rights only for a specific time window.
- Utilise ephemeral credentials or tokens that expire automatically after the pre-authorised task is completed.
- Result: Elimination of “standing privileges,” significantly narrowing the window of opportunity for attackers to exploit active administrative sessions.
4. Mandate Multi-Factor Authentication (MFA) and Secure Vaulting
- Enforce phishing-resistant Multi-Factor Authentication (MFA) for every login attempt to a privileged account or management console.
- Securely vault all administrative passwords and SSH keys within a PAM system, preventing administrators from knowing or storing clear-text credentials.
- Result: Protection against credential-based attacks and the mitigation of risks associated with shared or poorly managed administrative secrets.
5. Execute Continuous Session Monitoring and SIEM Logging
- Configure system logs to capture all privileged commands and configuration changes, exporting this telemetry to a centralised SIEM platform.
- Enable session recording or live monitoring for high-risk administrative activities to provide a visual or text-based audit trail of all actions performed.
- Result: Enhanced situational awareness and a forensically sound record of all elevated activities for compliance and incident response.
6. Revoke and Review Privileged Rights Periodically
- Conduct monthly technical audits to verify the continued requirement for privileged access among authorised personnel.
- Automate the immediate revocation of privileged rights upon a user’s role change or termination of employment through HRIS integration.
- Result: Prevention of “privilege creep” and the elimination of orphaned administrative accounts that could be targeted by malicious actors.
Account Separation Table
| Activity | Standard User Account | Privileged (Admin) Account |
| Email / Web Browsing | ✅ Allowed | ❌ FORBIDDEN |
| Editing Documents | ✅ Allowed | ❌ FORBIDDEN |
| Installing Software | ❌ Blocked | ✅ Allowed |
| Changing System Time | ❌ Blocked | ✅ Allowed |
ISO 27001 Access Control Policy Template
The ISO 27001 Access Control Policy template is pre written and ready to go. It is one of the required ISO 27001 policies that sets out the organisations approach to access control.

I’ve sat in the Auditor’s chair for 30 years. Use the exact system and tools I use to guarantee a pass.

How to pass an audit of ISO 27001 Annex A 8.2
Based on my experience this is the best practice approach to passing the audit of ISO 27001 Annex A 8.2 Privileged Access Rights.
Time needed: 1 day.
How to pass an audit of ISO 27001 Annex A 8.2
- Have policies and procedures in place
Write, approve, implement and communicate the documentation required for privileged access rights.
- Assess your privilege use requirements and perform a risk assessment
Identify what your requirements are for privileged access and then perform a risk assessment.
- Implement controls proportionate to the risk posed
Based on the risk assessment implement controls proportionate that risk assessment and the needs of the business.
- Keep records
For audit purposes you will keep records. Examples of the records to keep include changes, updates, monitoring, review and audits.
- Test the controls that you have to make sure they are working
Perform internal audits that include the testing of the controls to ensure that they are working.
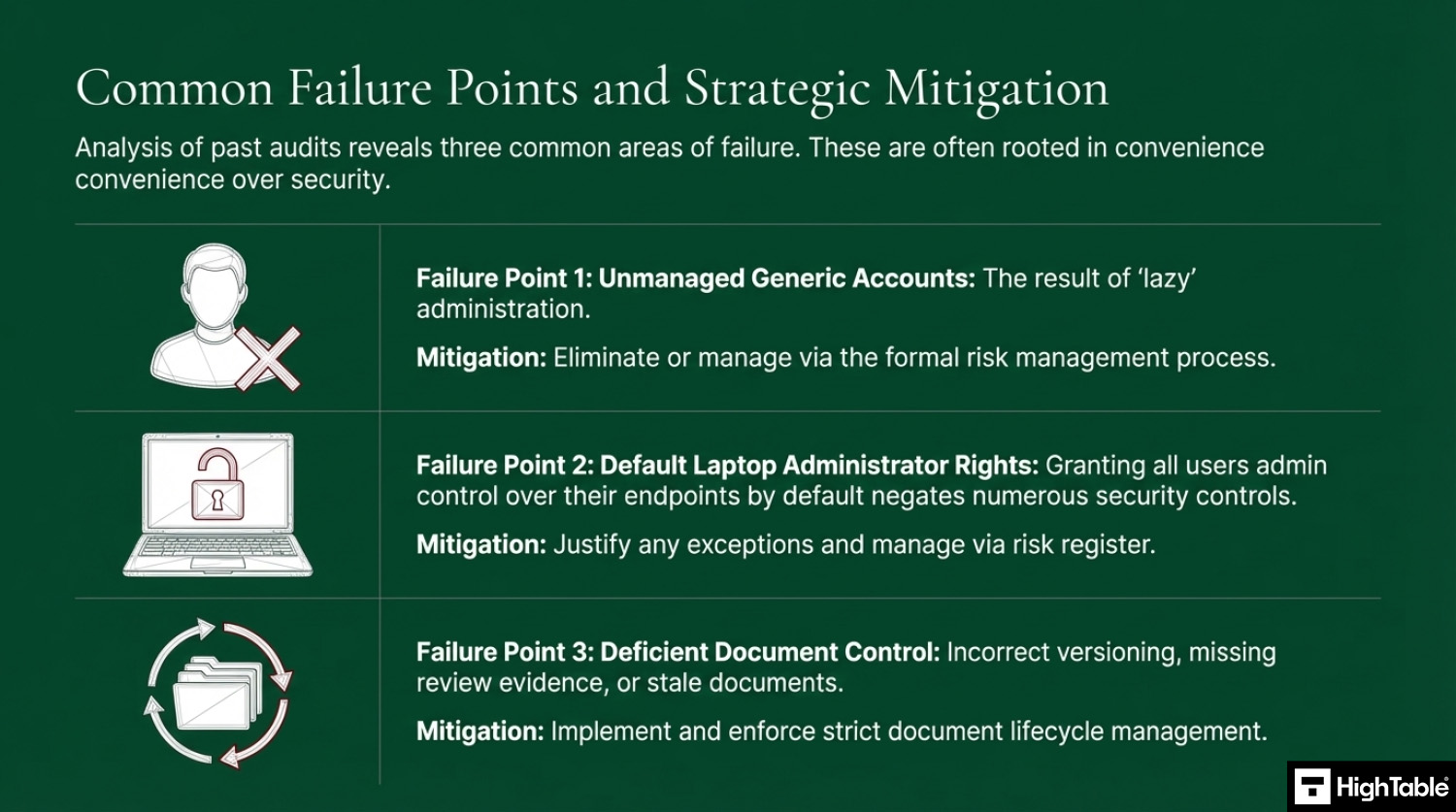
Top 3 ISO 27001 Annex A 8.2 mistakes and how to avoid them
The top 3 mistakes people make for ISO 27001 Annex A 8.2 are
- Having generic accounts: Having generic accounts is not always a bad thing but having them because you are lazy is. Try to eliminate them and where you do require them manage via risk management. This means recording them on the risk register and managing the risk, even if managing the risk is accepting the risk and recording the decision.
- Laptop Administrator Accounts: This common mistake actually relates to end points and the default position of providing all users administrative control over those devices by default. Again, this is usually lazy management and again, as above, if required manage it via risk management. Auditors check and will want a justification and don’t just do it because it is easy or you have always done it. This level of access really does negate a lot of the end point controls that you are going to rely on.
- Your document and version control is wrong: Keeping your document version control up to date, making sure that version numbers match where used, having a review evidenced in the last 12 months, having documents that have no comments in are all good practices.
ISO 27001 Annex A 8.2 FAQ
What is the specific requirement of ISO 27001 Annex A 8.2?
Annex A 8.2 requires the strict restriction and management of privileged access rights. Organizations must ensure that users with elevated permissions (such as administrators) are only granted access through a formal authorization process. Key requirements include:
- Allocation: Access must be specific, authorized, and logged.
- Minimization: Use the “Least Privilege” principle (only what is necessary).
- Traceability: Every privileged action must be linked to a specific user identity.
- Review: Access rights must be reviewed at regular intervals (e.g., monthly).
What counts as “privileged access” in an ISO 27001 audit?
Privileged access refers to any account or role that can bypass standard security controls or alter system configurations. These are often referred to as the “keys to the kingdom.” Common examples include:
- Domain Administrators: Users who can manage the entire network infrastructure.
- Local Administrators: Users with full control over a specific endpoint or server.
- Root Users: The highest level of access in Unix/Linux environments.
- Service Accounts: Non-human accounts used by applications to run automated tasks with elevated rights.
Does ISO 27001 require separate accounts for administrative tasks?
Yes, separating standard and administrative accounts is a critical best practice for compliance. An individual should not use a privileged account for day-to-day activities like reading emails or browsing the web. Implementation involves:
- Standard User Account: Used for 95% of daily work (email, document editing).
- Admin Account: Used only when performing specific administrative tasks.
- Risk Reduction: This prevents a phishing attack on a daily email from compromising the entire network via admin rights.
Are generic or shared administrator accounts allowed?
No, shared or generic accounts (e.g., “admin@company.com”) are strictly prohibited under best practice compliance. You must be able to attribute every privileged action to a specific human being. If a generic account is absolutely necessary for technical reasons:
How often should privileged access rights be reviewed?
Privileged access rights should be reviewed at least monthly, or upon any significant change in personnel. This frequency is higher than standard user reviews because the risk is significantly greater. The review process should verify:
- Continued Business Need: Does the user still require this level of access?
- Role Changes: Has the user moved to a department where this access is no longer needed?
- Activity Logs: Has the account been dormant? (Dormant admin accounts should be disabled immediately).
What evidence will an auditor ask for regarding Annex A 8.2?
Auditors will primarily look for the “who, when, and why” of your privileged accounts. Be prepared to produce the following evidence during your Stage 2 audit:
- The List: An up-to-date inventory of all users with admin rights.
- Authorization Records: Documented approval tickets or forms for when access was granted.
- Access Reviews: Minutes or logs showing you reviewed these rights last month.
- Audit Trails: Logs showing specific actions taken by an administrator on a specific date.
What is “Segregation of Duties” in privileged access?
Segregation of Duties (SoD) ensures that no single person has total control over a critical process. In the context of Annex A 8.2, this prevents internal fraud and error. Examples include:
- Approvals: The person requesting admin access cannot be the same person who approves it.
- Audit Logs: Ideally, system administrators should not have permission to delete or modify the security logs that track their own actions.
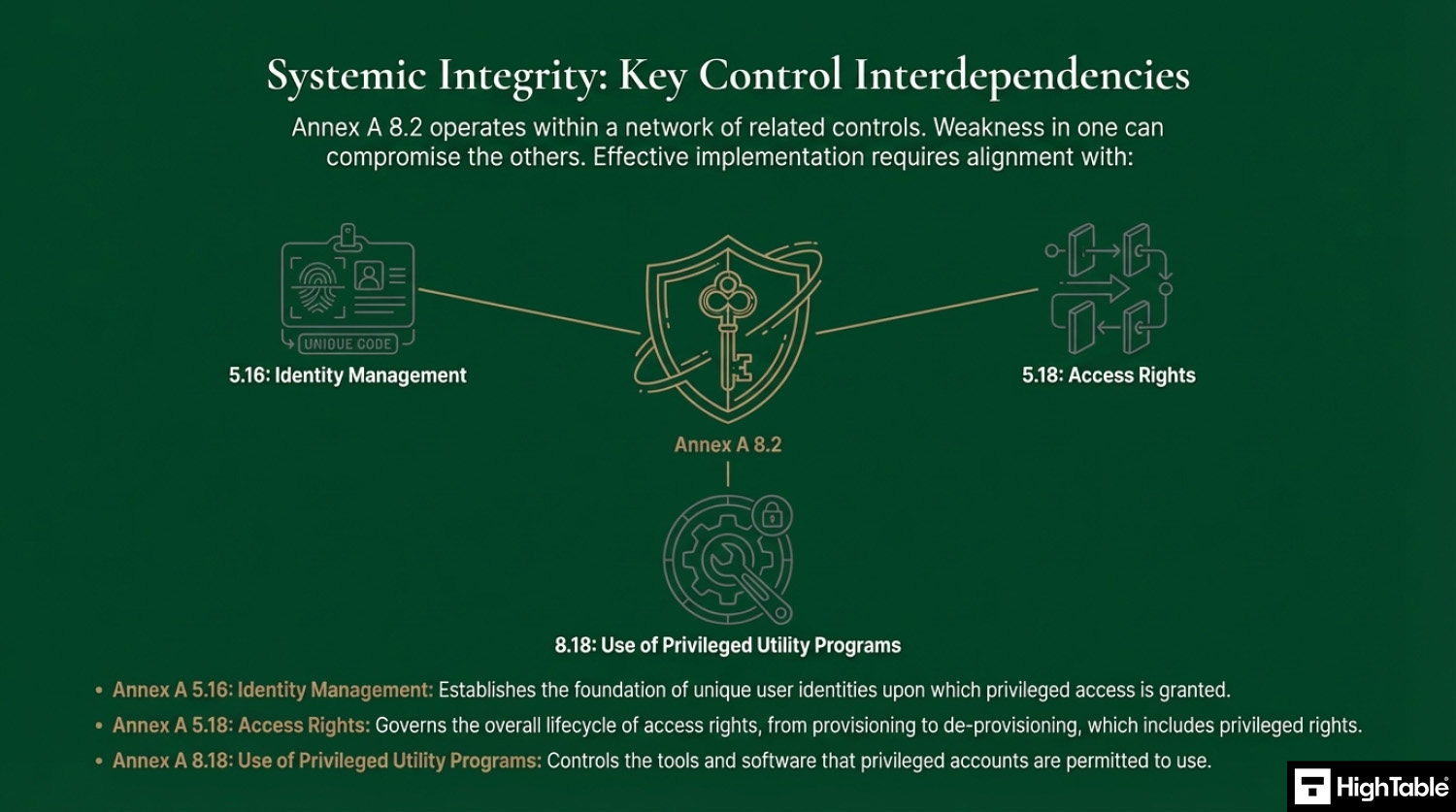
Related ISO 27001 Controls
Applicability of ISO 27001 Annex A 8.2 across different business models.
| Business Type | Applicability | Examples of Control Implementation |
|---|---|---|
| Small Businesses | Focuses on removing “Local Admin” rights from staff laptops and ensuring that only specific technical roles have administrative access to central productivity tools (e.g., M365/Google Workspace). |
|
| Tech Startups | Critical for managing high-trust environments. Compliance requires a formal authorization process for granting “Global Admin” or “Superuser” rights to developers and ensuring these rights are reviewed frequently. |
|
| AI Companies | Vital for protecting core model IP and high-performance computing (HPC) clusters. Focus is on isolating administrative access to GPU nodes and sensitive training datasets. |
|
Fast Track ISO 27001 Annex A 8.2 Compliance with the ISO 27001 Toolkit
For ISO 27001 Annex A 8.2 (Privileged access rights), the requirement is to restrict and manage the allocation and use of privileged access, such as administrator, super user, or global admin accounts. These accounts hold the “keys to the kingdom,” and their mismanagement is a top cause of major security breaches.
| Compliance Factor | SaaS Compliance Platforms | High Table ISO 27001 Toolkit | Audit Evidence Example |
|---|---|---|---|
| Policy Ownership | Rents access to your administrative rules; if you cancel, your documented authorization history disappears. | Permanent Assets: Fully editable Word/Excel Privileged Access Policies that you own forever. | An Account Separation Table stored on your secure server defining “Standard” vs. “Admin” account rules. |
| Implementation | Over-engineers compliance with complex PAM integrations that duplicate native Entra ID, Okta, or Google data. | Governance-First: Formalizes your existing roles (Global Admin, Super User) into an auditor-ready framework. | A signed Privileged Access Review log proving that elevated permissions are audited every 90 days. |
| Cost Structure | Charges a “Success Tax” based on the number of privileged users or “admin seats,” scaling OpEx as you grow. | One-Off Fee: A single payment covers your governance documentation for 2 admins or 200. | Allocating budget to hardware MFA or PAM tools rather than a monthly compliance “paperwork” subscription. |
| IAM Strategy Freedom | Limited by vendor “connectors”; struggles with hybrid, on-premise, or custom local server setups. | 100% Agnostic: Standards adapt to any environment, from cloud-native microservices to local Active Directory. | The ability to switch Identity Providers (IdP) without needing to pay for a new compliance module or integration. |
The Tools We Use.
100% Audit Success. Zero AI Guesswork.

Summary: For Annex A 8.2, an auditor wants to see that you have a formal policy for privileged access and proof that you follow it (e.g., authorization records and access reviews). The High Table ISO 27001 Toolkit provides the governance framework to satisfy this requirement immediately. It is the most direct, cost-effective way to achieve compliance using permanent documentation that you own and control.
Further Reading
ISO 27001 Controls and Attribute Values
| Control type | Information security properties | Cybersecurity concepts | Operational capabilities | Security domains |
|---|---|---|---|---|
| Preventive | Confidentiality | Protect | Identity and access management | Protection |
| Integrity | ||||
| Availability |
ISO 27001 Annex A 8.2 Strategic Briefing Slides