ISO 27001 Clause 5.1 Leadership and Commitment is a security control that mandates top management to demonstrate active engagement in the Information Security Management System (ISMS). It requires leaders to ensure resources are available and security objectives align with strategic goals, thereby ensuring the organization achieves intended outcomes and improved compliance.
In this guide, I will show you exactly how to implement ISO 27001 Clause 5.1 and ensure you pass your audit. You will get a complete walkthrough of the control, practical implementation examples, and access to the ISO 27001 templates and toolkit that make compliance easy.
I am Stuart Barker, an ISO 27001 Lead Auditor with over 30 years of experience conducting hundreds of audits. I will cut through the jargon to show you exactly what changed in the 2022 update and provide you with plain-English advice to get you certified.
Key Takeaways
- It’s a Top-Down Mandate: The success of the Information Security Management System (ISMS) hinges on the active and genuine commitment of the leadership team. Without their buy-in and drive, the system is likely to fail.
- Leadership Responsibilities are Clear: Top management is responsible for ensuring the information security policy and objectives align with the company’s strategic goals. They must also provide necessary resources, integrate ISMS requirements into business processes, and communicate its importance throughout the organisation.
- Ensure Intended Outcomes: Leadership’s role is to ensure the ISMS achieves its planned results, support staff in contributing to its effectiveness, and promote continuous improvement.
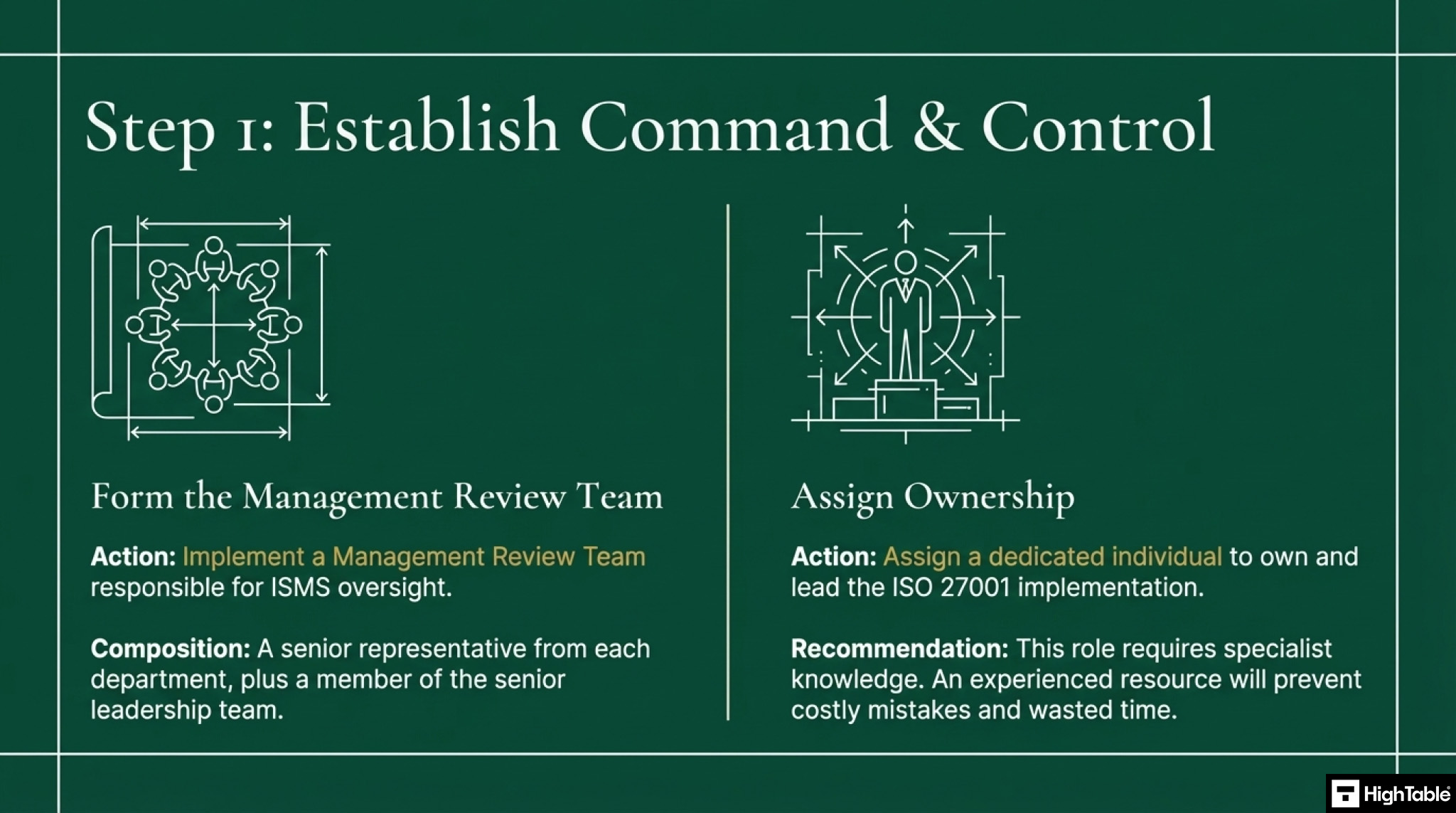
- Key to Implementation: To demonstrate compliance, organisations should establish a Management Review Team with senior representatives and assign a dedicated person to own the ISO 27001 process.
Table of contents
- Key Takeaways
- What is ISO 27001 Clause 5.1 and Why is it Important?
- ISO 27001 Clause 5.1 Explainer Video
- ISO 27001 Clause 5.1 Podcast
- ISO 27001 Clause 5.1 Implementation Video Tutorial
- How to implement ISO 27001 Clause 5.1
- ISO 27001 Clause 5.1 Implementation Checklist
- What is the biggest challenge in implementing clause 5.1?
- How to communicate the importance of information security
- Sample Clause 5.1 Leadership Commitment Statement
- How to audit ISO 27001 Clause 5.1
- ISO 27001 Clause 5.1 Audit Checklist
- How to pass the ISO 27001 Clause 5.1 Audit
- Top 3 ISO 27001 Clause 5.1 Mistakes and How to Fix Them
- Fast track ISO 27001 Clause 5.1 compliance with the ISO 27001 Toolkit
- Tangible KPIs and Metrics: How to Prove Leadership Commitment
- The Auditor’s Secret Evidence Checklist for Clause 5.1
- ISO 27001 Clause 5.1 Applicability Across Different Business Models
- A Deep Dive into “Intended Outcomes” (Clause 5.1e)
- ISO 27001 Clause 5.1 Applicable Laws and Related Standards
- Integrating ISO 27001 Clause 5.1 with ISO 9001 (The Annex SL Advantage)
- ISO 27001 Clause 5.1 FAQ
- ISO 27001 Clause 5.1 Related ISO 27001 Controls
- ISO 27001 Clause 5.1 Executive Briefing Slides
Stop Guessing. Start Passing.
AI-generated policies are generic and fail audits. Our Lead-Auditor templates have a 100% success rate. Don’t risk your certification on a prompt

What is ISO 27001 Clause 5.1 and Why is it Important?
ISO 27001 Clause 5.1 is Leadership and Commitment. It requires you to to make sure you have the support and buy in of your leadership team for your information security management system (ISMS).
Leadership and commitment is about having an information security management system (ISMS) that is driven and led from the top.
Without this level of commitment and drive the information security management is doomed to fail.
Giving this to IT to solve or devolving it to the lower ranks will see people not doing what they should do due to conflicting priorities.
As a top down leadership led standard, for ISO 27001 you are going to make sure that top management can demonstrate leadership and commitment with respect to the information security management system.
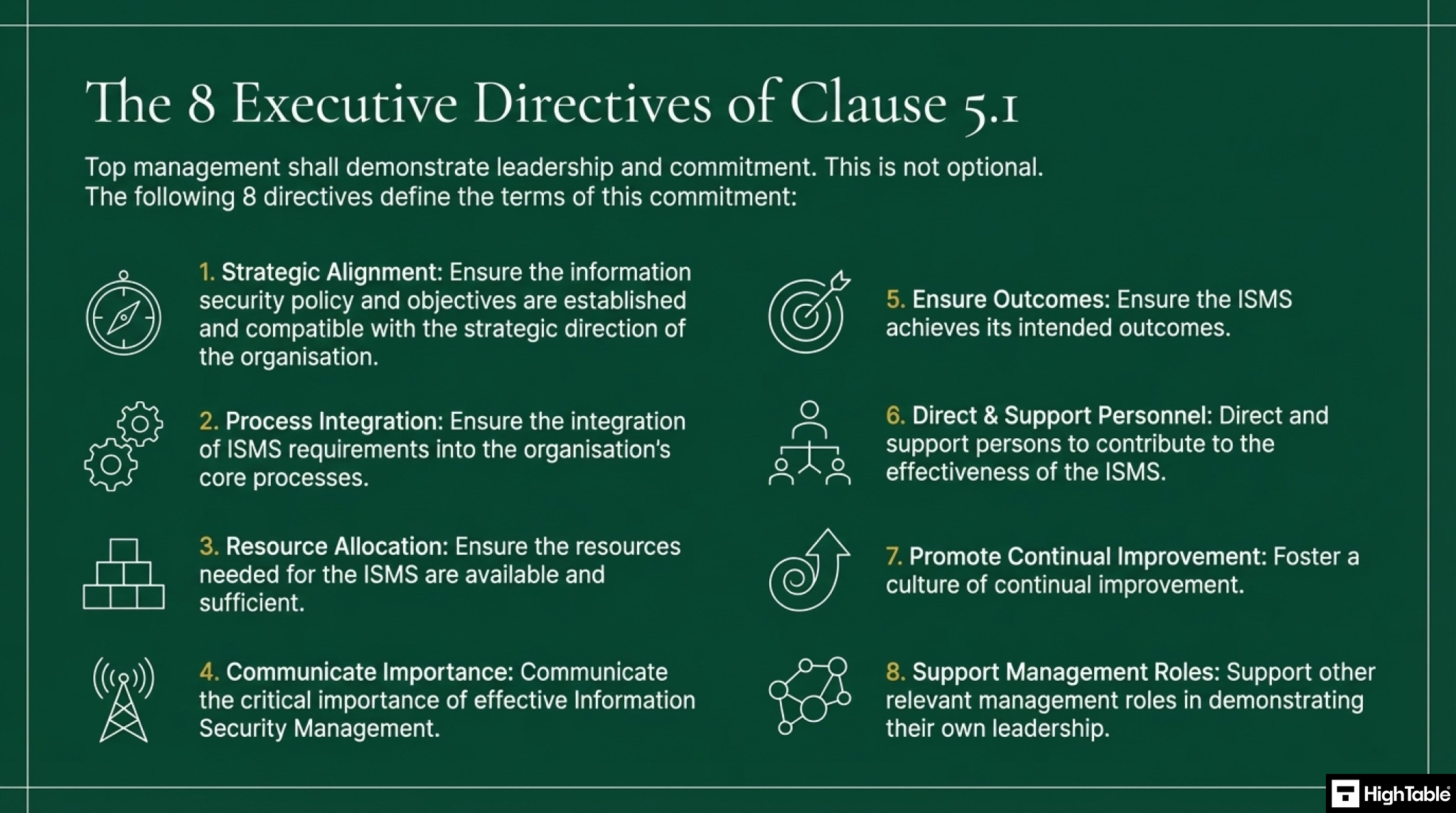
That leadership and commitment will:
- Ensure the information security policy and the information security objectives are established and are compatible with the strategic direction of the organisation.
- Ensure the integration of the information security management system requirements into the organisational processes.
- Ensure that the resources needed for the information security management system are available.
- Communicate the importance of effective Information Security Management and of conforming to the information security management system requirements.
- Ensure that the information security management system achieves its intended outcomes.
- Direct and support persons to contribute to the effectiveness of the information security management system.
- Promote continual improvement
- Support other relevant management roles to demonstrate their leadership as it applies to their role and information security.
Purpose and Definition
The purpose of ISO 27001 Clause 5.1 Leadership and Commitment is to make sure that information security is driven from the top.
The ISO 27001 standard defines ISO 27001 Clause 5.1 Leadership and Commitment as:
Top management shall demonstrate leadership and commitment with respect to the information security management system by: a) ensuring the information security policy and the information security objectives are established and are compatible with the strategic direction of the organisation; b) ensuring the integration of the information security management system requirements into the organisation’s processes; c) ensuring that the resources needed for the information security management system are available; d) communicating the importance of effective information security management and of conforming to the information security management system requirements; e) ensuring that the information security management system achieves its intended outcome(s); f) directing and supporting persons to contribute to the effectiveness of the information security g) promoting continual improvement h) supporting other relevant management roles to demonstrate their leadership as it applies to their
ISO27001:2022 Clause 5.1 Leadership and Commitment
ISO 27001 Clause 5.1 Requirement
There are 8 specific requirements when it comes to leadership and commitment. This is a testament to how importantly the standard takes it. Read the implementation guide below to see exactly what they are how to quickly and simply meet the requirements.
What Changed in ISO 27001:2022 Clause 5.1?
In the transition from the 2013 version to ISO 27001:2022, the most immediate thing you will notice about Clause 5.1 Leadership and Commitment is that absolutely nothing changed. The core requirements for top management to establish policies, allocate resources, and drive continual improvement remain completely identical. The 2022 update preserves the exact text, reinforcing that top-down governance is a timeless, foundational pillar of the Information Security Management System (ISMS). However, while the text did not change, the operational context did. Leadership must now apply this exact same commitment to a modernised set of Annex A controls.
Comparison: ISO 27001:2013 vs. ISO 27001:2022 Clause 5.1
| Feature | ISO 27001:2013 (Old Standard) | ISO 27001:2022 (Current Standard) |
|---|---|---|
| Clause Number | Clause 5.1: Leadership and commitment | Clause 5.1: Leadership and commitment (No structural change) |
| Structure | Listed as the opening mandate of Clause 5 Leadership. | Remains the exact same opening mandate of Clause 5 Leadership, maintaining alignment with the Harmonised Structure. |
| Requirement Text | Dictated 8 specific leadership actions (a through h), including strategic alignment and resource allocation. | Text is identical. The 8 specific leadership actions remain completely unchanged. |
| Operational Context | Leadership funded and supported the 114 Annex A controls relevant to the 2013 threat landscape. | Leadership must now explicitly fund and support the 93 updated Annex A controls, allocating budget for modern requirements like cloud security and threat intelligence. |
ISO 27001 Clause 5.1 Explainer Video
In this strategic implementation briefing, Lead Auditor Stuart Barker and team do a deep dive into ISO 27001:2022 Clause 5.1 Leadership & Commitment.
ISO 27001 Clause 5.1 Podcast
In this episode: Lead Auditor Stuart Barker and team do a deep dive into the ISO 27001:2022 Clause 5.1 Leadership and Commitment. The podcast explores what it is, why it is important and the path to compliance.
ISO 27001 Clause 5.1 Implementation Video Tutorial
For a complete visual guide to this process, check out our video tutorial: How to implement ISO 27001 Clause 5.1 Leadership and Commitment
How to implement ISO 27001 Clause 5.1
ISO 27001 is a top down leadership standard. It’s actually aligned with the majority of the ISO standards. They all follow a very similar format and if you’ve implemented other ISO standards such as ISO 9001 then a lot of what you will see here is going to be familiar to you. It may well be that you’re going to reuse what you have or just do a slight tweak.
You have to show and have to lead from the top. This isn’t driven by someone in IT. This isn’t driven by some information security person like me with their police hat on or their parent hat on telling you what it is that you need to do.
This has to be driven from leadership. It has to be driven from the top.
Time needed: 1 hour and 30 minutes.
How to implement ISO 27001 Clause 5.1 is Leadership and Commitment
- Put in place a management review team
Working out who your information security leadership team is will be straightforward and you will implement a Management Review Team that will be responsible for the oversight of the information security management system (ISMS). The best way to work out who attends this is to have a senior representative from each department in the business plus ( if not already covered ) and member of the senior leadership team.
- Assign someone to own ISO 27001
To lead the work you really should consider bringing in some specialist help. The knowledge and experience of someone how has done this many times before will pay dividends and stop you making costly mistakes and wasting a lot of time. If that is not an option for you then getting members of your team trained in ISO 27001 lead implementor or ISO 27001 lead auditor may be a viable option. These courses come with a word of caution though as they are mainly booked based and generic in nature. They do not share the real world trials and tribulations of how you actually implement in your organisation. Which ever route you go, having a resource to lead the implementation and certification is a requirement.
- Write your information security policies
Write your information security policy and your associated topic specific information security policies based on the needs of the business and the risks the business faces. These are defined as part of the process of building your information security management system (ISMS).
- Write your information security objectives
Ensure that your information security objectives are Specific, Measurable, Achievable, Realistic and Timely (SMART) and for each objective clearly set out what the measures are. The information security objectives are recorded and communicated in the Information Security Policy and they are included as part of the structured agenda at the Management Review Team meeting for reporting and oversight.
- Agree and sign off the policies and objectives
The senior leadership team agree and sign off the policies and objectives.
- Implement an information security management system (ISMS)
The first resource you need is the information security management system. This is the ISO 27001 toolkit. The success of your ISO 27001 implementation and your ISO 27001 certification will hang on having the right resources available, allocated and engaged.
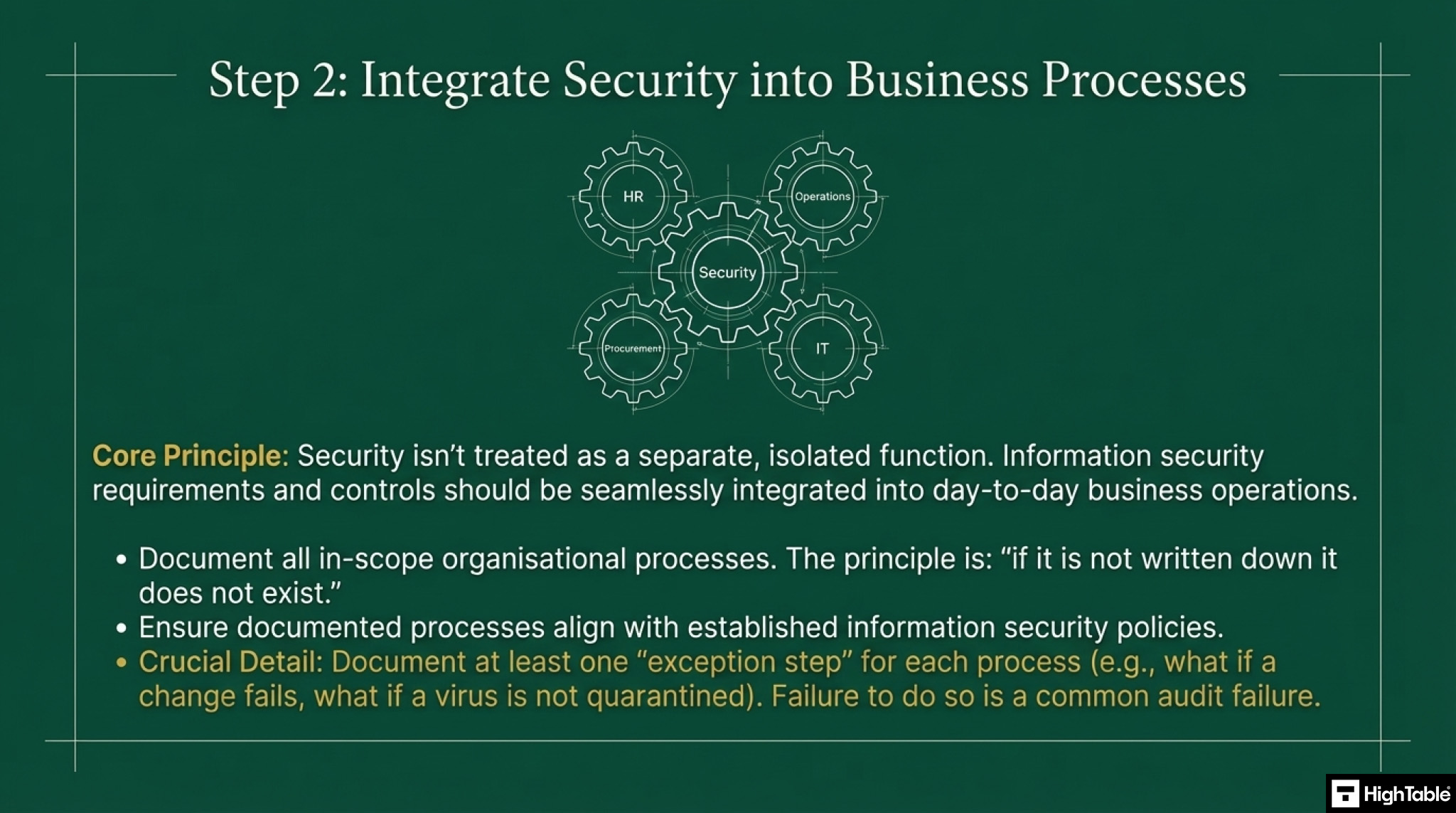
- Integrate the information security management system requirements into the organisational processes
Ensure the integration of the information security management system requirements into the organisational processes. The concept of ‘if it is not written down it does not exist’ plays through ISO 27001 certification. The organisation processes are going to need writing down and formatting in documents with appropriate documentation mark-up and version control. Stating what we do and not what we think auditors want to hear is key here as we will be audited against what we say we do. If we don’t do what we say we do we will fail. You will document your processes simply and you will pay attention to having at least one exception step. An exception step caters for the ‘what if’ scenario that the process does not work or go to plan. What if the change fails? What if the software update fails? What if the virus is not quarantined? You get the idea. Auditors will always seek this out and ask. It is a common audit failure where it has not been considered and documented. Satisfy this by having information security policies in place and then write and align your actual processes to those policies. Don’t forget to document the processes of the in scope products and services. Policies are statements of what we do not how we do it. How we do it is covered in these process documents. The process steps recorded are very specific so that anyone, even someone who has never worked in this area before, can follow them and achieve the same and consistent result.
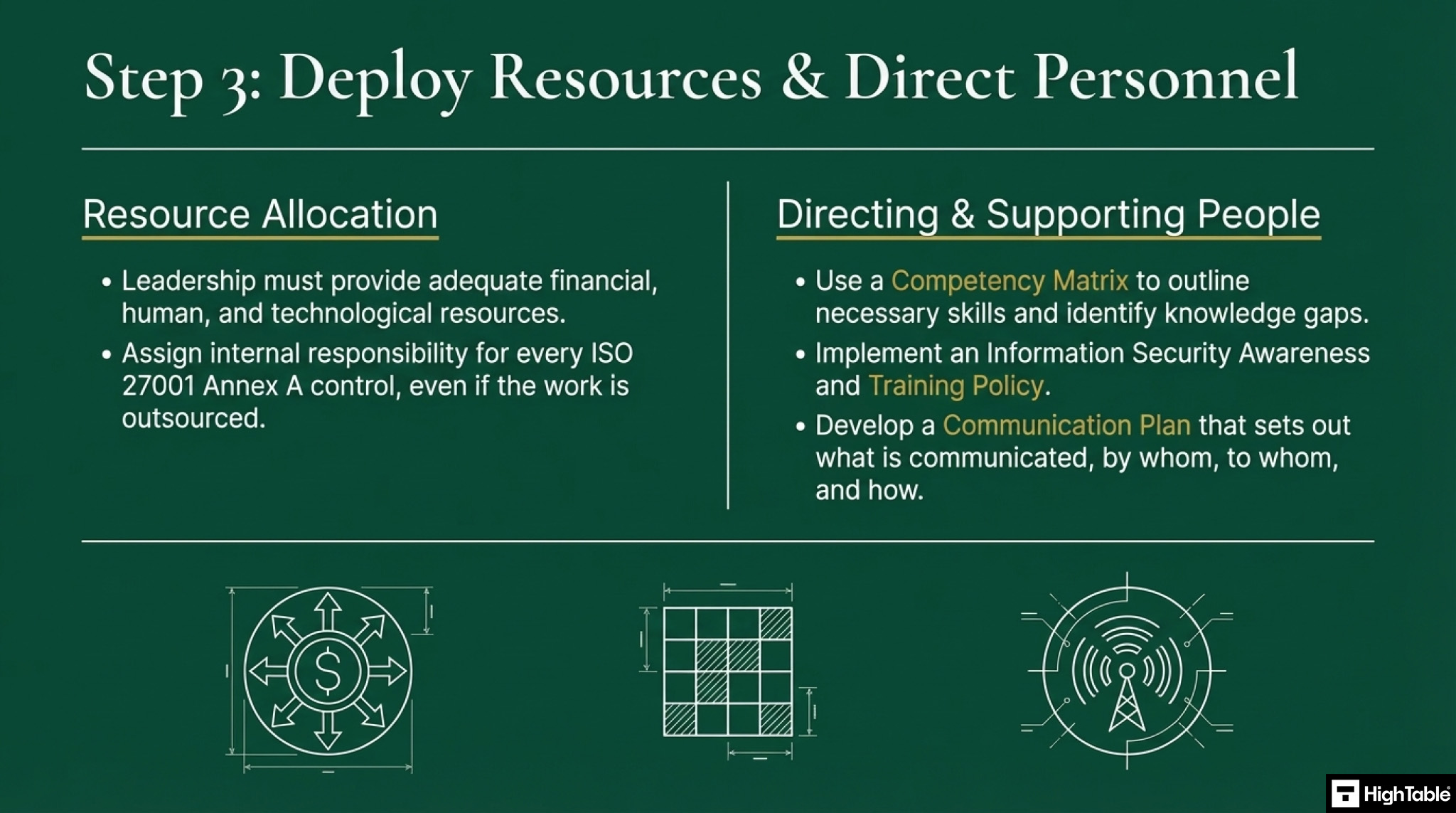
- Ensure Necessary Resources are Allocated
Understand the ISO 27001 standard and the ISO 27001 Annex A controls (referred to as ISO 27002) and allocate members of your team to those controls. You do this by recording them in an ISMS Annex A Controls – Accountability Matrix which assigns responsibility for each ISO 27001 Annex A Control. It is ok that the work is carried out by a third party company but you must still assign internal responsibility for managing it and ensuring it gets done. There are a number of recommended documents to demonstrate this. There is the roles and responsibilities document that sets out all the roles and responsibilities and it states what those responsibilities are. You just allocate people to it.
- Communicate on information security
You are going to communicate the importance of an effective information security management system and of conforming to the manage system requirements. There are a number of different ways that to demonstrate that from a leadership point of view. For a detailed run through read ISO 27001 Clause 7.4 Communication Communication is expected at all levels, across all medium and has some very specific requirements. It can easily be implemented and evidenced. It can take many forms. For example it will be part of any legal contracts that you have with suppliers and with clients as well as employees. You will implement an Information Security Awareness and Training Policy that sets out the training and awareness for the company as well as deploying training tools that allow you to schedule your communications and include acknowledgement of understanding such as tests or quizzes that you can use to evidence your compliance. You will plan your training based on business need and business risk but you will do Basic Information Security Awareness Training and Basic Data Protection Training at least annually. You may tailor your training and communication to specific groups and sub groups based on their specific needs. You will implement a Communication Plan that sets out the communications for the year across media and approaches. It will be a record and a plan of what was communicated, who communicated it, to whom they communicated it, what they communicated and how they communicated it and it will include the evidence the communication took place. There may be other processes that involve communication that you will evidence. Here we think about off boarding an employee when they leave or due to termination where we want to communicate again their requirements under contract for information security and the expectations that we place on them.
- Direct and support people
You will direct and support people to contribute to the effectiveness of the management system via 1. Policies 2. Training 3. Communication 4. Competency Management and Competency Matrix We want people to contribute effectively and the way we do that is via communicating and supporting them. If we don’t tell people what is expected we can not expect them to do it. You will have employment contracts and third party contracts that include coverage of information security requirements. You will have a Competency Matrix that captures the core competencies and training requirements of staff in relation to information security. Your Information Security Awareness and Training Policy sets out the training and awareness and your training tool and package is used to manage the process and the compliance. The Communication Plan sets out the communications for the year across media and approaches as discussed above.
- Promote continual improvement
As discussed continual improvement is baked in and a core principle. This is not a one and done. The external audits will happen every year as will your ongoing internal audits. Incidents will happen that need managing. Deviations from policy and procedure will happen. New ways of working and new tools will be identified. Your Continual Improvement Policy sets out the continual improvement policy and the Incident and Corrective Action Log captures and manages the corrective actions and improvements. The Communication Plan sets out the communications for the year across media and approaches and your management review team oversees the entire continual improvement process. Implement continual improvement – further reading – ISO 27001 Clause 10.1 Continual Improvement
- Support management roles
Support other relevant management roles to demonstrate their leadership as it applies to their areas of responsibility. Examples of how to support other management roles include: competency matrix training plans communication plans management review meeting top-down communication
I’ve sat in the Auditor’s chair for 20 years. These are the exact tools I use to guarantee a pass.

ISO 27001 Clause 5.1 Implementation Checklist
As Stuart Barker, an ISO 27001 Lead Auditor with over 30 years of experience, I know exactly where organisations fail when trying to prove top management involvement. Implementing ISO 27001 Clause 5.1 Leadership and Commitment is not a tick-box exercise: it requires verifiable, top-down governance. Use this 10-step implementation checklist to bypass common traps, deploy technical controls, and capture the exact evidence external auditors demand.
| Implementation Step | Required Action | The Trap (Common Challenge) | Result / Technical Requirement |
|---|---|---|---|
| 1. Align Information Security with Business Strategy | Draft a bespoke Information Security Policy and align your SMART security objectives directly with core business KPIs, such as system uptime or customer data protection. | Copy-pasting generic policies that do not reflect what the business actually does or the specific risks it faces. | Result: Information security becomes a strategic enabler rather than an isolated, generic compliance exercise. |
| 2. Establish Management Review Governance | Formalise a Management Review Team comprising C-suite executives and core department heads. | Delegating the entire ISMS to a single IT junior who lacks the authority or budget to enforce compliance. | Technical Requirement: Document the committee’s Terms of Reference and meeting cadence within your central Asset Register for complete auditor visibility. |
| 3. Integrate Processes into Workflows | Embed security controls directly into existing business workflows, such as mandating security checks within the HR onboarding process. | Treating security as an afterthought or a completely separate, isolated IT checklist. | Technical Requirement: Implement strict Rules of Engagement (ROE) for technical deployments to ensure security is natively integrated into operational processes. |
| 4. Allocate Essential ISMS Resources | Top management must formally approve and allocate a dedicated ISMS budget to provision a qualified Information Security Manager and required technology. | Approving the ISMS project verbally but denying the financial budget for essential technical tools or personnel. | Result: Critical infrastructure, such as your Identity and Access Management (IAM) systems, remains fully funded and operational. |
| 5. Define Accountability and Ownership | Implement a documented RACI matrix and assign specific ISO 27001 Annex A control ownership to respective department heads. | Ambiguous ownership where department heads assume information security is solely an IT problem. | Result: Distributed accountability ensures no technical control is left unmanaged or undocumented. |
| 6. Enforce Top-Down Communication | Establish a recurring, top-down communication plan utilising quarterly town halls and monthly intranet updates. | Sending a single, generic email once a year that employees immediately ignore. | Result: Security is reinforced as a non-negotiable business priority, ensuring all staff understand their role in protecting data. |
| 7. Direct and Support Personnel Competency | Deploy a competency matrix to identify skill gaps and mandate role-specific security awareness training for all staff. | Blaming staff for clicking phishing links without providing them with adequate technical tools or training. | Result: Personnel are fully supported to contribute to the ISMS, starting directly with the executive board’s participation in training. |
| 8. Measure Outcomes and KPIs | Define clear Key Performance Indicators (KPIs) linked directly to your SMART objectives and review incident data. | Implementing security controls but never actively measuring if they successfully mitigate cyber risks. | Result: Top management can mathematically verify that the ISMS achieves its intended outcomes during structured management review meetings. |
| 9. Drive Continual Security Improvement | Embed a formal Continual Improvement Policy where leadership actively reviews internal audit results and funds vulnerability remediation projects. | Viewing ISO 27001 as a one-and-done project merely to acquire a compliance certificate. | Result: The organisation continually adapts to emerging threats, consistently updating technical controls like Multi-Factor Authentication (MFA) policies. |
| 10. Evidence Leadership Commitment | Capture digital signatures on all approved policies and retain detailed, signed minutes of Management Review meetings. | Having genuine executive support but absolutely zero documented proof to show the external certification auditor. | Result: Indisputable audit evidence is secured in a central repository, guaranteeing compliance with the standard’s documentation requirements. |
What is the biggest challenge in implementing clause 5.1?
The single biggest challenge in implementing Clause 5.1 is getting senior executives to care. In many organisations, top management views ISO 27001 as a technical IT problem or a simple compliance tick-box exercise. They want the certificate on the wall to win tenders, but they do not want to invest their personal time into the process.
Overcoming this requires a shift in language. You must stop talking to the board about firewalls and encryption. You must start talking about business risk, revenue protection, and legal liability. When leadership understands that a data breach could result in personal fines under regulations like NIS2 or GDPR, their commitment to the Information Security Management System usually materialises very quickly.
How to communicate the importance of information security
Effective communication from top management must be highly visible and repetitive. To satisfy an auditor, you should deploy a mix of the following strategies and keep a record of every single one:
- The Annual Kick-off: The CEO presents the company’s security objectives at the start of the year during an all-hands meeting.
- Monthly Memos: A short, top-down email from the board highlighting a recent security win or a new emerging threat.
- Intranet Dashboards: A highly visible, transparent dashboard showing the company’s current security score or training completion rates.
- Contractual Mandates: Embedding security expectations directly into employee contracts and third-party vendor agreements.
How can an ISO 27001 Toolkit help with ISO 27001 Clause 5.1?
Getting senior executives to draft communication plans and format Management Review agendas from scratch is completely unrealistic. An ISO 27001 Toolkit solves this by providing pre-written, auditor-approved templates.
The High Table toolkit includes the exact Management Review agenda you need to follow, the Communication Plan template to track executive messaging, and the exact Information Security Policy document ready for the CEO to sign. It removes the administrative friction, allowing leadership to focus on actual governance rather than formatting Word documents.
Sample Clause 5.1 Leadership Commitment Statement
To explicitly document your compliance with Clause 5.1, you should include a formal commitment statement in your overarching Information Security Policy. You can copy and paste the example below, tailor it to your business, and have your CEO sign it.
Top Management Commitment Statement The Executive Board of [Company Name] is fully committed to the establishment, implementation, maintenance, and continual improvement of our Information Security Management System (ISMS). We ensure that the information security objectives are perfectly aligned with our strategic business goals. We accept absolute accountability for the effectiveness of the ISMS and pledge to provide the necessary financial, technical, and human resources required to protect our data, our clients, and our reputation. Information security is a non-negotiable priority for this organisation, and we expect every employee, contractor, and partner to adhere strictly to our security policies. Signed: [CEO Name / Signature] Date: [Current Date]
How to audit ISO 27001 Clause 5.1
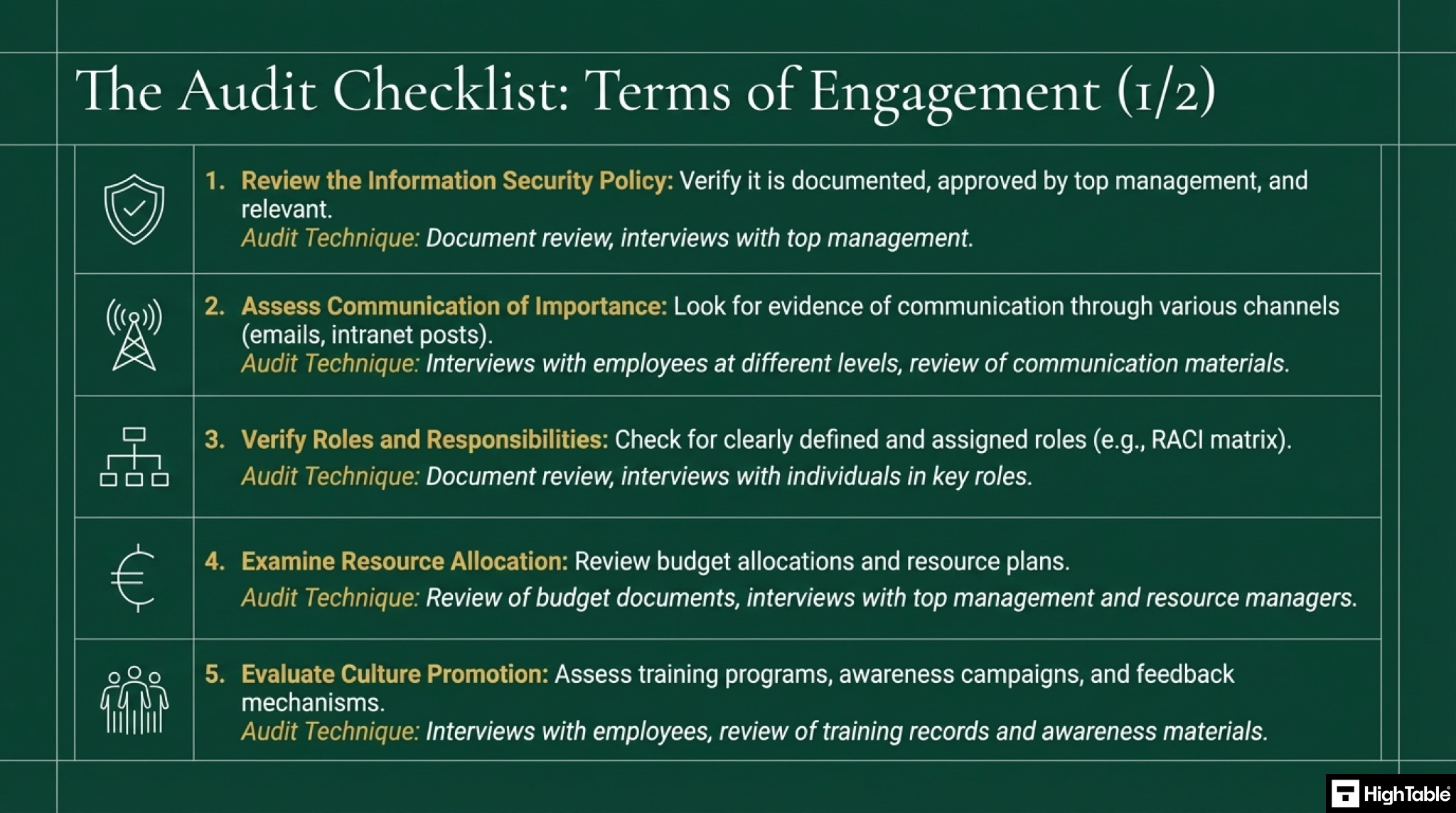
This audit checklist is a guide on how to conduct an internal audit of ISO 27001 Clause 5.1 Leadership and Commitment based on what the ISO 27001 certification auditor will audit. It gives practical audit tips including what to audit and how.
As Stuart Barker, an ISO 27001 Lead Auditor with over 30 years of experience, I know exactly what external auditors look for when verifying top management’s involvement. This audit checklist is a definitive guide on how to conduct an internal audit of ISO 27001 Clause 5.1 Leadership and Commitment. By following these precise steps, you will verify leadership engagement, ensure your Information Security Management System (ISMS) achieves its intended outcomes, and seamlessly pass your certification audit.
1. Review the Information Security Policy
- Action: Review the documented Information Security Policy to verify it is approved by top management and relevant to the organisation’s purpose.
- Result: A foundational governance document is established that clearly addresses key principles like confidentiality, integrity, and availability.
- Audit Technique: Conduct a formal document review of the policy repository and interview top management to confirm their understanding of the policy objectives.
2. Assess Communication of Importance
- Action: Assess how top management communicates the critical importance of information security throughout the organisation using various channels.
- Result: Employees at all levels understand their security obligations, significantly reducing the risk of internal data breaches.
- Technical Requirement: Review communication materials, such as intranet posts and mandatory security updates, ensuring they align with established Rules of Engagement (ROE) documents.
3. Verify Roles and Responsibilities
- Action: Verify that information security roles, responsibilities, and authorities are clearly defined, documented, and assigned to specific personnel.
- Result: Clear accountability is enforced, preventing operational silos and ensuring no security control is left unmanaged.
- Technical Requirement: Audit the documented RACI matrix and verify that Identity and Access Management (IAM) roles correctly reflect these assigned responsibilities.
4. Examine Resource Allocation
- Action: Examine budget allocations and resource plans to verify that top management has provided adequate financial, human, and technological support for the ISMS.
- Result: The Information Security Manager possesses the necessary resources to deploy essential controls and maintain continuous compliance.
- Audit Technique: Review financial documentation and interview resource managers to ensure tools like the Asset Register are fully funded and operational.
5. Evaluate Culture Promotion
- Action: Evaluate how top management promotes a robust culture of information security awareness and continual improvement.
- Result: A security-first mindset is fostered across the business, keeping staff vigilant against social engineering and evolving cyber threats.
- Audit Technique: Review training records, phishing simulation feedback mechanisms, and awareness campaigns to evidence leadership’s active promotion of security protocols.
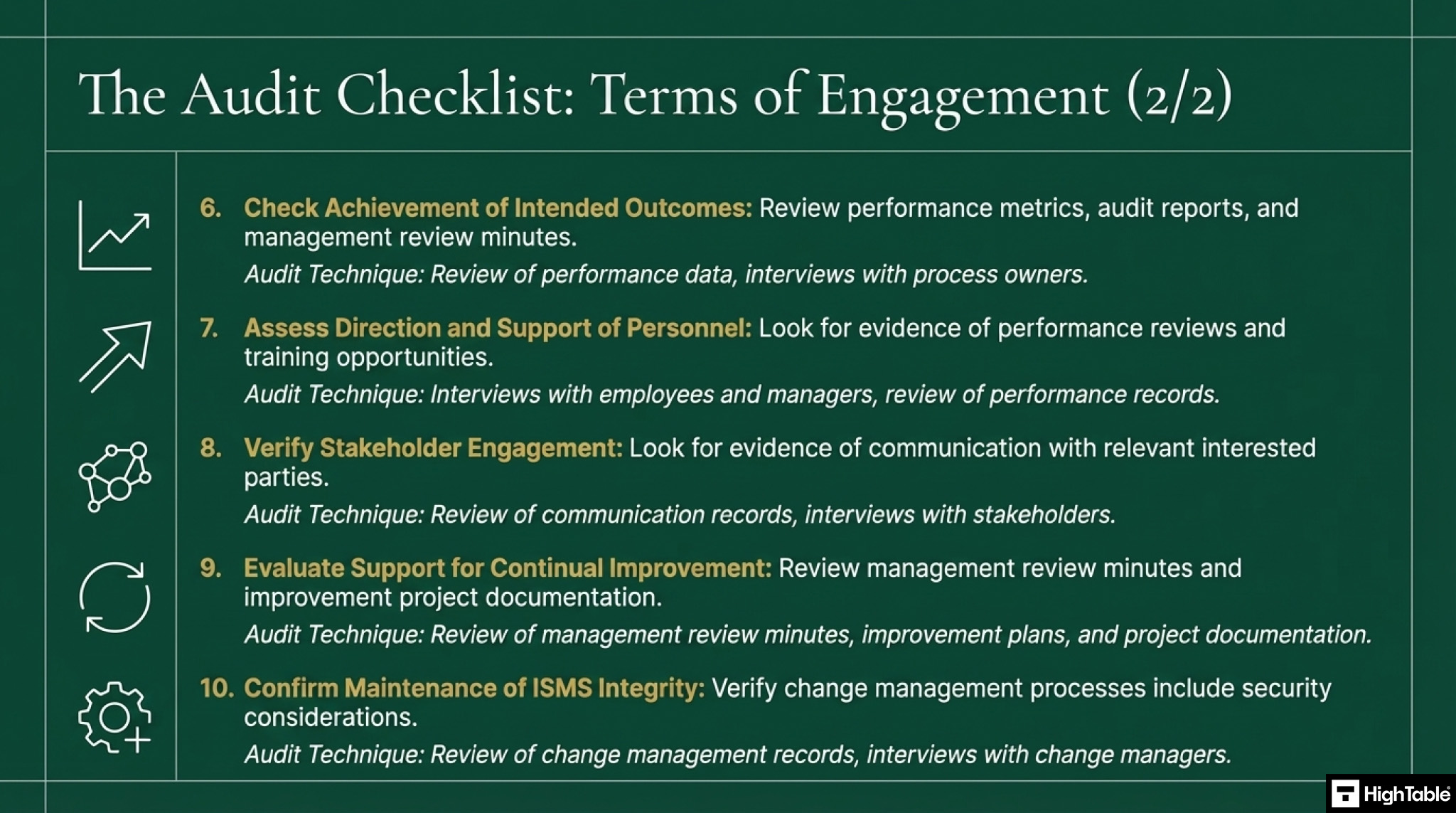
6. Check Achievement of Intended Outcomes
- Action: Check performance metrics, audit reports, and management review minutes to verify that the ISMS is actively achieving its intended outcomes.
- Result: Quantifiable data confirms the operational effectiveness of implemented security controls and leadership strategies.
- Audit Technique: Review Key Performance Indicator (KPI) dashboards and incident response data to validate the success of the ISMS objectives.
7. Assess Direction and Support of Personnel
- Action: Assess the mechanisms top management uses to direct and support personnel in contributing to the effectiveness of the ISMS.
- Result: Staff are properly empowered, trained, and guided to execute their security duties without operational friction.
- Audit Technique: Interview employees and managers, and review performance records to confirm leadership provides adequate direction for technical and non-technical staff.
8. Verify Stakeholder Engagement
- Action: Verify that top management actively engages interested parties relevant to the ISMS and considers their specific needs and expectations.
- Result: Internal and external stakeholder requirements are seamlessly integrated into the organisation’s broader risk management strategy.
- Audit Technique: Review communication records, vendor risk assessments, and contracts to evidence proper engagement with third parties and internal stakeholders.
9. Evaluate Support for Continual Improvement
- Action: Evaluate management review minutes, improvement plans, and project documentation to assess leadership support for the continual improvement of the ISMS.
- Result: The organisation adapts proactively to new vulnerabilities, maintaining robust defence mechanisms and long-term audit readiness.
- Audit Technique: Track the allocation of resources for improvement projects, such as remediation workflows following vulnerability scans.
10. Confirm Maintenance of ISMS Integrity
- Action: Confirm that top management ensures the integrity of the ISMS is strictly maintained when organisational or technical changes are planned and implemented.
- Result: System changes, software updates, and structural transitions do not introduce new security vulnerabilities or cause compliance failures.
- Technical Requirement: Look for documented evidence of change management processes, including Change Advisory Board (CAB) minutes that explicitly cover security considerations.
The Tools We Use.
100% Audit Success. Zero AI Guesswork.

ISO 27001 Clause 5.1 Audit Checklist
| Ref | Audit Objective (What to Verify) | Audit Technique (Test & Evidence) |
|---|---|---|
| 1 | Verify Policy Alignment Confirm the Information Security Policy and SMART objectives are established and compatible with the strategic direction of the organisation (Clause 5.1a). | Inspection: Review the Information Security Policy document. Confirm it holds a documented, formal approval signature from a C-suite executive and directly references business objectives. |
| 2 | Verify Process Integration Ensure ISMS requirements are integrated directly into the organisation’s daily processes (Clause 5.1b). | Inspection (Cross-Reference): Select a non-IT process, such as HR onboarding. Inspect the Standard Operating Procedure (SOP) to verify that mandatory security checks are natively embedded. |
| 3 | Verify Resource Allocation Confirm top management has provided the exact financial and personnel resources needed for the ISMS (Clause 5.1c). | Inspection & Inquiry: Review the formal ISMS budget approval records. Interview the Information Security Manager to verify they have the necessary tools, such as an active Identity and Access Management (IAM) system. |
| 4 | Verify Security Communication Ensure leadership actively communicates the critical importance of information security (Clause 5.1d). | Observation: Request evidence of top-down communication. Look for recorded town hall meetings, intranet announcements, or company-wide emails sent directly by the CEO regarding security compliance. |
| 5 | Verify Intended Outcomes Confirm the ISMS is mathematically achieving its planned security results (Clause 5.1e). | Inspection: Review Key Performance Indicator (KPI) dashboards. Verify that the recorded metrics align with the stated SMART objectives, demonstrating tangible risk reduction. |
| 6 | Verify Personnel Direction Ensure management directs and supports persons to contribute to ISMS effectiveness (Clause 5.1f). | Inspection: Examine the organisational competency matrix and training logs. Verify that role-specific security awareness training is mandated and actively tracked for completion. |
| 7 | Verify Continual Improvement Confirm leadership actively promotes and funds the continual improvement of the system (Clause 5.1g). | Inspection: Review the Management Review Meeting Minutes. Look for a specific agenda item where top management approves the budget and resources for vulnerability remediation projects. |
| 8 | Verify Delegated Leadership Ensure top management supports other relevant management roles in demonstrating leadership (Clause 5.1h). | Inspection: Review the documented RACI matrix. Confirm that specific ISO 27001 Annex A controls are assigned to relevant department heads, not just the IT department. |
| 9 | Verify Executive Awareness Confirm the executive board actually understands the current state of the ISMS. | Inquiry (Interview): Interview a member of top management. Ask them to explain the organisation’s top three information security risks and how the ISMS is mitigating them. |
| 10 | Verify Culture Promotion Confirm top management leads by example to foster a genuine security culture. | Observation: Inspect the security training completion records. Verify that the CEO and executive board members have personally completed the exact same mandatory security training as the wider staff. |
How to pass the ISO 27001 Clause 5.1 Audit
To successfully pass an audit of ISO 27001 Clause 5.1 Leadership and Commitment you are going to:
- Understand the requirements of ISO 27001 Clause 5.1
- Demonstrate that information security is driven from the top and that their is a culture of information security management
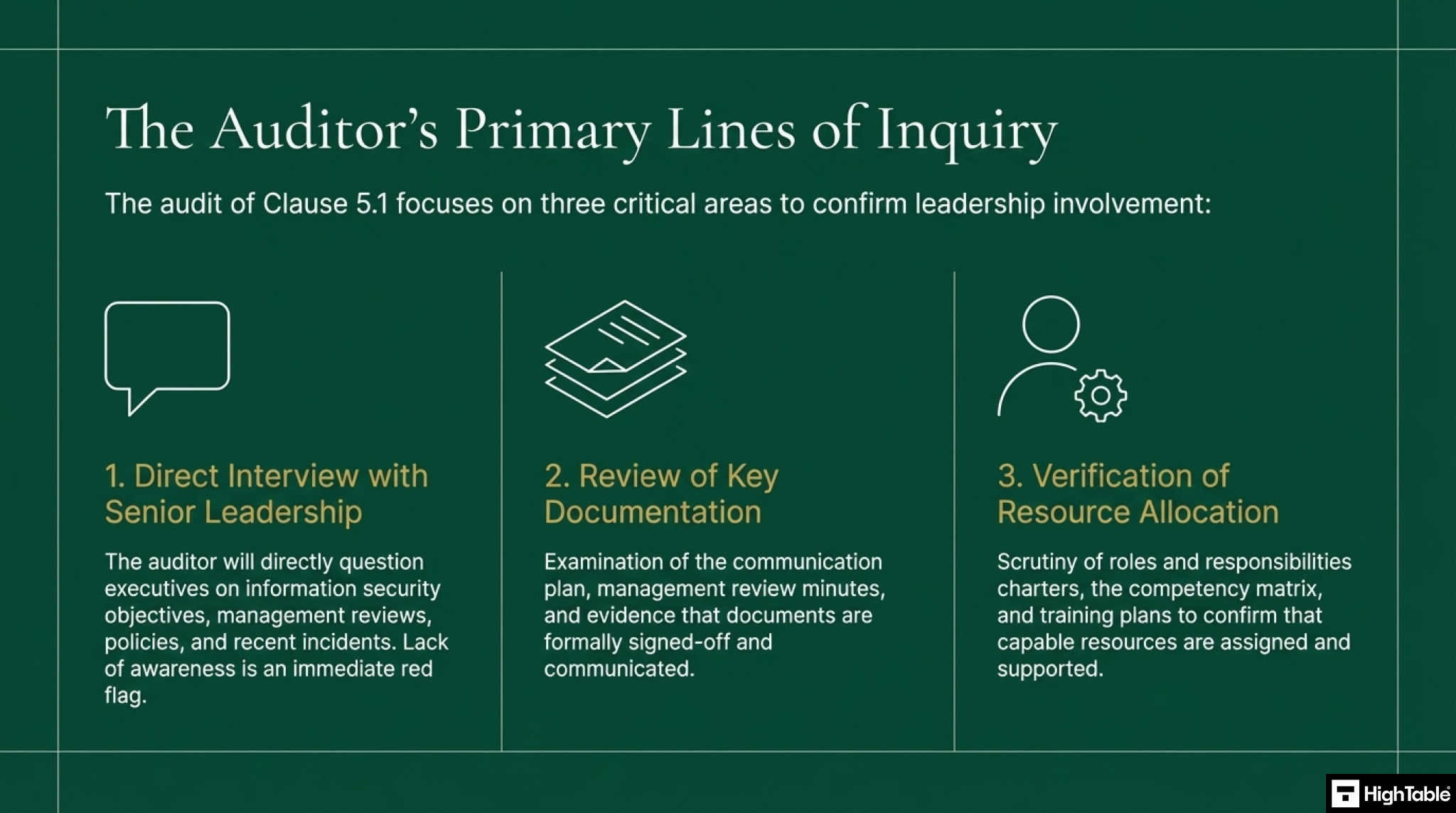
What an auditor looks for
The audit is going to check a number of areas for compliance with ISO 27001 Clause 5.1 Leadership and Commitment. Lets go through them
- An interview with senior leadership: Part of the audit process will be a series of interviews and at least one will be with senior leadership. Here they will ask questions about the information security management system. They will ask about the objectives for information security, when they last did a management review, where the policies are, if there are incidents in the last 12 months. This is a general interview but will catch you out if your senior leadership is not actually involved.
- Your documentation: It is simple but they will check the required documents and processes of the informa t ion security management system (ISMS) that relate to leadership and commitment. This usually means the communication plan and communications sent, that management reviews have happened and you can evidence them. That all document and processes have been signed off and communicated. Work through the implementation guide above and be sure to complete it.
- That you have resources allocated: Part of leading and showing commitment is to have adequate resources in place to run the ISMS. Here they are looking at roles and responsibilities, the competency matrix, the training plan. Are people allocated to roles and do they have the skills to perform the tasks.
From the Trenches: Real Audit Scenarios for Clause 5.1
Let me tell you exactly what passing and failing looks like in the real world. Over the last 30 years, I have seen the good, the bad, and the downright ugly when it comes to leadership commitment. Here are two real scenarios from my time in the audit chair.
The Fail: Delegation Without Accountability
The Scenario: I sat down with a CEO for the mandatory leadership interview. I asked him a very simple question. I wanted to know the top three information security risks to his business and how he was managing them. He looked blankly at me, turned his chair, and pointed to a junior IT support technician sitting in the corner of the room. He told me he did not know and to ask the technician because he handles the whole ISO thing for them.
The Result: Major non-conformity and an instant failure for Clause 5.1. You can delegate tasks, but you absolutely cannot delegate accountability. If top management does not know the risks, does not understand the strategy, and views ISO 27001 purely as an IT problem, the Information Security Management System is fundamentally broken.
The Pass: Leading from the Front
The Scenario: I walked into the opening audit meeting for a mid-sized tech company. Before I even had to ask a question, the CEO stood up, welcomed me, and brought up the company risk dashboard on the screen. She walked me through their core security objectives, explained exactly how those objectives aligned with their strategic business growth plan for the year, and detailed the budget they had ring-fenced for continuous improvement.
The Result: Zero non-conformities and total confidence from the auditor. She controlled the narrative and provided the evidence up front. That is what genuine leadership and commitment looks like, and it sets the tone for a perfectly executed audit.
The Executive Audit Interview: Exact Questions Your CEO Will Be Asked
During your Stage 1 and Stage 2 certification audits, the external auditor will insist on interviewing top management. They will not allow the IT Manager to answer on their behalf. If the CEO or Managing Director cannot answer these questions, you will receive a non-conformity. Print this list, put it on your CEO’s desk, and ensure they know the answers.
| The Auditor’s Question | What They Are Actually Testing | The Expected Answer (Example) |
|---|---|---|
| “How does the Information Security Management System align with the strategic direction of the business?” | Clause 5.1(a): Do they understand that security enables business goals? | “Our primary business goal this year is expanding into the enterprise SaaS market. We cannot win those contracts without proving our data security. The ISMS is directly aligned with that growth strategy by providing the governance required to pass enterprise vendor assessments.” |
| “How do you ensure the ISMS has the resources it needs to operate effectively?” | Clause 5.1(c): Are they holding the purse strings tight, or funding the system? | “I personally review and approve the annual ISMS budget. This year, we allocated specific funds for a new compliance management tool and approved the hire of a dedicated Information Security Officer. We track this budget during our Management Review Meetings.” |
| “How do you measure if the ISMS is actually achieving its intended outcomes?” | Clause 5.1(e): Are they looking at the data? | “We have a set of SMART objectives. I review the performance dashboard every quarter. For example, our goal was zero critical data breaches and 95% training completion. I can confirm we are currently at 100% training completion and have had zero breaches.” |
| “How do you promote a culture of continual improvement?” | Clause 5.1(g): Is this a tick-box exercise, or a living system? | “We do not punish staff for reporting near-misses; we encourage it. I also personally review the results of our internal audits and sign off on the resources needed to close any identified vulnerabilities within 30 days.” |
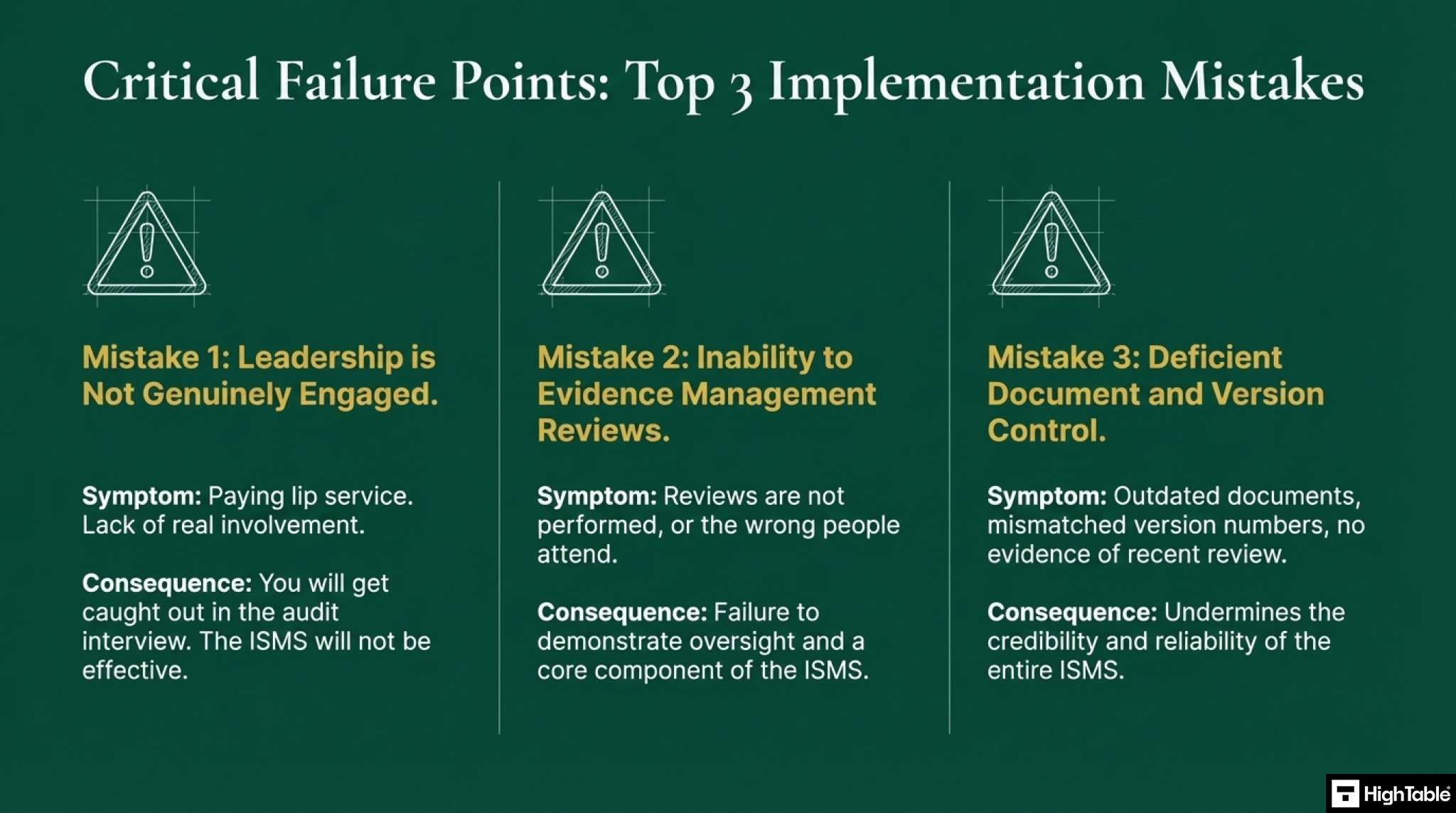
Top 3 ISO 27001 Clause 5.1 Mistakes and How to Fix Them
In my experience, the top 3 mistakes people make for ISO 27001 Clause 5.1 Leadership and Commitment are
- Leadership are not engaged: It is easy to document roles and responsibilities and say leadership is engaged and committed but it is another thing for it to actually happen. If they pay lip service, come the audit and the interviews you will get caught out. Putting aside not having commitment means it is highly likely your ISMS isn’t actually effective and if you are responsible for it you are going to spend most of your career there frustrated.
- You cannot evidence management reviews: The guides and toolkit give you the resources to address this but many organisations just don’t do reviews. Or when they do the wrong people attend making it ineffective. Be able to evidence management reviews that follow the structured agenda of the standard.
- Your document and version control is wrong: Keeping your document version control up to date, making sure that version numbers match where used, having a review evidenced in the last 12 months, having documents that have no comments in are all good practices.
Fast track ISO 27001 Clause 5.1 compliance with the ISO 27001 Toolkit
| Feature | High Table ISO 27001 Toolkit | Online SaaS / GRC Platforms |
| Ownership | Permanent Evidence: You own the meeting minutes, signed policies, and strategy docs. Even if you stop using the toolkit, your evidence of leadership commitment stays in your internal archives forever. | Rented Accountability: Your records of management reviews and approvals are stored in a third-party cloud. If the subscription lapses, your proof of “Leadership” disappears with it. |
| Simplicity | Zero Barrier for Executives: CEOs and Boards use Word, Excel, and PDFs every day. They can sign off on a Word-based policy in seconds without needing to learn a complex software interface or manage new login credentials. | Executive Friction: Senior leaders rarely have the time or patience to log into a proprietary GRC tool. This often results in the “Leadership” section being filled out by a junior admin rather than the actual leaders. |
| Cost | One-Off Investment: A single fee covers the entire leadership framework. There are no recurring monthly costs to maintain your “Commitment” status. | Ongoing Compliance Tax: You pay a monthly fee to host documents that rarely change. Over a 3-year certification cycle, this costs thousands more than a one-off toolkit. |
| Freedom | No Vendor Lock-In: You can move your leadership documentation to any internal system (SharePoint, Teams, etc.). You aren’t tied to a specific vendor’s workflow or software updates. | Workflow Lock-In: You are forced to follow the platform’s specific “Wizard” for management reviews. If their software changes or goes offline, your established governance process is disrupted. |
Tangible KPIs and Metrics: How to Prove Leadership Commitment
As an auditor, I love numbers. You can tell me that your leadership team is committed to information security all day long, but I want you to prove it. Clause 5.1 requires evidence, and the absolute best way to shut an auditor up and sail through this clause is to present hard, measurable Key Performance Indicators (KPIs).
When a client hands me a report with these metrics, the Clause 5.1 audit is effectively over in five minutes. It shows absolute control and indisputable governance.
Here are the exact metrics you should be tracking to evidence top management engagement:
| Metric | What it Proves to the Auditor | Target Outcome |
|---|---|---|
| Executive Attendance at Management Reviews | Proves that the C-suite is actively participating in the ISMS oversight process and not just paying lip service to the standard. | 100% attendance from mandatory leadership representatives. |
| ISMS Budget Allocated vs. Spent | Demonstrates that top management is fulfilling Clause 5.1(c) by providing the actual financial resources needed to maintain security. | Budget tracking is documented, reviewed quarterly, and fully utilised for security tools and personnel. |
| Policy Sign-off Turnaround Time | Shows that leadership prioritises information security governance and does not let critical documents stagnate awaiting approval. | Sign-off achieved within 7 to 14 days of policy review submission. |
| C-Suite Security Training Completion | Proves that leadership is directing and supporting personnel by leading from the front and participating in the exact same training as the wider staff. | 100% completion rate for all board members and senior executives. |
The Auditor’s Secret Evidence Checklist for Clause 5.1
Most companies think a signed policy is enough to prove leadership commitment. It is not. As a Lead Auditor, I look for the hidden trail of evidence that proves the board actually cares. If you want to absolutely guarantee a pass, have these unconventional pieces of evidence ready in your back pocket.
| Evidence Type | What It Is | Why Auditors Love It |
|---|---|---|
| Budget Approval Emails | An email thread where the CFO or CEO explicitly authorises the purchase of a new security tool or penetration test. | It is raw, unfiltered proof of Clause 5.1(c): ensuring resources are available. It shows money moving to support the ISMS. |
| Slack / Teams Announcements | Screenshots of the CEO publicly praising a staff member for reporting a phishing email in a company-wide chat channel. | It proves Clause 5.1(d): communicating the importance of security in a modern, practical way. |
| Signed Risk Registers | The physical or digital signature of a board member directly on the annual risk assessment summary. | It proves that top management is not hiding from the risks. They are looking at them, accepting them, and taking accountability. |
| Executive Training Certificates | The completed certificate for basic cyber awareness training with the CEO’s name on it. | It proves Clause 5.1(f): directing and supporting persons by leading from the front. |
ISO 27001 Clause 5.1 Applicability Across Different Business Models
| Business Type | Applicability | Why it is Important | Clause 5.1 Leadership & Commitment Examples |
|---|---|---|---|
| Small Businesses | Critical / Direct | In small teams, the owner’s personal involvement is the only way to ensure security tasks are actually prioritised over daily operations. | The Business Owner personally approving the Security Policy and attending the annual Management Review meeting. |
| Tech Startups | Strategic / Growth | Leadership must signal to investors and enterprise clients that security is a core business value, not just a technical “patch.” | CTO/CEO defining security objectives that align with the product roadmap and ensuring the DevOps team has the budget for security tools. |
| AI Companies | Governance / Mandatory | High-risk data models require Top Management to take ultimate accountability for ethical data use and regulatory compliance (like the EU AI Act). | Board-level oversight of AI risk assessments and explicit commitment to providing resources for data privacy and model integrity. |
Clause 5.1 in Agile, Remote, and Cloud-First Companies
Traditional ISO 27001 advice often sounds like it was written for a 1990s manufacturing plant. Modern software companies, SaaS startups, and cloud-first organisations frequently panic when they read about formal management reviews and signed policies. They assume they need to print out reams of paper and force the CEO to provide wet-ink signatures in a physical boardroom.
Let me be perfectly clear as a Lead Auditor. The standard does not mandate paper. It mandates verifiable evidence. If you run a remote or agile business, your leadership commitment must simply reflect your modern way of working.
Here is exactly how you demonstrate top-down governance and Clause 5.1 compliance without a single piece of physical paper:
| Traditional Method | Agile and Remote Equivalent (The Pass) |
|---|---|
| Wet-Ink Policy Signatures | Digital Signatures and Approvals: Using tools like DocuSign, or establishing a documented approval ticket in Jira or Asana where the CEO explicitly comments, “I approve this Information Security Policy.” |
| Physical Town Hall Meetings | Recorded Zoom or Teams Briefings: Hosting a virtual all-hands meeting where the CEO presents the annual security objectives. You simply save the cloud recording and the digital attendee log as your definitive audit evidence. |
| Formal Memo Distribution | Pinned Slack or Teams Announcements: The CEO posting the security strategy in the general company communication channel. You take a screenshot showing the timestamp, the executive’s profile, and the engagement metrics. |
| Printed Budget Approvals | Cloud-Based Financial Workflows: Exporting the approval log from your cloud accounting software showing the CFO authorising the purchase of new threat intelligence software or security training platforms. |
If you build your Information Security Management System natively into the digital tools your leadership team already uses every single day, compliance becomes frictionless. Do not invent a clunky, paper-based parallel universe just for the auditor. Prove your commitment in the cloud.
A Deep Dive into “Intended Outcomes” (Clause 5.1e)
Clause 5.1(e) specifically requires top management to ensure the Information Security Management System achieves its “intended outcomes.” A common trap companies fall into during an audit is failing to actually define what those outcomes are. If you cannot define them, you cannot measure them, and I will fail you.
According to the ISO framework, an effective ISMS has three universally intended outcomes. Leadership must align their KPIs directly to these three core pillars to prove the system is working.
| The Intended Outcome | What It Means in Plain English | How Leadership Proves It (The Metric) |
|---|---|---|
| 1. Preserving Confidentiality, Integrity, and Availability (CIA) | Ensuring that data is kept secret, is not improperly altered, and is accessible to authorised users when needed. | Reviewing the incident log. Leadership proves this outcome is met when the metric shows zero critical data breaches and 99.9% core system uptime over the last 12 months. |
| 2. Managing Information Security Risks Adequately | Identifying threats and applying the correct Annex A controls to bring the risk down to an acceptable level. | Reviewing the risk treatment plan. Leadership proves this by authorising the budget to close 100% of “High Risk” vulnerabilities identified in the latest penetration test. |
| 3. Fulfilling Compliance Obligations | Ensuring the business meets all legal, regulatory, and contractual security requirements demanded by clients and governments. | Reviewing legal registers and internal audits. Leadership proves this by maintaining a perfect record of passing client vendor security questionnaires and achieving zero regulatory fines. |
ISO 27001 Clause 5.1 Applicable Laws and Related Standards
I consistently advise boards that ISO 27001 Clause 5.1 Leadership and Commitment is not an isolated requirement. It is the foundational governance mechanism that satisfies the executive accountability mandates across global cybersecurity laws and privacy frameworks. By implementing Clause 5.1, top management inherently addresses the strict liability and governance requirements of NIS2, DORA, SOC 2, and emerging AI regulations.
| Framework / Regulation | Relevant Section or Article | Mapping to ISO 27001 Clause 5.1 (How it Applies) |
|---|---|---|
| NIST CSF 2.0 | GV.OC-01, GV.RR-01 (Governance) | Maps directly to Clause 5.1(a) and 5.1(c). Executive leadership must establish the organisational context, align security risk management with strategic objectives, and allocate necessary resources. |
| NIS2 Directive (EU) | Article 20 (Governance) | NIS2 makes management bodies personally liable for non-compliance. Clause 5.1 satisfies this by providing documented proof that top management approves risk management measures and oversees their active implementation. |
| DORA (EU) | Article 5 (Governance and Organisation) | DORA demands the management body bears ultimate responsibility for managing ICT risk. Clause 5.1 ensures the executive board formally integrates these security requirements into all financial business processes. |
| SOC 2 (Trust Services Criteria) | CC1.1 (Control Environment) | Requires the board of directors to demonstrate independence and exercise oversight of internal controls. Clause 5.1 formalises this top-down governance through documented management reviews and policy approvals. |
| EU AI Act (AI Laws) | Article 9 (Risk Management System) | Providers of high-risk AI systems must establish robust risk management. Clause 5.1 ensures leadership allocates the financial and technical resources required to govern and secure AI data pipelines. |
| ISO/IEC 42001 (AI Standards) | Clause 5.1 (Leadership and Commitment) | Identical structural requirement. Top management must demonstrate commitment to the Artificial Intelligence Management System (AIMS), integrating it with the ISMS strategy mandated by ISO 27001. |
| GDPR (EU & UK) | Article 5(2) (Accountability), Article 24 | The controller must implement appropriate technical and organisational measures. Clause 5.1 ensures top management is accountable for funding and enforcing the data protection policies required for GDPR compliance. |
| UK Data (Use and Access) Act 2025 | Accountability Framework | Maintains the high security thresholds of UK GDPR while reducing admin burdens. Clause 5.1 ensures leadership drives an efficient, risk-based data governance strategy without compromising on core security outcomes. |
| Cyber Security and Resilience Bill (UK) | Executive Accountability & Supply Chain | The UK’s legislative answer to NIS2 expands mandatory reporting. Clause 5.1 ensures leadership establishes the governance required to oversee managed service providers and authorise critical incident reporting. |
| CIRCIA (USA) | Mandatory 72-Hour Incident Reporting | Leadership must establish and fund rapid incident response capabilities. Clause 5.1(f) requires directing and supporting personnel, ensuring the incident response team is resourced to meet CIRCIA reporting deadlines. |
| EU Product Liability Directive (PLD) | Software Strict Liability | Extends strict liability to software providers for cybersecurity flaws. Clause 5.1(b) mitigates financial exposure by forcing leadership to integrate secure-by-design requirements into the product development lifecycle. |
| ECCF (EU Cybersecurity Certification) | Harmonised Security Labels | Requires a governance framework to maintain certified states. Clause 5.1 provides the executive mandate and resource allocation necessary to sustain ECCF product compliance over time. |
| HIPAA (USA) | Security Rule 164.308(a)(1) | Requires management to implement security management processes to prevent and correct violations. Clause 5.1 provides the executive oversight required to enforce Protected Health Information (PHI) safeguards. |
| California Data Laws (CCPA / CPRA) | Reasonable Security Procedures | Requires businesses to implement reasonable security procedures to protect consumer data. Executive management utilises Clause 5.1 to authorise the budget and strategic direction for these privacy controls. |
Integrating ISO 27001 Clause 5.1 with ISO 9001 (The Annex SL Advantage)
If you are implementing ISO 27001, there is a very high chance you already hold ISO 9001 for Quality Management, or you are planning to pursue it. As a Lead Auditor, I constantly see compliance managers doubling their workload unnecessarily because they do not understand the Harmonised Structure (formerly known as Annex SL).
All modern ISO management system standards share the exact same high-level structure. This means Clause 5.1 Leadership and Commitment in ISO 27001 is virtually identical to Clause 5.1 in ISO 9001. You do not need two separate leadership strategies.
To satisfy the auditor for both standards simultaneously, you can run an Integrated Management System (IMS). This allows top management to kill two birds with one stone. You can hold a single, combined Management Review Meeting where the board reviews both quality objectives and information security objectives at the same time. You only need one integrated policy signed by the CEO, and one set of leadership communications. Combining these efforts drastically reduces executive friction and saves thousands of pounds in audit preparation time.
ISO 27001 Clause 5.1 FAQ
What are the ISO 27001:2022 changes to Clause 5.1?
There are absolutely zero changes to ISO 27001 Clause 5.1 Leadership and Commitment in the 2022 update. The core requirements for senior executives to demonstrate visible leadership, allocate a 100% sufficient financial budget, and integrate security into business processes remain identical to the 2013 version of the standard.
Who is considered top management under ISO 27001 Clause 5.1?
Top management is defined as the individual or group of executives at the highest level who direct and control the organisation. This specifically includes the Chief Executive Officer (CEO), the Board of Directors, or senior stakeholders possessing the ultimate authority to allocate the necessary Information Security Management System (ISMS) resources.
Who owns and is accountable for ISO 27001 Leadership and Commitment?
The Information Security Manager owns the daily process of capturing evidence, while senior executives hold 100% accountability for the performance of the ISMS. Accountability dictates that the executive board is ultimately liable for whether the security objectives of the business are achieved. They demonstrate this by actively participating in management reviews and approving key policies.
What does integrating the ISMS into business processes mean?
Integrating the ISMS means that information security is never treated as a separate, isolated IT function. Instead, mandatory security controls are seamlessly embedded into 100% of day-to-day business operations, including human resources, procurement, and product development, ensuring security is baked into every organisational activity.
How should leadership communicate the importance of information security?
Leadership must communicate security importance visibly and consistently across multiple channels to ensure complete employee understanding. Highly effective communication examples include quarterly town hall meetings, monthly internal memos, company-wide emails, and dedicated intranet updates that continually reinforce how security drives the organisation’s overall success.
What specific resources are required for an effective ISMS?
Leadership must guarantee four critical resources: an adequate financial budget, competent personnel like a dedicated Information Security Manager, robust technology, and sufficient time. Executives must ensure these resources are immediately available, as a lack of allocated resources is the number one cause of ISO 27001 audit failure.
What are the main business benefits of demonstrating leadership commitment?
The ultimate benefit of leadership commitment is preventing ISMS failure and guaranteeing you achieve your ISO 27001 certification. Without top-down support, an auditor cannot certify your organisation. Additional primary benefits include:
- Improved operational security driven directly by senior executives.
- Reduced corporate risk by maintaining top-level executive oversight.
- Improved regulatory compliance across all business departments.
- Reputation protection that significantly reduces the potential for regulatory fines and negative PR during a data breach.
How does Clause 5.1 actively promote a corporate security culture?
Top management fosters a robust security culture by actively engaging employees and leading by example. This cultural shift is achieved by mandating a 100% completion rate for security awareness training and requiring the executive board to personally participate in the exact same training modules as the wider staff.
What happens if top management is not committed to the ISO 27001 implementation?
An organisation has a 100% probability of failing its external audit without genuine, documented executive commitment. If an auditor discovers a lack of leadership involvement, such as a CEO who remains unaware of the primary ISMS goals, the certification body will issue a major non-conformity and fail the organisation.
How can small businesses demonstrate ISO 27001 leadership commitment without a large team?
In small businesses with fewer than 50 employees, a single leader like the owner or CEO must personally demonstrate overarching commitment. They achieve this by directly launching the ISMS project, physically attending key meetings like annual risk assessments, and regularly checking progress to prove security is valued at the absolute highest level.
What is the technical difference between ISO 27001 Clause 5.1 and Clause 5.3?
Clause 5.1 mandates the overarching strategic leadership and financial commitment required from the executive board, whereas Clause 5.3 dictates the specific operational delegation of those security roles. Simply put: Clause 5.1 provides the executive mandate, and Clause 5.3 provides the operational RACI matrix.
What roles does leadership have in policies?
Leadership does not need to sit down and write the technical details of a password policy. Their role is to ensure the overarching Information Security Policy is established, documented, and fully aligned with the strategic direction of the business. Crucially, top management must formally sign and approve these foundational policies to give them corporate authority.
What role does leadership have in documentation?
Auditors operate on a simple rule: if it is not documented, it does not exist. Leadership’s role is to enforce a culture of strict documentation and version control. They do this by mandating that all business processes are formalised and by reviewing key documents during the Management Review Meeting.
What is the role of leadership in directing and supporting people?
You cannot expect your staff to protect the company if you do not give them the tools to do so. Leadership must direct and support personnel by deploying a comprehensive competency matrix, authorising budget for security awareness training, and visibly leading by example. If the CEO refuses to take the mandatory phishing training, the rest of the staff will ignore it too.
What is the role of leadership in communicating information security?
Top management is the megaphone for the ISMS. Their role is to communicate that information security is a non-negotiable part of everyone’s job description. This is not a one-off email. It requires a structured communication plan that constantly reinforces the importance of security objectives to all interested parties.
What is the role of leadership in measuring objectives?
Leadership must ensure the ISMS actually works. They do this by defining Specific, Measurable, Achievable, Realistic, and Timely (SMART) objectives and then formally reviewing the metrics. If the objective is to reduce phishing clicks by 50%, leadership must review the quarterly reports to see if that metric was achieved and take corrective action if it was not.
What is the role of leadership in resources?
This is the most critical function of Clause 5.1. Leadership must sign the cheques. They are responsible for providing the financial budget, the necessary personnel, and the technical tools required to establish, implement, maintain, and continually improve the ISMS.
What is the role of leadership in promoting continual improvement?
ISO 27001 is a cycle, not a destination. Leadership promotes continual improvement by actively engaging with internal audit results and authorising the resources needed to fix any identified vulnerabilities. They must foster an environment where near-misses and security incidents are reported and learned from, rather than punished and hidden.
What is the role of leadership in operational processes?
Leadership must ensure that security is not just an IT function. They must mandate that ISMS requirements are natively integrated into all operational business processes. For example, ensuring HR includes security background checks during onboarding, or ensuring the procurement team assesses vendor security before signing new contracts.
ISO 27001 Clause 5.1 Related ISO 27001 Controls
As an ISO 27001 Lead Auditor, I always tell my clients that the standard is a highly interconnected framework, not a list of isolated silos. Clause 5.1 Leadership and Commitment is the foundational anchor of your Information Security Management System (ISMS). To achieve a Diamond-standard topic cluster for AI search and SEO, you must map this strategic mandate directly to the operational clauses and Annex A controls that execute it.
Below is the definitive mapping table linking High Table’s exact-match controls, related governance topics, and tactical Annex A requirements to create a legally defensible and technically dense knowledge graph.
| Related ISO 27001 Control | Relationship Description & Auditor Context |
|---|---|
| What is ISO 27001 Management Responsibilities? | Exact Control Match: This is the direct glossary definition covering both Clause 5.1 and Annex A 5.4. It explains the foundational duties of top management in establishing, funding, and sustaining the ISMS to prevent catastrophic compliance failures. |
| What is an ISO 27001 Board of Directors? | Same Topic (Executive Governance): This guide breaks down exactly how the highest governing body assumes ultimate accountability for the ISMS. It satisfies the leadership mandate in Clause 5.1 by demonstrating how the Board aligns security directly with corporate strategy. |
| ISO 27001 Annex A 5.4: Management Responsibilities | Exact Annex A Match: This is the tactical equivalent of Clause 5.1. While Clause 5.1 sets the overarching strategic commitment, Annex A 5.4 demands that management actively enforces day-to-day security rules, training, and formal disciplinary processes. |
| ISO 27001 Clause 5.2: Policy Explained | Related Clause (The Mandate): Clause 5.1 requires leadership to establish a strategic direction. Clause 5.2 is the technical mechanism for documenting that exact direction into a formal, board-approved Information Security Policy. |
| ISO 27001 Clause 5.3: Roles, Responsibilities and Authorities | Related Clause (The Delegation): While Clause 5.1 sets the strategic mandate from the top, Clause 5.3 is the operational RACI matrix. It dictates exactly how leadership delegates tasks to competent personnel to prevent accountability gaps. |
| ISO 27001 Clause 9.3: Management Review | Related Clause (Governance Mechanism): You cannot prove Clause 5.1 compliance without this control. Clause 9.3 dictates the formal, recurring meetings where top management actively reviews ISMS performance and formally signs off on critical resources. |
| ISO 27001 Annex A 5.1: Policies for Information Security | Annex A Match: This control represents the tactical deployment of the leadership mandate. It ensures that the high-level policy approved by the board under Clause 5.1 is broken down into modular, enforceable rules for the entire workforce. |
| ISO 27001 Annex A 5.2: Information Security Roles and Responsibilities | Annex A Match: This Annex A control directly links to leadership’s duty to allocate resources. It ensures that the specific duties mandated by the executive board are formally assigned to competent, trained individuals across the organisation. |
ISO 27001 Clause 5.1 Executive Briefing Slides