An ISO 27001 checklist or ISO 27001 checklist PDF can quickly help you orientate to the standard. Let’s look at some quick and easy ISO 27001 checklists and a totally free ISO 27001 checklist PDF that can fast track you. I am Stuart Barker the ISO 27001 Lead Auditor and this is ISO 27001 Checklists.
I am also going to give you a totally free ISO 27001 Implementation Guide. A complete guide to implementing ISO 27001. For free. So at the end of this you will have the implementation guide and the checklist and will be able to implement ISO 27001 yourself. I am not even going to ask you for your email address.
Table of contents
What is an ISO 27001 Checklist?
Before we jump in with the ISO 27001 checklists and free ISO 27001 Checklist that you can download and use straight away it is worth a quick word on what and ISO 27001 checklist is not, rather than what it is. It is not a substitute for getting a copy of the standard. If you are serious about ISO 27001 certification get a copy of the standard. Right, now that is out of the way, onto the ISO 27001 checklists that should save you time and money.
ISO 27001 Toolkit for Business.
With the Ultimate ISO 27001 Toolkit you are in good company. Downloaded thousands of times getting businesses just like you ISO 27001 certified at the speed of light and at a fraction of the costs.
You even get a weekly 1 hour Q and A session included. So you are not on your own.
Free ISO 27001 Implementation Checklist xls
I am going to give you a free ISO 27001 Implementation Checklist xls and I am not even going to ask you for your email address. It is a totally free ISO 27001 Implementation checklist.
What the free ISO 27001 Implementation Checklist xls Covers
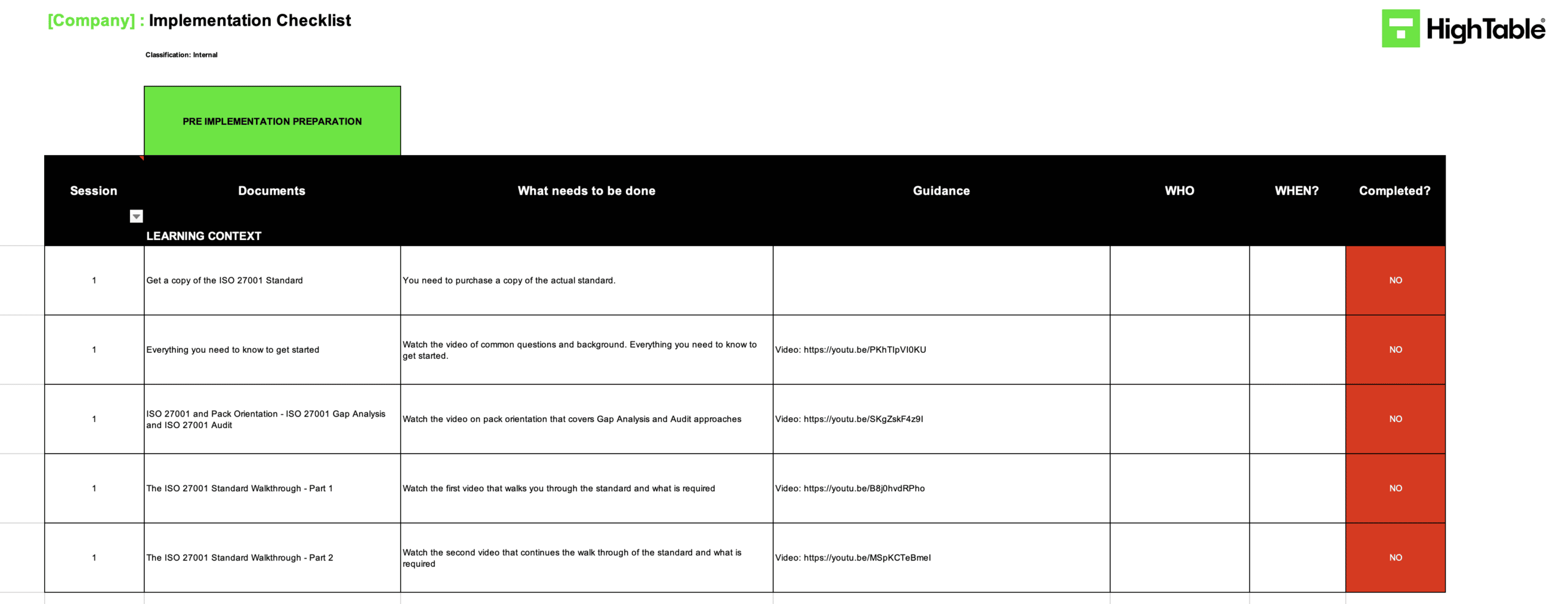
The checklist is designed to give you the ISO 27001 implementation steps. Sure you can tick them off as you go but as well as that it gives you detailed guides and videos to help you with each step. For free. Am I mad giving you this? Perhaps. But if it helps you then we are all good.
The summary of the ISO 27001 steps covered:
- PRE IMPLEMENTATION PREPARATION
- BRAND YOUR DOCUMENTS
- ASSIGN YOUR TEAM
- DOCUMENT YOUR POLICIES
- TRAIN EVERYONE
- DOCUMENT WHO YOU ARE AND WHAT YOU HAVE
- DOCUMENT YOUR INFORMATION SECURITY SYSTEM
- CREATE YOUR PLANS
- CONDUCT YOUR RISK REVIEW
- IMPLEMENT YOUR OPERATIONAL PROCESSES
- PLAN AND CONDUCT YOUR BUSINESS CONTINUITY
- CONDUCT YOUR INTERNAL AUDIT
- HOLD YOUR MANAGEMENT REVIEW MEETING
- COMMUNICATE YOUR NEW INFORMATION SECURITY MANAGEMENT SYSTEM
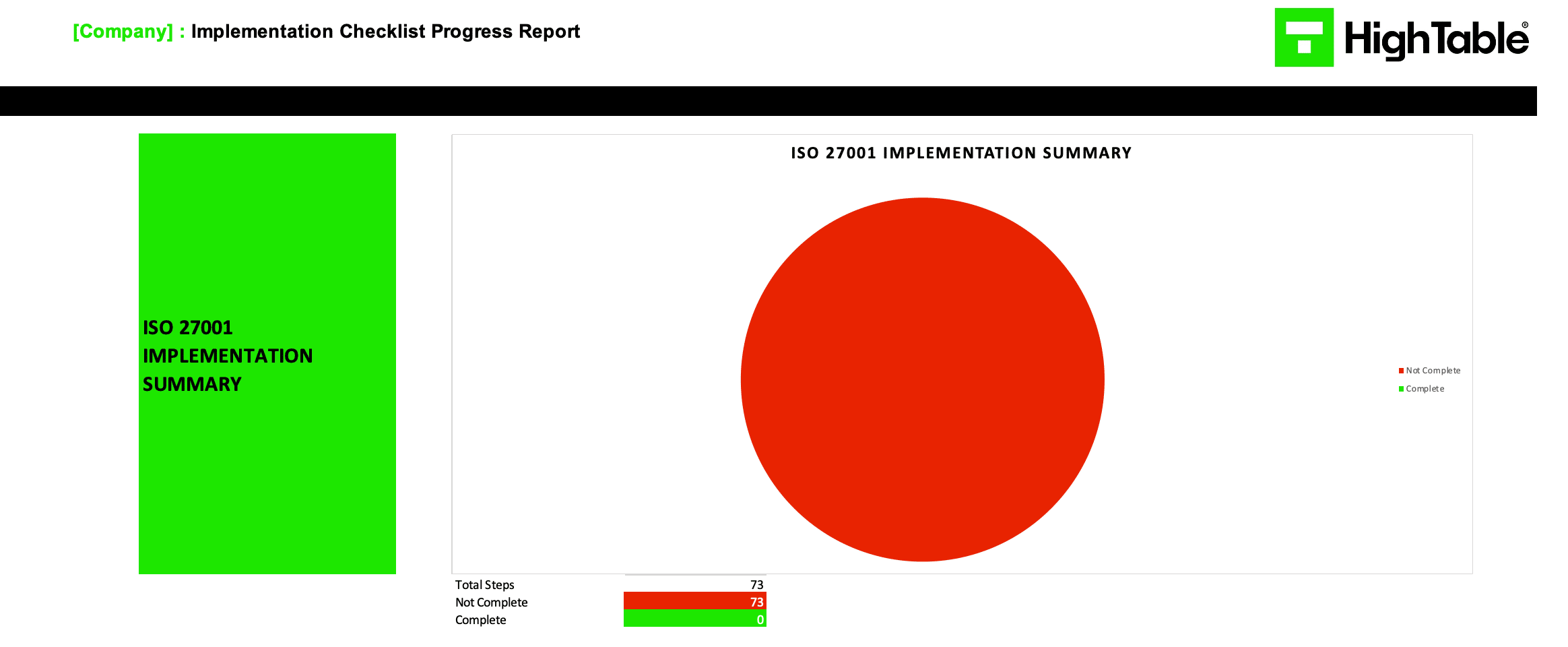
ISO 27001 Checklist Dashboards
You are getting an ISO 27001 Summary Dashboard so you can track your progress and you are getting ISO 27001 Dashboards for each of the steps so you can track the progress of each step. How cool is that? For free you say? Yes.
ISO 27001 Checklist Example
It might help to show you an example of the ISO 27001 Checklist.
Download FREE ISO27001 Implementation Guide
The Complete ISO27001 Implementation Guide.
Your free ISO27001 Implementation Guide is a click away.

Download FREE ISO27001 Checklist XLS
The Wait is Over.
We don’t even want your email address.
Download FREE ISO27001 Checklist PDF
The PDF Versions of the totally free ISO 27001 Checklist.
We still don’t want your email address.

ISO 27001 Checklist FAQ
The totally free ISO 27001 Checklist PDF is located here: https://hightable.io/iso27001-checklist/
The totally free ISO 27001 Checklist xls is located here: https://hightable.io/iso27001-checklist/
No. It is totally free and you do not need to provide your email address.
If you follow the ISO 27001 checklist you will have an ISO 27001 Information Security Management System and be ISO 27001 Certification Ready.
Yes, the ISO 27001 Checklist meets the requirements of ISO 27001:2022
Yes, the ISO 27001 Checklist meets the requirements of ISO 27002:2022
Yes the ISO 27001 checklist is backward compatible with ISO 27001:2013 and ISO 27001:2017
No catch. If you like it and it helps you might come back and we can help you some more. We don’t want your email address as we have no interest in marketing to you.
ISO 27001 Checklist Top 6 Must Knows
Let me add some more value by sharing the top 6 must knows for your ISO 27001 checklist.
1. Information Security Policy
Your information security policy is the document that shows exactly how your company stores and manages data.
It refers to the business on a companywide scale.
You will need to detail which employees have access to the data in your company, how often they have access, and the processes involved with individuals handling this data.
In a more basic sense, your information security policy should highlight your company’s antivirus management, your backup systems, data support operations data recovery process, and data retention.
You will also need to display evidence that your staff is trained in all of these areas.
As a result, you can show the auditor that your team is fully informed on what to do when it comes to data management and what not to do.
2. Information Security Risk Assessment
If the information security policy part of this assessment was the theoretical side of ISO 27001, the information security risk assessment is the practical.
This process is designed to assess how well your security controls work.
You will test your systems from a cyber attacker’s point of view, revealing weaknesses that people on the outside can exploit.
The reason for this isn’t to demonstrate how you have failed, but rather to focus on what can be improved.
The best way to show off your cybersecurity protocols is with an attack, and it is better to identify holes in your processes in a controlled environment like this than experience a real case of cybercrime.
What’s more, you can go on to fix any issues that present themselves which will only bolster your security measures.
3. Treatment Plan
The next step in your assessment is the information security treatment plan.
This treatment plan is used as a way to perfect any holes that were dug up during the risk assessment.
Anyone new to cybersecurity or the ISO 27001 as a whole is going to find the process very confusing.
That is why it is necessary to perform these practical assessments first and fix things before it is too late.
Your ISO 27001 consultant is going to know exactly how to tackle any holes that arise.
The point of these tests is to show that your company has the right cybersecurity protocols in place.
Therefore, you need to treat any issues that are going to prevent this.
4. Statement Of Applicability
The statement of applicability is used to demonstrate what issues your company faced during the risk assessment and what controls were put in place to prevent them.
Basically, it is proof that you know what cybersecurity risks your business is prone to and how you plan on defending your data.
This documentation is filled out using another step-by-step process.
First, you need to outline what issues were found and why.
Next, you will be asked to provide evidence of your implanted controls and explain why.
This part is fairly self-explanatory; however, you may want to be more specific about your reasoning.
Simply stating that the security protocols were put in place to protect your confidential data isn’t enough.
Try to demonstrate applied knowledge where possible to show that you can deal with these issues without an auditor present.
The last step is recognising what problems did not come up during the test and why.
The main reason that these issues did not show up is going to be because you already had the right cybersecurity processes in place.
Again, this demonstrates that you know how to deal with these security issues on your own.
Try to be as detailed as possible, recognising where your strengths are when it comes to data protection.
5. Information Security Objectives
There are three main focuses of cybersecurity, and you must familiarise yourself with all three if you are to achieve ISO 27001 certification.
The first of these criteria is confidentiality.
Are you aware of what is classified as confidential information? Learning this step will showcase that you know how vital it is to protect this type of data.
The second criterion is known as integrity.
This highlights that you know that information can be doctored and that you have been honest in your approach to cybersecurity.
In other words, it shows that you have not falsified any documents.
The last criterion is availability.
This part demonstrates that people will have access to your business data when they need it and that you can provide it in the event of a disaster.
6. Evidence Of Compliance
This is the last document that you will need to worry about during this process, and all it does is wrap all of the evidence of the processes listed above.
This means that you have put all of the tools and procedures in place to protect the data of your business and anyone else that communicates with you. Think of this part as your final results.
The main thing that your clients will look at is your evidence of compliance.
It must be signed by an independent body, which removes any suspicions regarding fraud.
In the end, your evidence of compliance will prove that you have undergone the full checklist to become a fully-fledged and certified ISO 27001 holder.
Conclusion
All of this information may seem intimidating on the surface but try to remember that there are people out there that can help you with your ISO 27001. At the very least, this article should have given you a fundamental understanding of what goes into a cybersecurity assessment and why. There is a method to the madness, and assessments like these are only going to be more necessary as time moves on. Make sure that you get a head start and sort out your ISO 27001.
About the author




