The ISO 27001 Clause 4.1 Understanding The Organisation And Its Context Audit Checklist.
The ISO 27001 Clause 4.1 audit checklist is designed to help an ISO 27001 Lead Auditor conduct internal audits and external audits of ISO 27001 Clause 4.1.
It complements the guide – How to audit ISO 27001 Clause 4.1
Use this checklist to simulate a certification audit and identify non-conformities regarding the Context of the Organization before the external auditor arrives.
Table of contents
Introduction
The ISO 27001 Clause 4.1 Audit Checklist
Time needed: 2 hours
ISO 27001 Clause 4.1 Understanding The Organisation And Its Context Audit Checklist
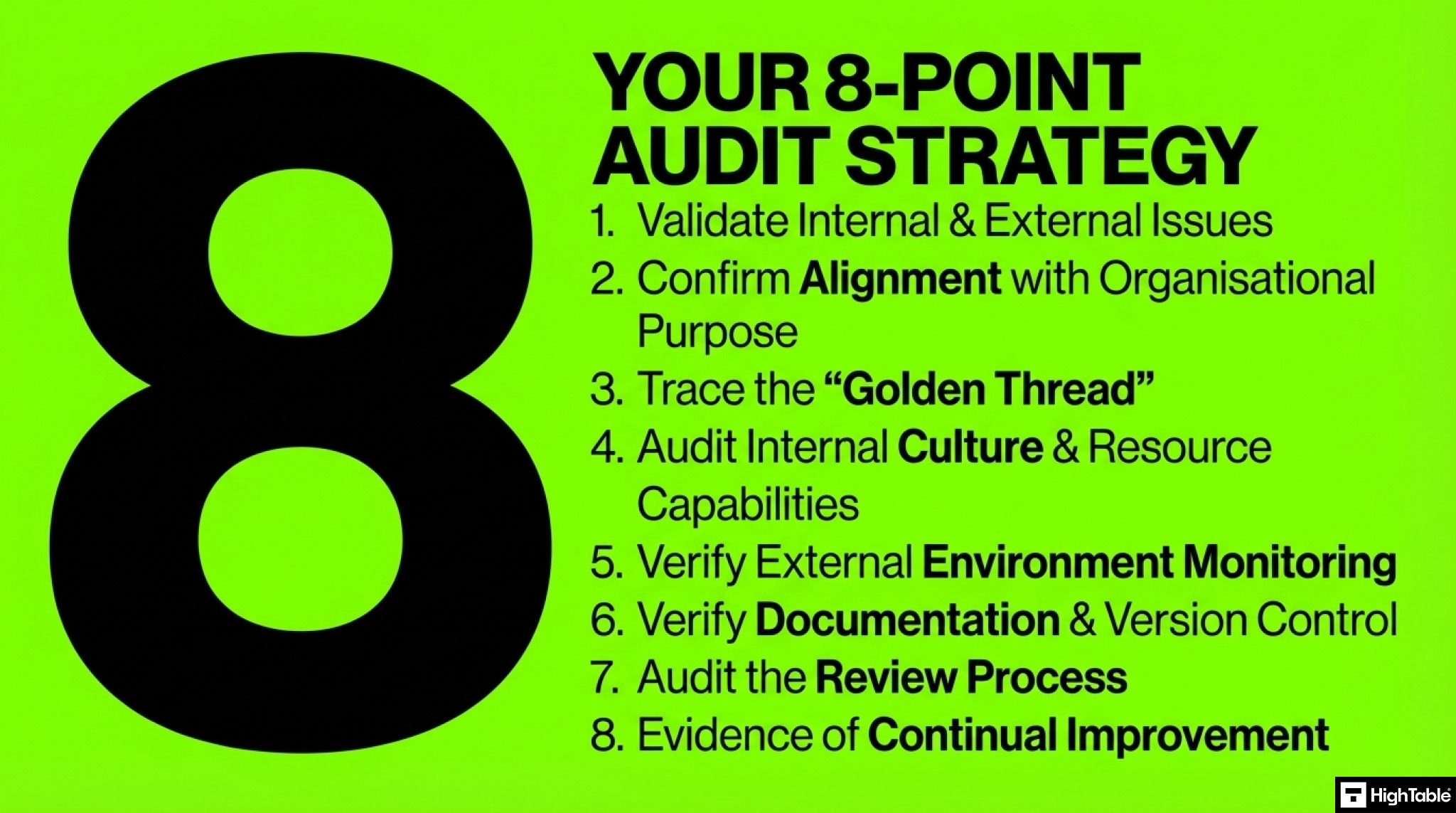
- Validate Internal & External Issues (The Core Requirement)
Objective: Ensure the organization has explicitly determined the internal (culture, resources) and external (legal, market, threat landscape) issues that affect its ability to achieve ISMS outcomes.
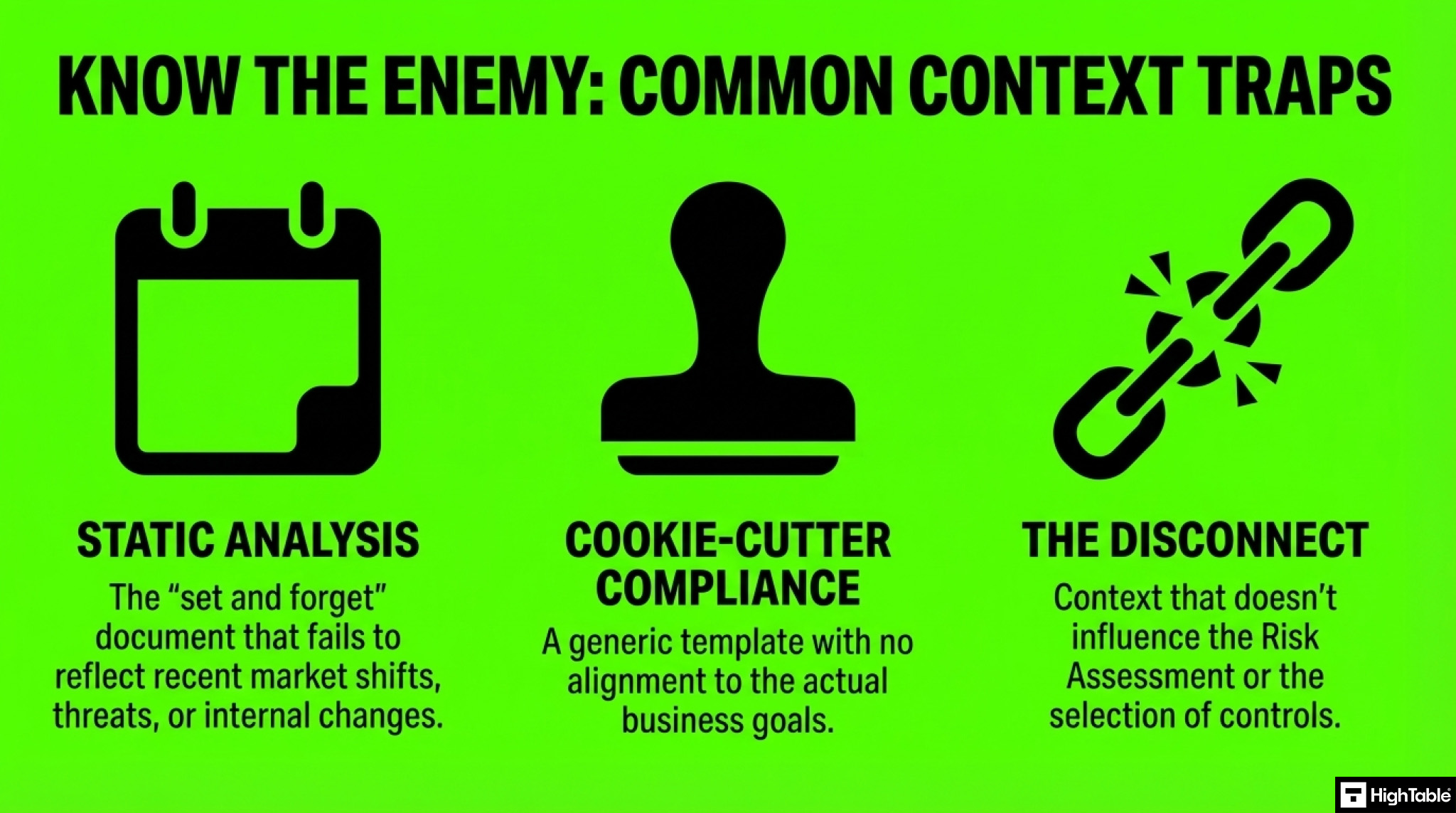
The Challenge: Static analysis. Auditors often find “Context” documents written years ago that were never updated to reflect new market threats, economic shifts, or internal restructuring.
Audit Technique: Examine Strategic Plans, SWOT Analyses, or PESTLE analysis documents. Challenge management on how recent changes (e.g., a new product launch, a change in legislation, or a move to remote work) are reflected in the documented context. - Confirm Alignment with Organisational Purpose
Objective: Verify that the ISMS is not generic but directly aligned with the organization’s strategic direction as required by Clause 4.1.
The Challenge: “Cookie-cutter” compliance. The security context looks like a downloaded template and doesn’t reflect the actual business goals (e.g., a startup prioritizing speed to market vs. a bank prioritizing data integrity).
Audit Technique: Interview Senior Management. Ask them to explain how the ISMS supports specific business objectives found in their Mission Statement or Annual Report. If the business goal is “Rapid AI Adoption,” does the Context analysis list “AI Security Risks” as a key issue? - Trace the “Golden Thread” (Context > Risk > Control)
Objective: Confirm that the issues identified in Clause 4.1 actually influenced the Risk Assessment and Statement of Applicability (SoA). This proves the Context is functional, not just paperwork.
The Challenge: The “Disconnect.” The Context document lists “Ransomware” as a critical external issue, but the Risk Register has no specific risks or controls addressing it.
Audit Technique: Perform a Traceability Audit. Pick one high-priority external issue (e.g., “GDPR Compliance” or “Supply Chain Instability”).
Ask to see where this appears in the Risk Register (Clause 6.1).
Trace it to the specific Annex A Control selected to mitigate it. If the thread breaks, raise a Non-Conformity. - Audit Internal Culture & Resource Capabilities
Objective: Verify that “Internal Issues” go beyond just hardware. They must include organisational culture, knowledge, and resource availability.
The Challenge: Ignoring the “Human Factor.” The organization documents its servers and software but fails to document that they have a high staff turnover rate or a culture of “shadow IT.”
Audit Technique: Review HR reports or interview department heads. If the organization has recently downsized or merged, check if the “Internal Context” has been updated to reflect the loss of institutional knowledge or changes in reporting lines. - Verify External Environment Monitoring (Legal & Technological)
Objective: Ensure the organization monitors the broader environment, including legal, technological, and competitive factors.
The Challenge: Blind spots. The organization focuses heavily on competitors but ignores upcoming regulatory changes (like DORA or NIS2) or technological shifts (like the end-of-life of a critical software dependency).
Audit Technique: Ask for the sources of their external intelligence. Do they subscribe to legal updates? Do they receive threat intelligence feeds? Verify that these inputs are actually recorded in the Context analysis. - Verify Documentation & Version Control
Objective: Confirm that the “Context of Organization” is documented information that is controlled, maintained, and retained.
The Challenge: Informal knowledge. “We know our context” is not evidence. If it isn’t written down, it doesn’t exist for the auditor.
Audit Technique: Examine the Documented Information for version control (dates, authors). If the document date is two years old, ask: “Has nothing in the world or your business changed in 24 months?” - Audit the Review Process (Dynamic Monitoring)
Objective: Ensure that the context is reviewed at planned intervals or when significant changes occur.
The Challenge: “Set and Forget.” The organization treats Context as a one-time setup task rather than a dynamic monitoring process.
Audit Technique: Examine Management Review Minutes (Clause 9.3). Look for evidence that “Changes in external and internal issues” is a standing agenda item and that valid discussions actually took place regarding recent events. - Evidence of Continual Improvement
Objective: Confirm that updates to the context analysis lead to tangible improvements in the ISMS.
The Challenge: Analysis paralysis. The organization identifies new threats or issues but fails to open Corrective Actions or update controls to address them.
Audit Technique: Review the Improvement Log. Look for a clear link between a change in context (e.g., “We adopted a remote-first policy”) and a security improvement (e.g., “We implemented Endpoint Detection and Response (EDR) and updated the Mobile Device Policy”).
Further Reading
How to implement ISO 27001 Clause 4.1
ISO 27001 Clause 4.1 Implementation Checklist
How to audit ISO 27001 Clause 4.1
ISO 27001 Clause 4.1 Audit Checklist
ISO 27001:2022 Amendment 1 – Absolutely Everything You Need to Know
ISO27001:2022 Amendment 1 Climate Action Changes – Definitive Briefing
ISO 27001 Clause 4.1 Understanding the Organisation and Its Context Explained
ISO 27001 Clause 4.1 Understanding the Organisation and Its Context Explained
About the author