ISO 27001 Clause 4.1 is a security control that mandates organizations to identify and document internal and external issues relevant to their context. This requirement ensures that the Information Security Management System (ISMS) aligns with strategic direction, addressing risks like regulatory changes, market trends, and organizational culture to achieve compliance and operational resilience.
In this guide, I will show you exactly how to implement ISO 27001 Clause 4.1 and ensure you pass your audit. You will get a complete walkthrough of the control, practical implementation examples, and access to the ISO 27001 templates and toolkit that make compliance easy.
I am Stuart Barker, an ISO 27001 Lead Auditor with over 30 years of experience conducting hundreds of audits. I will cut through the jargon to show you exactly what changed in the 2022 update and provide you with plain-English advice to get you certified.
Key Takeaways
- Internal and external issues are risks to the information security management system.
- You identify them by doing a brainstorming session
- You manage them via risk management
Table of contents
- Key Takeaways
- What is ISO 27001 Clause 4.1?
- What is the 2024 Climate Change Amendment?
- Exactly How to Document Climate Change for Clause 4.1
- ISO 27001 Clause 4.1 Free Training Video
- ISO 27001 Clause 4.1 Explainer Video
- ISO 27001 Clause 4.1 Podcast
- How Clause 4.1 Applies to Different Business Models
- Integrating Clause 4.1 with ISO 9001 and 14001
- What are ISO 27001 internal issues?
- What are ISO 27001 external issues?
- How to implement ISO 27001 Clause 4.1
- Facilitation Guide: How to Run a Clause 4.1 Workshop
- ISO 27001 Clause 4.1 Implementation Checklist
- How to audit ISO 27001 Clause 4.1
- Technical Artifact Preview: The ISO 27001 Context Registry
- What Evidence Must You Show the Auditor?
- ISO 27001 Clause 4.1 Audit Checklist
- Trigger-Based Updates: When to Refresh Your Context
- How to pass the ISO 27001 Clause 4.1 audit
- What an auditor looks for
- Top 3 ISO 27001 Clause 4.1 Mistakes and How to Fix Them
- The Auditor’s Choice: Using SWOT and PESTLE for Clause 4.1
- The Audit Trail: How Clause 4.1 Drives the Rest of Your ISMS
- Fast track ISO 27001 Clause 4.1 compliance with the ISO 27001 Toolkit
- How to Present Clause 4.1 to Your CEO
- ISO 27001 Clause 4.1 Applicable Laws and Related Standards
- Related ISO 27001 Controls
- ISO 27001 Clause 4.1 FAQ
- Further Reading
- ISO 27001 Clause 4.1 Executive Briefing Slides
Stop Guessing. Start Passing.
AI-generated policies are generic and fail audits. Our Lead-Auditor templates have a 100% success rate. Don’t risk your certification on a prompt

What is ISO 27001 Clause 4.1?
ISO 27001 Clause 4.1 Understanding The Organisation and Its Context is the requirement to identify and manage the internal and external issues that can affect the information security management system (ISMS) and prevent it from achieving its intended outcomes.
In ISO 27001 this is known as ISO27001:2022 Clause 4.1 Understanding The Organisation And Its Context. It is one of the mandatory ISO 27001 clauses.
Internal issues and external issues are just another way of saying risks.
Internal and external issues are risks to the information security management system and they should be identified and managed.
So the clause is asking you to consider and record what internal and external risks there are to your information security management system (ISMS). What could stop your information security management system from being able to achieve its outcomes?
ISO 27001 Clause 4.1 Understanding The Organisation And Its Context is an ISO 27001 clause that requires us to understand the internal and external issues that could impact your information security management system (ISMS).
Reference: What is ISO 27001 Clause 4.1?
Core Purpose of the Control
ISO 27001 Clause 4.1 is an Information Security Management System (ISMS) control to ensure you identify, manage and mitigate risks to the management system achieving its intended outcomes.
Official Standard Definition
The ISO 27001 standard defines ISO 27001 Clause 4.1 as:
The organisation shall determine external issues and internal issues that are relevant to its purpose and that affect its ability to achieve the intended outcome(s) of its information security management system. The organisation shall determine whether climate change is a relevant issue.
ISO27001:2022 Clause 4.1 Understanding The Organisation And Its Context
What is the 2024 Climate Change Amendment?
The standard amended the definition in February 2024. This amendment, referred to as Amendment 1: Climate action changes added climate change to ISO 27001 Clause 4.1. The standard also added the following sentence:
‘ The organisation shall determine whether climate change is a relevant issue.’
ISO27001:2022 Amendment 1
Exactly How to Document Climate Change for Clause 4.1
The 2024 Amendment to ISO 27001 Clause 4.1 added a mandatory requirement: “The organisation shall determine whether climate change is a relevant issue.” As a Lead Auditor, I am now required to look for evidence that you have specifically considered this. Simply leaving it out is now an automatic minor non-conformity.
You do not need to become an environmental expert, but you must document your conclusion in your Context Registry. Here are the two scenarios I look for during a certification audit:
Scenario A: Climate Change is Relevant
If your physical infrastructure or supply chain is at risk, you must document it like this:
“We are a SaaS provider using physical data centres located in flood-prone zones; therefore, climate change is a relevant issue for our operational continuity and the availability of our services. This issue is linked to Risk ID #104 in our Risk Register.”
Scenario B: Climate Change is Not Relevant
For many digital-first firms, climate change may not directly impact information security. However, you must still record that you checked:
“We are a 100% remote consulting firm using Tier-4 cloud providers. We have reviewed climate change and determined it does not currently impact our ability to manage information security, though we will review this annually as part of our Management Review.”
Lead Auditor Tip: The biggest mistake is thinking that if it is “not relevant,” you don’t have to write anything. The standard says you must “determine” its relevance. If there is no mention of climate change in your Clause 4.1 documentation, you have not “determined” it in the eyes of the assessor.
ISO 27001 Clause 4.1 Free Training Video
In the video ISO 27001 Clause 4.1 Understanding The Organisation And Its Context Explained I show you how to implement it and how to pass the audit.
ISO 27001 Clause 4.1 Explainer Video
In this strategic implementation briefing for ISO 27001:2022 Clause 4.1 Understanding the Context of the Organisation, ISO 27001 Lead Auditor Stuart Barker and his team talk you through what it is, how to implement in and how to pass the audit.
ISO 27001 Clause 4.1 Podcast
In this episode of The Lead Auditor Podcast, Stuart Barker breaks down exactly what the auditor is looking for when they ask about “Internal and External Issues.”
How Clause 4.1 Applies to Different Business Models
| Business Type | Applicability | Why it is Important | Clause 4.1 Content Examples (Internal & External) |
|---|---|---|---|
| Small Businesses | Foundational Requirement | Ensures the ISMS is right-sized for limited resources, preventing over-engineering while satisfying customer trust. | External: Local data protection laws (GDPR/CCPA), market competition. Internal: Limited IT headcount, reliance on key individuals, and budget constraints. |
| Tech Startups | High Priority / Strategic | Critical for passing investor due diligence and shortening sales cycles with enterprise clients who require security proof. | External: VC security requirements, rapid technological shifts in cloud infrastructure. Internal: Agile/fast-paced culture, remote-first workforce, and flat governance. |
| AI Companies | Mandatory & Complex | Necessary to manage unique risks associated with massive data ingestion, algorithmic transparency, and evolving global AI regulations. | External: Emerging AI ethics standards (EU AI Act), GPU supply chain availability. Internal: Proprietary model training data, complex data pipelines, and research-focused culture. |
Integrating Clause 4.1 with ISO 9001 and 14001
If your organisation already holds ISO 9001 (Quality) or ISO 14001 (Environment), do not create a separate context document for ISO 27001. All Annex SL standards share the same Clause 4.1 requirement.
The “One-Registry” Strategy: Create an Integrated Context Registry that covers:
- Quality Issues (9001): Customer satisfaction and process efficiency.
- Security Issues (27001): Data confidentiality and threat landscape.
- Environmental Issues (14001): Carbon footprint and waste management.
This “Single Source of Truth” reduces the administrative burden on your team and shows the auditor that your management systems are a core part of the business, not a side project.
I’ve sat in the Auditor’s chair for 20 years. These are the exact tools I use to guarantee a pass.

What are ISO 27001 internal issues?
ISO 27001 Internal Issues are threats that could hinder the effective functioning of your information security management system (ISMS). In other words, consider them as risks that could prevent the ISMS from achieving its desired outcomes.
ISO 27001 Internal Issues are inherent risks originating within an organisation that can hinder the effective functioning of its Information Security Management System (ISMS). These issues originate within your organisation and, to a large extent, are within your control. These internal risks can impede the ISMS from achieving its objectives, particularly in safeguarding the confidentiality, integrity, and availability of information assets.
Internal issues is defined as, organisational risks to the Information Security Management System (ISMS) achieving its interned outcomes.
10 Examples of Internal ISMS Risks
The following are 10 real world examples of ISO 27001 Internal Issues:
- Lack of management commitment: This can hinder the successful implementation and maintenance of the ISMS, as employees may not perceive information security as a critical organisational objective.
- Inadequate resource allocation: This can lead to gaps in security coverage, delayed responses to incidents, and an inability to implement necessary security measures.
- Lack of employee awareness and training: This can increase the risk of data breaches, system disruptions, and reputational damage.
- Poor communication and coordination: This can create silos within the organisation, hindering the collective effort to maintain information security.
- Resistance to change: This can lead to non-compliance with security measures, hindering the effectiveness of the ISMS6.
- Lack of Regular Reviews and Updates: This can lead to outdated security controls, increased vulnerability to new threats, and non-compliance with evolving standards and regulations.
- Inadequate access control management: This can lead to data breaches, system disruptions, and loss of confidentiality, integrity, and availability of information assets.
- Insufficient incident response planning: This can exacerbate the impact of security incidents, increasing the risk of data loss, system downtime, and reputational damage.
- Inadequate physical and environmental security: This can lead to data breaches, system disruptions, and loss of critical infrastructure.
- Lack of Business Continuity and Disaster Recovery Planning: This can lead to significant financial losses, reputational damage, and disruption to business operations.
By identifying and addressing these internal issues, organisations can significantly improve the effectiveness of their ISMS and enhance their overall information security posture.
What are ISO 27001 external issues?
External Issues are inherent risks originating outside an organisation that can hinder the effective functioning of its Information Security Management System (ISMS). These external risks, primarily outside the organisation’s control, can impede the ISMS from achieving its objectives, particularly in safeguarding the confidentiality, integrity, and availability of information assets.
External issues is defined as – external risks to the Information Security Management System (ISMS) achieving its interned outcomes.
10 Examples of External ISMS Risks
The following are 10 real world examples of ISO 27001 External Issues:
- Legal and Regulatory Requirements: Changes in data privacy laws (e.g., GDPR, CCPA), industry-specific regulations (e.g., HIPAA, PCI DSS), and cybersecurity frameworks (e.g., NIST Cybersecurity Framework). Non-compliance can lead to severe financial penalties, reputational damage, and loss of customer trust.
- Competitive Landscape: Actions of competitors, such as new product offerings, market share shifts, and cyberattacks targeting rivals. This can indirectly affect an organisation’s information security posture by increasing pressure to innovate and adapt, potentially leading to security vulnerabilities.
- Technological Advancements: Rapid changes in technology, such as the rise of cloud computing, artificial intelligence, and the Internet of Things. This creates new security challenges and opportunities, requiring organisations to constantly update their security controls and adapt to evolving threats.
- Economic Conditions: Economic downturns or recessions can impact an organisation’s budget, potentially leading to reduced spending on information security measures. This can weaken the organisation’s security posture, making it more vulnerable to cyberattacks.
- Social and Cultural Factors: Changing societal norms and expectations regarding data privacy and security, as well as cultural differences between countries. This can influence an organisation’s approach to information security and its reputation among stakeholders.
- Political Stability: Political instability, such as wars, conflicts, or changes in government. This can disrupt business operations and increase the risk of cyberattacks, particularly those targeting critical infrastructure.
- Natural Disasters: Natural disasters, such as earthquakes, floods, and hurricanes can damage physical infrastructure and disrupt business operations, potentially impacting the availability and integrity of information assets.
- Geopolitical Events: Global events, such as pandemics, trade wars, and geopolitical tensions can create uncertainty and disrupt supply chains, potentially affecting an organisation’s ability to maintain its information security controls.
- Cybersecurity Threats: The evolving threat landscape, including new malware, ransomware attacks, and social engineering techniques. This requires organisations to constantly adapt their security measures to stay ahead of cybercriminals.
- Stakeholder Expectations: The expectations of customers, suppliers, and other stakeholders regarding data privacy and security can influence an organisation’s information security policies and practices, as well as its reputation and brand image.
How to implement ISO 27001 Clause 4.1
To implement ISO 27001 Clause 4.1, follow the ISO 27001 Lead Auditor guide How to implement ISO 27001 Clause 4.1
Facilitation Guide: How to Run a Clause 4.1 Workshop
Many organisations make the mistake of having the Information Security Manager sit in a dark room and write the context registry alone. As a Lead Auditor, I can spot this instantly because the context lacks business “flavour.” To pass your audit and build a resilient system, you should run a collaborative workshop. Here is my five step guide to getting it right.
5 Steps to Running a Clause 4.1 Workshop
- Assemble the right team: You cannot define the context of the organisation without the people who actually run it. You must include representatives from IT, HR, Legal, and, crucially, the C-Suite. This ensures you capture strategic business issues, not just technical ones.
- Set the Strategy baseline: Before you talk about security, talk about the business. What are the company goals for the next 12 months? Are you expanding into new territories? Are you launching an AI product? Your ISMS must support these goals to be relevant.
- Run the PESTLE and SWOT exercise: Use the frameworks we discussed above. I recommend using a digital whiteboard or physical sticky notes. Ask each department head what “external shifts” or “internal weaknesses” keep them awake at night.
- Filter for Relevance: This is the most important step. A common mistake is listing every single risk under the sun. You must only document issues that affect the ability of your ISMS to achieve its intended outcomes. If a political shift in a country where you have no customers does not impact your data security, leave it out.
- Obtain Management Sign-off: Once the registry is complete, it must be formally reviewed and approved by senior management. This is your “Auditor’s Proof” that the leadership team is actively involved in the ISMS.
Lead Auditor Tip: When I perform a Stage 1 audit, I often ask to see the meeting minutes from this workshop. If you can show me an invitation list that includes the CEO or COO and a set of minutes showing a healthy debate about business context, you have already won 50% of the auditor’s trust.
Visualising the Workshop Flow
The workshop flow should move from wide-angle business strategy down to narrow-focus security risks. This logical funnel ensures that your technical controls are always aligned with the higher purpose of the organisation.
ISO 27001 Clause 4.1 Implementation Checklist
The ISO 27001 Clause 4.1 Implementation Checklist supports the guide on how to implement ISO 27001 Clause 4.1
How to audit ISO 27001 Clause 4.1
To audit ISO 27001 Clause 4.1, follow the ISO 27001 Lead Auditor guide How to audit ISO 27001 Clause 4.1
Technical Artifact Preview: The ISO 27001 Context Registry
The primary output of ISO 27001 Clause 4.1 is the Context Registry. This is the document I will ask for first during your Stage 1 audit. It acts as the master list of everything that could influence your security posture. A best-in-class registry does not just list issues; it links them to the rest of the standard to ensure your ISMS is fully integrated.
What a “Best-in-Class” Context Registry Looks Like
Below is a mock-up of the headers and data points required for a professional, audit-ready registry. (Swipe left/right on mobile to view full table)
| Issue ID | Type | Issue Description | Impact on ISMS Objectives | Interested Parties (4.2) | Risk ID (6.1) |
|---|---|---|---|---|---|
| C4.1-01 | External | Introduction of the EU AI Act affecting data processing. | High: Requires new compliance checks and algorithmic transparency. | Regulators, Customers | R-042 |
| C4.1-02 | Internal | High staff turnover in the core DevOps team. | Medium: Risk of knowledge loss and insider threat during offboarding. | Employees, Management | R-015 |
| C4.1-03 | External | Climate change impact on primary data centre (2024 Amendment). | Medium: Potential for service downtime due to extreme weather. | Customers, Partners | R-088 |
Lead Auditor Tip: Notice the final two columns. By linking your issues directly to Interested Parties (Clause 4.2) and your Risk Register (Clause 6.1), you are proving to the assessor that your management system is “closed loop.” This is the fastest way to demonstrate maturity and secure your certification.
What Evidence Must You Show the Auditor?
When I conduct a Stage 1 audit, I am looking for more than just a list of issues. To demonstrate that ISO 27001 Clause 4.1 is fully implemented, you should have the following three items ready in your evidence folder:
| Evidence Item | Why It Matters |
|---|---|
| Context Registry | The formal document listing internal/external issues and climate relevance. |
| Workshop Minutes | Proof that senior management and department heads were involved in the process. |
| Management Review Slides | Evidence that Clause 4.1 was presented and signed off at the board level. |
ISO 27001 Clause 4.1 Audit Checklist
The ISO 27001 Clause 4.1 Audit Checklist supports the guide on how to audit ISO 27001 Clause 4.1
Trigger-Based Updates: When to Refresh Your Context
A common audit trap is having a Context Registry dated January, while the business moved to a new country in June. As a Lead Auditor, I look for evidence that your context is “living.” You should update your registry whenever one of these triggers occurs:
- Mergers and Acquisitions: New business units mean new internal cultures and external legal risks.
- Geopolitical Shifts: Conflicts or trade wars impacting your supply chain or cloud provider locations.
- Regulatory Deadlines: The enforcement of new laws like the UK Cyber Security and Resilience Bill or the EU AI Act.
- Major Incidents: A significant data breach often reveals a “contextual blind spot” that was previously undocumented.
- Executive Turnover: A change in the CEO or Board often shifts the risk appetite and strategic direction of the organisation.
Lead Auditor Tip: Don’t wait for the annual review. Add “Context Refresh” as a standing agenda item in your monthly or quarterly security committee meetings. This proves your ISMS is proactive, not reactive.
How to pass the ISO 27001 Clause 4.1 audit
To successfully pass an audit of ISO 27001 Clause 4.1 Understanding The Organisation And Its Context you must
- Identify ISO 27001 internal Issues
- Identify ISO 27001 external issues
- Document internal and external issues in a Context of Organisation Document
Watch this short video on what you need to implement and what will be audited for Clause 4.1.
| Audit Stage | Auditor Focus for Clause 4.1 |
|---|---|
| Stage 1 (Documentation) | Does a Context Registry exist? Is Climate Change mentioned? Is it signed off by the Board? |
| Stage 2 (Implementation) | Can staff explain the context? Are the issues in the registry actually being managed in the Risk Register? |
What an auditor looks for
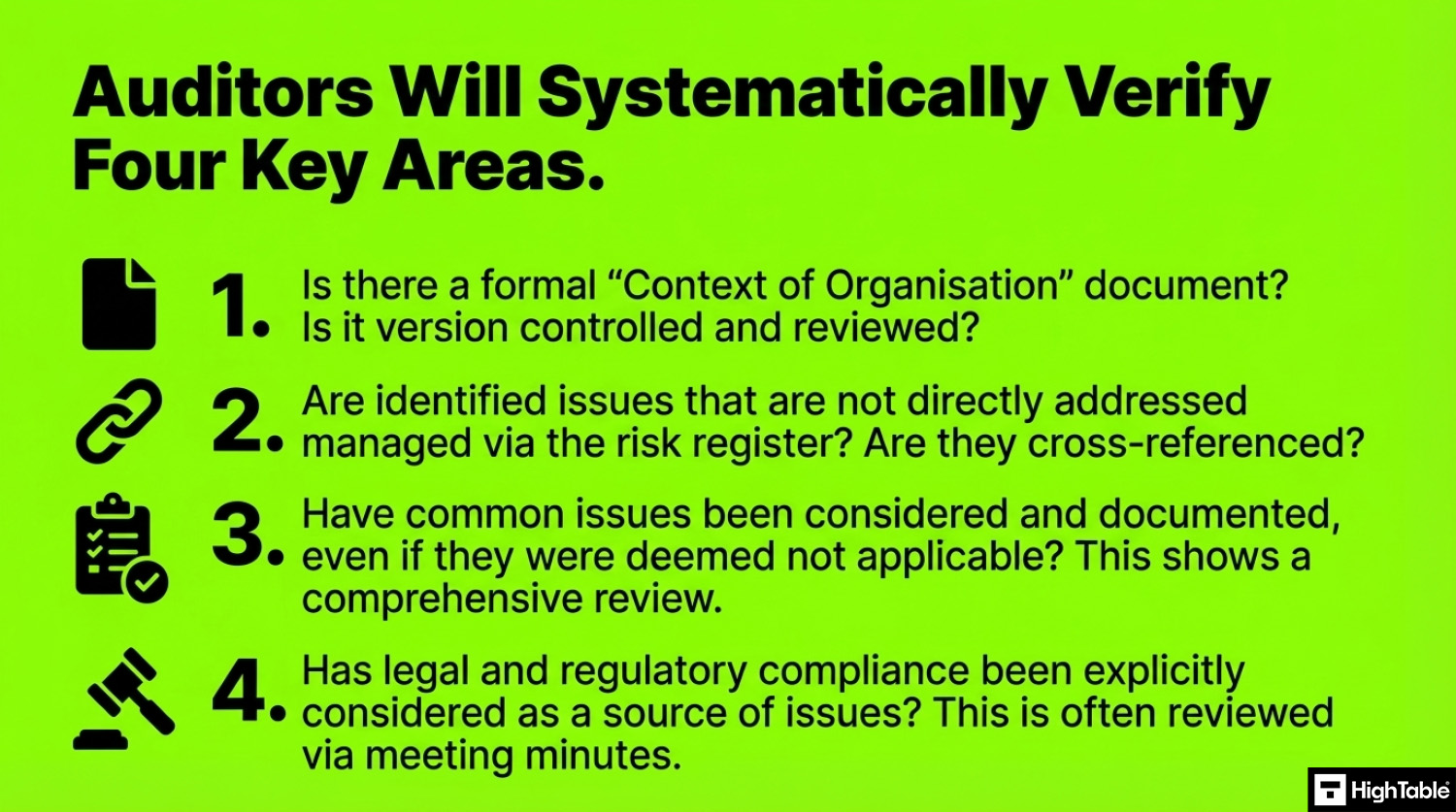
The auditor is going to check a number of areas for compliance with ISO 2001 Clause 4.1 Understanding The Organisation And Its Context.
Let’s take a look at the top 3 in more details.
1. That you have documented your internal and external issues: The simplest way to do this is with the fully populated ISO 27001 Context of Organisation Template. In this short vide I explain why you document your internal and external issues when implementing ISO 27001 clause 4.1.
2. That you are risk managing internal and external issues: If you identify internal issues or external issues that can impact the information security management system and you are not addressing them directly then you need to manage it via risk management. This means as a minimum putting it on the ISO 27001 risk register and following your ISO 27001 risk management process. Be sure to link the issue to the risk by cross referencing.
3. That you have approved the included common issues: Auditors often raise common internal issues and external issues that they have seen elsewhere. Therefore, it is good practice to list out all potential internal issues and external issues that could impact your information security management system, regardless of whether they apply to you or not. If they do not apply to you, record them and explain why. By doing this, you can demonstrate that you have conducted a thorough review and avoid awkward questions or the auditor raising points that you have considered but placed out of scope. Since you have recorded these issues and determined that they do not apply, you can provide evidence to support your conclusion.
Top 3 Audit Findings: Why Companies Fail Clause 4.1
In 2026, certification bodies are being stricter on “Generic” context documents. Here are the three most common non-conformities I raise:
- The “Copy-Paste” Failure: The context registry lists laws like HIPAA when the company only operates in the UK. This proves the organisation does not actually understand its context.
- Missing “The Human Factor”: Documenting software but failing to mention high staff turnover or a culture of “Shadow IT” as an internal issue.
- The Disconnect: Identifying “Ransomware” as a top external issue but having no corresponding risk entry in the Clause 6.1 Risk Register.
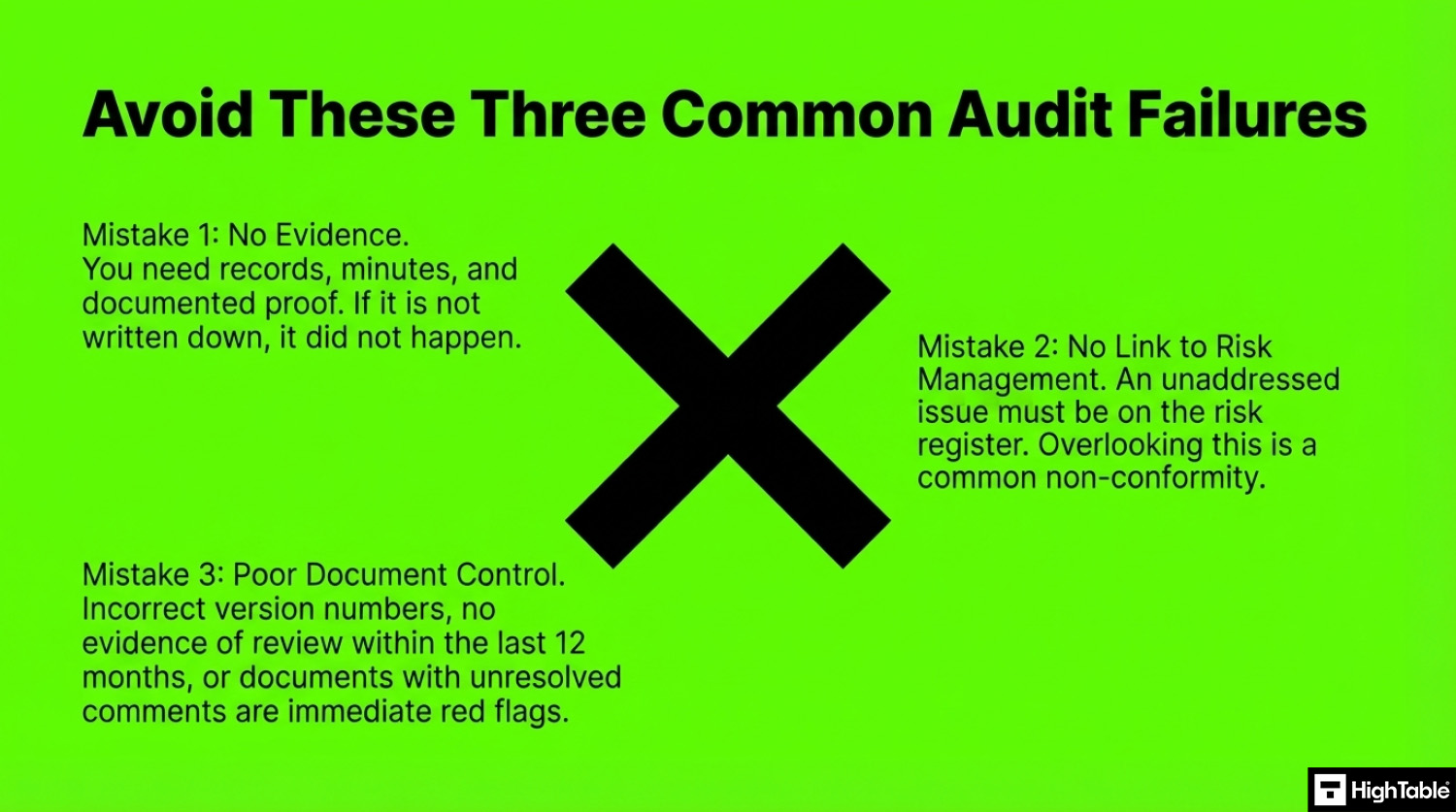
Top 3 ISO 27001 Clause 4.1 Mistakes and How to Fix Them
Based on experience, the top 3 mistakes people make for ISO 27001 clause 4.1 are
- You have no evidence that anything actually happened: You need to keep records and minutes and documented evidence. As a result, recording internal issues and external issues that apply and those that do not shows a thorough understand of the requirement and will avoid awkward questions.
- You did not link to risk management: Where internal issues or external issues are identified but you cannot satisfy it you should have this on the risk register and managed via risk management. This is a point often overlooked. It must be remember that if you identify an issue and do nothing about, or cannot evidence that you have done something about it, it will be raised as a non conformity.
- Your document and version control is wrong: Best practice for documentation includes: Keeping your document version control up to date, Making sure that version numbers match where used, Having a review evidenced in the last 12 months, Keeping your document version control up to date, Having a review evidenced in the last 12 months, Having documents that have no comments
The Tools We Use.
100% Audit Success. Zero AI Guesswork.

ISO 27001 Context of Organisation Template
The ISO 27001 Context Of Organisation template fully meets the requirements of ISO 27001 Clause 4.1 and includes pre-written examples of common internal issues and external issues. The template can be purchase as an individual download or as part of the internationally acclaimed and award-winning ISO 27001 Toolkit.
The Auditor’s Choice: Using SWOT and PESTLE for Clause 4.1
As a Lead Auditor, when I walk into an audit and see a company has just “made a list” of issues, I look deeper. To truly satisfy ISO 27001 Clause 4.1, you need a methodology. The most effective way to demonstrate a “thorough review” of your context is by using the PESTLE and SWOT frameworks specifically through a security lens.
PESTLE Analysis for Information Security
A PESTLE analysis ensures you haven’t missed external issues that could disrupt your ISMS. Here is how a modern tech company should apply this for Clause 4.1 compliance:
| Category | ISO 27001 Clause 4.1 External Issue Example | Impact on ISMS Objectives |
|---|---|---|
| Political | Data sovereignty shifts (e.g., Post-Brexit UK vs. EU divergence). | Requirement to relocate physical servers or change cloud regions. |
| Economic | Cybersecurity insurance premium hikes and stricter underwriting. | Pressure to implement more advanced technical controls to maintain coverage. |
| Social | Shift toward long-term remote-work culture expectations. | Increased risk in “Physical Security” (Annex A 7) and “Device Management.” |
| Technological | Rapid adoption of Generative AI in the daily workforce. | Massive risk of data leakage via unsanctioned LLM usage. |
| Legal | Evolution of the EU AI Act and GDPR enforcement. | Need for specific algorithmic transparency and data protection audits. |
| Environmental | Data center resilience against extreme weather (2024 Amendment). | Reviewing “Business Continuity” (Annex A 5.30) for physical threats. |
SWOT Analysis for the ISMS
While PESTLE looks outward, SWOT is the best tool for identifying internal issues and strategic opportunities for the ISMS. An auditor wants to see that you know your weaknesses.
- Strengths: Strong board-level buy-in, high employee security awareness, automated patch management.
- Weaknesses: Single point of failure in IT staff, legacy hardware in secondary office, limited budget for 24/7 SOC.
- Opportunities: Migration to Tier-4 cloud provider to improve availability, achieving ISO 27001 to win enterprise contracts.
- Threats: Increasing frequency of industry-specific ransomware, supply chain vulnerabilities via third-party vendors.
Lead Auditor Tip: Don’t just do the analysis once. Evidence that you reviewed your SWOT/PESTLE in your Management Review Meeting. This turns a “static document” into a “living ISMS,” which is exactly what certification bodies look for.
The Relevance Filter: How to Decide What Matters
A common mistake is turning your Context Registry into a general business “complaint list.” To pass an ISO 27001 audit, you must only include issues that directly affect your ISMS objectives. I recommend using the CIA Filter to determine relevance:
- Confidentiality: Does this issue increase the risk of unauthorised data access? (e.g. Shadow IT).
- Integrity: Does this issue affect the accuracy or completeness of our data? (e.g. AI model hallucinations).
- Availability: Does this issue threaten our uptime? (e.g. Climate change impacts on data centres).
If an issue does not impact at least one of these three pillars, it is a business issue, but it is not a Clause 4.1 information security issue.
The Audit Trail: How Clause 4.1 Drives the Rest of Your ISMS
In my 30 years of auditing, the most common reason for a Stage 1 failure is an ISMS built in silos. ISO 27001 Clause 4.1 does not exist in a vacuum; it is the “DNA” that determines how the rest of your security system is built. If your internal and external issues aren’t connected to your risks, your ISMS is just a collection of documents, not a management system.
The Clause 4 “Context Loop”
To pass a certification audit, you must demonstrate the “Golden Thread” that connects your business environment to your technical controls. This is how the logic flows:
- Clause 4.1 (The Issues): You identify what is happening in your world (e.g., “We are moving to 100% remote work”).
- Clause 4.2 (The People): You identify who cares about those issues (e.g., “Our customers expect secure remote access”).
- Clause 4.3 (The Boundaries): You define the Scope based on those issues and people (e.g., “Our ISMS must cover all remote endpoints and home-office protocols”).
- Clause 6.1 (The Action): You treat the Risks identified by those issues (e.g., “Risk: Unauthorized access via home Wi-Fi; Treatment: Mandatory MFA and VPN”).
Lead Auditor Tip: When I review a Risk Register (6.1), the first thing I do is cross-reference it with the Context Registry (4.1). If I see a major risk on your register that wasn’t identified as an “issue” in your context, I will question the robustness of your planning process. A truly compliant ISMS uses Clause 4.1 to feed Clause 6.1 directly.
Visualizing the ISMS Ecosystem
Think of Clause 4.1 as the foundation stone. If the stone is crooked, every “wall” you build on top of it, from your Statement of Applicability to your Internal Audit program, will eventually lean and fail under the pressure of a certification body assessment.
Fast track ISO 27001 Clause 4.1 compliance with the ISO 27001 Toolkit
The ISO 27001 toolkit can significantly assist with ISO 27001 Clause 4.1 by providing pre-written templates and structured guidance.
The toolkit provides pre written templates for context of the organisation that includes internal issues and external issues as well as a structured methodology on how to identify them and meet their needs.
| Feature | High Table ISO 27001 Toolkit | Online SaaS / GRC Platforms |
|---|---|---|
| Ownership | Absolute Ownership: You download the files (Word/Excel) and they are yours forever. Your Clause 4.1 “Context” document remains in your local repository. | Rented Compliance: You only have access as long as you pay. If you cancel, you often lose access to the history and logic of your context analysis. |
| Simplicity | Zero Learning Curve: Everyone knows how to use Word and Excel. You can quickly list your internal/external issues without learning a proprietary interface. | High Training Overhead: Your team must learn a complex new system just to document a simple SWOT or PESTLE analysis for Clause 4.1. |
| Cost | One-Off Fee: A single investment for the entire toolkit. No hidden charges or recurring costs as your company grows. | Expensive Subscriptions: High monthly or annual fees that scale with users. You essentially pay a “compliance tax” every month. |
| Freedom | No Vendor Lock-In: You are not tied to a specific software provider. You can move, edit, or back up your files anywhere, ensuring long-term flexibility. | Proprietary Lock-In: Exporting your data can be difficult or “lossy.” You are stuck with their workflow and their specific way of mapping risks. |
| Audit Readiness | Human-Centric Evidence: Forces you to engage with your documentation. Auditors prefer seeing that you understand your context, not just that a software “ticked a box.” | The “Empty Shell” Risk: Platforms often provide an automated “feel” that can lead to a “set and forget” mentality, which Lead Auditors frequently fail during Stage 1. |
How to Present Clause 4.1 to Your CEO
Clause 4.1 is not just a compliance checkbox; it is a strategic business summary. When communicating this to the C-Suite, do not talk about “clauses.” Instead, use this reporting framework:
- External Pressures: “Here are the legal and market shifts (like the EU AI Act) that require us to tighten our security.”
- Internal Weaknesses: “Here are our current resource gaps that we are addressing via the ISMS.”
- Strategic Alignment: “This is how our security system directly supports our goal of expanding into the US market this year.”
Lead Auditor Tip: A CEO who understands that Clause 4.1 protects the business strategy is a CEO who will approve your security budget. Use the context registry to bridge the gap between IT and the board room.
ISO 27001 Clause 4.1 Applicable Laws and Related Standards
| Standard / Law | Relevant Clause or Section | Relationship to ISO 27001 Clause 4.1 | Lead Auditor Relationship Description |
|---|---|---|---|
| NIST CSF v2.0 | GV.OC (Organizational Context) | Direct Alignment | NIST CSF v2.0 Governance category starts exactly where Clause 4.1 does: by understanding the mission, stakeholders, and legal requirements. If you skip this, your entire NIST framework is built on sand. |
| GDPR / UK GDPR | Article 24 (Responsibility) | Context of Processing | Article 24 requires you to implement measures considering the “nature, scope, context and purposes of processing.” This is Clause 4.1 applied specifically to personal data. If you don’t know your business context, you cannot justify your security measures to the ICO. |
| UK Data (Use and Access) Act 2025 | Section 1: Smart Data Schemes | Regulatory Environment | This new Act reduces admin burdens but increases the need to understand your role in the data economy. Clause 4.1 is where you document that you are now a “data holder” under this specific UK legislation. |
| NIS2 Directive (EU) | Article 21 (Risk Management) | Entity Criticality | NIS2 cares about your “criticality.” Clause 4.1 is where you define if you are an “Essential” or “Important” entity. If your context analysis fails to identify your role in the supply chain, you will miss the NIS2 boat entirely. |
| Cyber Security and Resilience Bill (UK) | Section: Managed Service Providers | Supply Chain Context | The UK’s answer to NIS2 targets MSPs specifically. Under Clause 4.1, you must identify if your business model falls under this new legal scope. Failing to recognise this “external issue” leaves you legally exposed. |
| DORA (Digital Operational Resilience Act) | Article 5 (ICT Risk Management) | Financial Sector Context | DORA is Clause 4.1 on steroids for finance. It demands you understand your ICT third-party dependencies. Clause 4.1 is the place where you document these dependencies as key external factors. |
| SOC 2 (Trust Services Criteria) | CC1.1 (COSO Principle 1) | Internal Environment | SOC 2 relies on the COSO framework. CC1.1 requires the board to demonstrate independence and oversight. This is the “Internal Context” of Clause 4.1. No board oversight means no internal context, which means no SOC 2 report. |
| EU AI Act | Article 3 (Definitions/Scope) | Technological Context | You must determine if you are a “provider” or “deployer” of high-risk AI. This determination is a core part of your Clause 4.1 technological context. If you don’t define this, you can’t apply the rest of the Act’s controls. |
| ISO/IEC 42001 (AI Management) | Clause 4.1 (Mirror Clause) | Identical Requirement | This is the exact same control but focused on AI. It requires you to understand the specific internal and external issues regarding AI development. It is the twin of ISO 27001 Clause 4.1 for the AI age. |
| CIRCIA (USA) | Section 2242 (Reportable Entities) | Infrastructure Context | CIRCIA requires 72-hour reporting for critical infrastructure. You use Clause 4.1 to determine if your organization is part of the 16 critical sectors. If you don’t know you’re in scope, you won’t know you’re breaking the law when you don’t report. |
| EU Product Liability Directive (PLD) | Update: Software Liability | External Legal Issue | The updated PLD treats software like a physical product. Under Clause 4.1, you must identify this as a legal risk. If your software causes harm, your “context” just became a massive financial liability. |
| ECCF (European Cybersecurity Cert) | Harmonised Labels | Market Context | If you want to sell in the EU, the ECCF labels are becoming the “external issue” you cannot ignore. Clause 4.1 is where you document the market requirement to hold these security labels to remain competitive. |
| HIPAA (Security Rule) | 164.306 (General Rules) | Organizational Size/Complexity | HIPAA says your security must be “appropriate” to your size and complexity. That is literally the definition of Clause 4.1. You use your context to justify why your HIPAA controls are scaled the way they are. |
| CCPA / CPRA (California) | 1798.100 (Duty of Care) | Geographic Context | If you have customers in California, that is a geographic external issue for Clause 4.1. The “Duty of Care” in CCPA is fulfilled by the risk-based approach that begins with your context analysis. |
Related ISO 27001 Controls
| Relationship Category | Related ISO 27001 Control / Link | Lead Auditor Relationship Description |
|---|---|---|
| Exact Control Match | ISO 27001 Clause 4.1 for AI Companies | This is the exact same control but tailored for the AI sector. We swap generic risks for specific issues like the EU AI Act and model poisoning. If you are in AI, your context must reflect these unique external pressures or you will fail at Stage 1. |
| Exact Control Match | ISO 27001 Clause 4.1 Audit Checklist | This page takes the theory of Clause 4.1 and turns it into a practical “pass or fail” list. It is the exact same control viewed through my eyes as an auditor. Use this to find your gaps before I find them for you. |
| Exact Control Match | How to implement ISO 27001 Clause 4.1 | While the main page defines the “what,” this is the “how.” It provides the step by step workflow for identifying internal and external issues. It is the implementation twin of the core requirement. |
| Exact Control Match | ISO 27001 Clause 4.1 SME Guide | Small businesses often over-engineer their context. This page is the same control simplified for SMEs. It focuses on limited resources as an internal issue, which is the reality for most small teams. |
| Exact Control Match | ISO 27001 Amendment 1: Climate Action | This is the mandatory update to Clause 4.1 released in 2024. It adds a specific requirement to determine if climate change is a relevant issue. You cannot claim to meet Clause 4.1 today without addressing the content on this page. |
| Same Topic (Clause 4) | ISO 27001 Clause 4.2: Interested Parties | Clause 4.1 and 4.2 are two sides of the same coin. You cannot understand your context (4.1) without knowing who your stakeholders are and what they want (4.2). They both feed the same “Context of Organisation” document. |
| Same Topic (Clause 4) | ISO 27001 Context of Organisation Generator | This is the practical output for Clause 4. It provides the templates and tools needed to document the issues identified in Clause 4.1. It is the destination for all the data you gather during your context analysis. |
| Same Topic (Clause 4) | ISO 27001 Glossary: Business Context | This provides the formal definition for the terminology used in Clause 4.1. It ensures that when we talk about “internal issues,” everyone from the board to the auditor is speaking the same language. |
| Same Topic (Clause 4) | ISO 27001 Clause 4.3: Determining the Scope | Your context (4.1) dictates your scope (4.3). If you identify a specific regulatory issue in your context, it must be reflected in the boundaries of your ISMS. This is where the strategic analysis becomes a physical boundary. |
| Broad Topic Match | ISO 27001 Clauses: The Complete Guide | This is the bird’s eye view. It places Clause 4.1 at the very start of the ISMS lifecycle. It explains how context (Clause 4) leads into Leadership (Clause 5) and Planning (Clause 6) to create a functional system. |
Mapping Clause 4.1 to Annex A Controls
As a Lead Auditor, I look for “closed loop” security. If you identify a specific context issue, I expect to see the corresponding technical control in your Statement of Applicability (SoA).
| Contextual Issue (4.1) | Primary Annex A Control |
|---|---|
| Use of Cloud / Third Party Providers | Annex A 5.21 (Managing Information Security in the Supplier Relationship) |
| Remote Workforce / Digital Nomad Culture | Annex A 6.7 (Remote Working) |
| Physical Infrastructure in Risk Zones | Annex A 7.1 (Physical Security Perimeters) |
ISO 27001 Clause 4.1 FAQ
ISO 27001 clause 4.1 is the requirement of defining what the internal and external issues are to the organisation that directly impact the information security system and addressing or accepting them. In February 2024 it was updated to include the need to document if climate change is a relevant issue.
The purpose of ISO27001 Clause 4.1 Understanding The Organisation And Its Context is to ensure you identify, manage and mitigate risks to the management system achieving its intended outcomes.
There are no changes to ISO27001:2022 Clause 4.1 in the 2022 update.
The ISO 27001 standard amended the definition of clause 4.1 in February 2024. This amendment, referred to as ISO 27001 Amendment 1: Climate action changes added climate change to ISO 27001 Clause 4.1.
Yes. It’s not sufficient to simply know them; you must also document them to demonstrate that you considered them. A best practice is to share these issues with the Management Review Team and document the fact that they were shared, signed off, and accepted.
ISO 27001 Clause 4.1 is important because it allows you to understand what can impact your information security management system so you can address it. By understanding the internal and external issues that could impact the information security management system allows to you to plan for them, mitigate and manage them and as a result increase in the effectiveness of the information security management system in meeting the business objectives and needs. Understanding The Organisation And Its Context is important because you need to understand whether or not your management system is going to be effective. To do that you are going to spend time to identify any risks that could impact it. There is a process of continual Improvement built into ISO 27001 that’s going to continually improve this management system but you need to make sure that you’ve documented and understood the issues and given your fledgling information security management system a fighting chance before it gets off the ground.
The following are benefits of implementing ISO 27001 Clause A 4.1: Improved security: You will have an effective information security management system that address known internal and external issues that could impact it Reduced risk: You will reduce the risk to your information security management system by identifying those risks and addressing them Improved compliance: Standards and regulations require context of organisation to be in place Reputation Protection: In the event of a breach having effectively managed risks to the management system will reduce the potential for fines and reduce the PR impact of an event
Responsibility for Understanding The Organisation And Its Context lies with Senior Management and the doing will be delegated to the information security manager.
Internal issues are factors within an organisation that can negatively impact the effectiveness of its Information Security Management System (ISMS). They are inherent risks originating within the organisation that can hinder the ISMS from achieving its objectives, particularly in safeguarding the confidentiality, integrity, and availability of information assets.
Internal issues originate within the organisation itself, such as lack of management commitment, inadequate resource allocation, or resistance to change. External issues stem from factors outside the organisation’s direct control, such as economic downturns, regulatory changes, or competitive pressures.
Identifying internal issues is crucial for several reasons: Risk mitigation: It allows organisations to proactively address potential threats and vulnerabilities. Improved security posture: It helps strengthen security controls and reduce the likelihood of security incidents. Enhanced compliance: It demonstrates a commitment to compliance with ISO 27001 and other relevant regulations. Increased efficiency: It can streamline operations and improve overall productivity. Enhanced reputation: It builds trust with customers, partners, and stakeholders.
Brainstorming sessions: Involve key stakeholders in brainstorming sessions to identify potential internal issues. PESTLE analysis: Adapt the PESTLE framework to identify internal factors such as political, economic, social, technological, legal, and environmental issues. Risk assessments: Conduct regular risk assessments to identify and evaluate potential threats, including those arising from internal factors. Internal audits: Utilise internal audits to uncover potential internal issues and areas for improvement.
Regularly review and update internal issues at least annually. Trigger events such as security incidents, internal audits, management reviews, and changes to risk assessments also warrant immediate review.
Lack of management commitment Inadequate resource allocation Lack of employee awareness and training Poor communication and coordination Resistance to change Lack of regular reviews and updates Inadequate access control management Insufficient incident response planning
Implement corrective and preventive actions to address identified issues. Improve communication and collaboration within the organisation. Enhance employee awareness and training programs. Allocate adequate resources to information security initiatives. Obtain management commitment and support for information security.
Information security management team Department heads Employees at all levels Internal auditors Management representatives
Internal issues are essentially internal risks. Identifying and addressing these issues is a fundamental part of the risk management process within an ISO 27001 framework.
External issues are factors outside an organisation that can negatively impact the effectiveness of its Information Security Management System (ISMS). They are inherent risks originating outside the organisation that can hinder the ISMS from achieving its objectives, particularly in safeguarding the confidentiality, integrity, and availability of information assets.
External issues stem from factors outside the organisation’s direct control, such as economic downturns, regulatory changes, or competitive pressures. Internal issues originate within the organisation itself, such as lack of management commitment, inadequate resource allocation, or resistance to change.
Identifying external issues is crucial for several reasons: Risk mitigation: It allows organisations to proactively address potential threats and vulnerabilities. Improved security posture: It helps strengthen security controls and reduce the likelihood of security incidents. Enhanced compliance: It demonstrates a commitment to compliance with ISO 27001 and other relevant regulations. Increased efficiency: It can streamline operations and improve overall productivity. Enhanced reputation: It builds trust with customers, partners, and stakeholders.
Implement corrective and preventive actions to address identified issues. Improve communication and collaboration within and outside the organisation. Enhance employee awareness and training programs. Join industry specific special interest groups. Maintain contact with authorities.
Information security management team Department heads Employees at all levels External auditors Management representatives
External issues are essentially external risks. Identifying and addressing these issues is a fundamental part of the risk management process within an ISO 27001 framework.
Document internal and external issues within the Context of the Organisation section of the ISO 27001 documentation. Use a table format with two columns: Issue Name and The Issue with a detailed description.
Further Reading
How to implement ISO 27001 Clause 4.1
ISO 27001 Clause 4.1 Implementation Checklist
How to audit ISO 27001 Clause 4.1
ISO 27001 Clause 4.1 Audit Checklist
ISO 27001 Clause 4.1 Understanding the Organisation and Its Context Explained
ISO 27001 Clause 4.1 Executive Briefing Slides