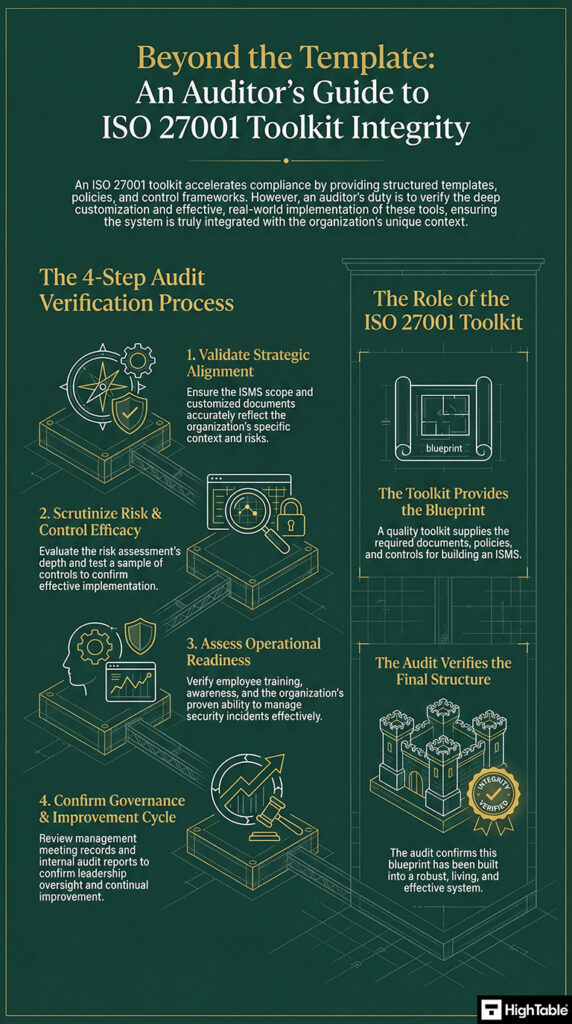
In this tutorial, ISO 27001 Lead Auditor Stuart Barker explains how to audit and ISO 27001 Toolkit. This is article supplements the complete guide to ISO 27001 toolkits – ISO 27001 Toolkit Explained + Templates
Time needed: 2 hours
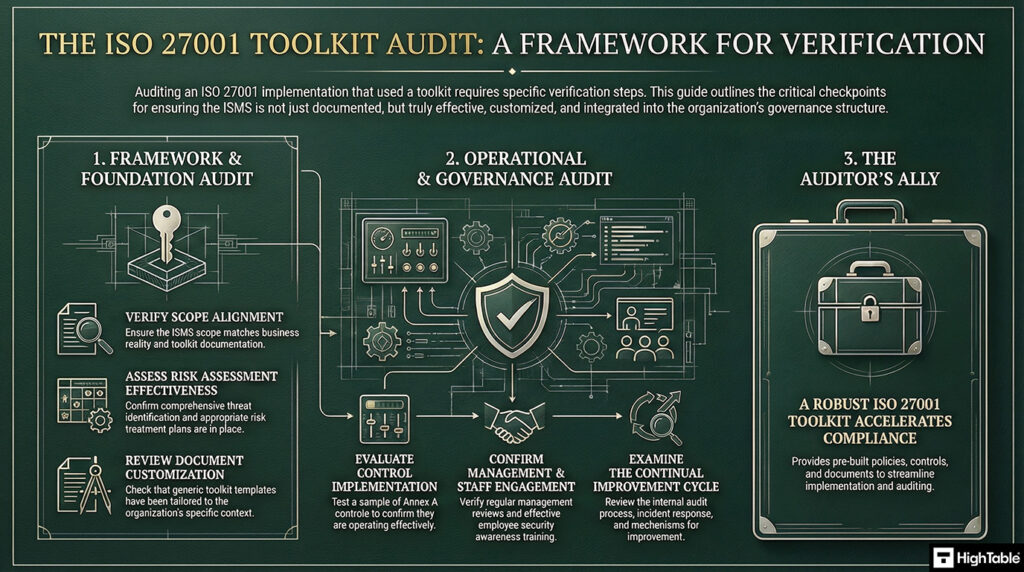
How to audit an ISO 27001 Toolkit:
- Verify Scope Alignment
Check if the ISMS scope defined by the organisation aligns with the scope documented in the toolkit and if it’s still appropriate for the business.
Challenge: Scope creep or misalignment.
Solution: Review scope documentation and interview relevant stakeholders.
- Review Document Customisation
Examine how the toolkit’s templates were customised. Are they truly tailored to the organisation’s specific context, risks, and processes, or are they generic?
Challenge: Insufficient customisation.
Solution: Compare customised documents against actual practices and interview process owners.
- Assess Risk Assessment Effectiveness
Evaluate the risk assessment process. Was it comprehensive? Did it identify relevant threats and vulnerabilities? Are the risk treatment plans appropriate and implemented?
Challenge: Inadequate risk assessment.
Solution: Review risk assessment documentation, interview risk owners, and test the effectiveness of controls. - Evaluate Control Implementation
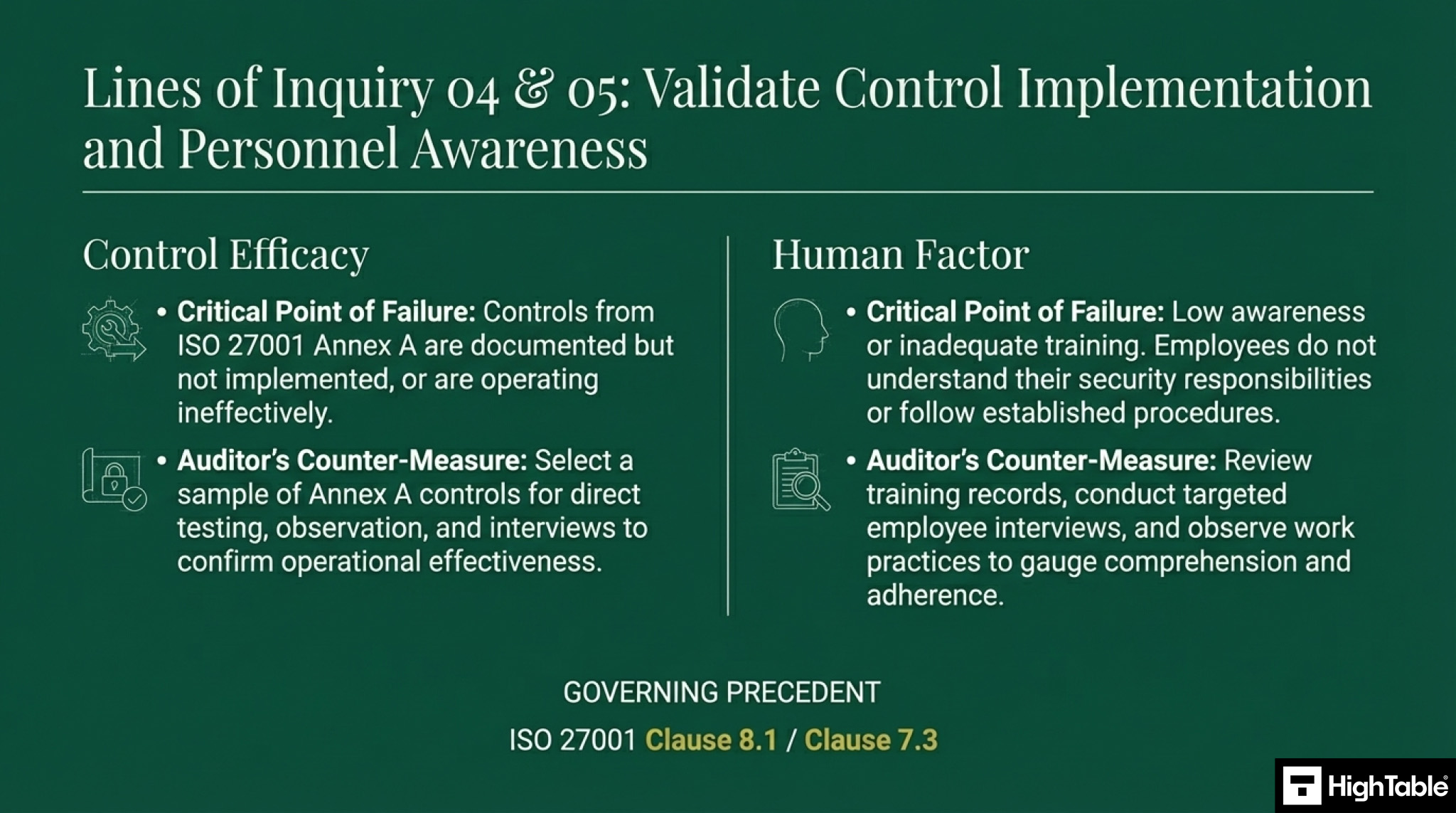
Select a sample of controls from the ISO 27001 Annex A and other relevant sources. Verify if they are implemented as documented and operating effectively.
Challenge: Controls not implemented or ineffective.
Solution: Conduct testing, observation, and interviews to confirm control effectiveness. - Check Training and Awareness
Assess the effectiveness of information security training. Do employees understand their responsibilities and are they following the established procedures?
Challenge: Low awareness or inadequate training.
Solution: Review training records, conduct employee interviews, and observe work practices. - Assess Incident Management
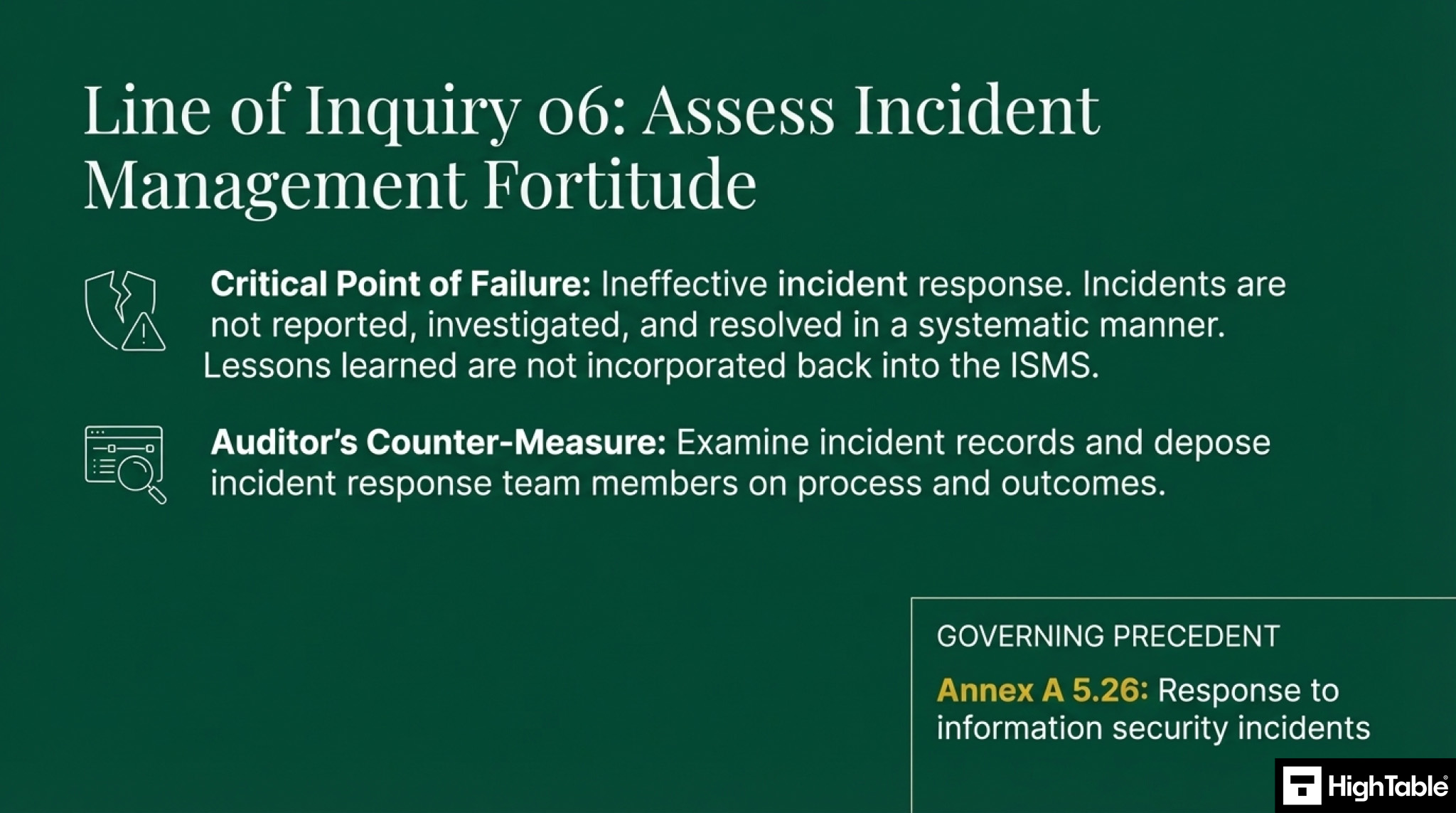
Evaluate the organisation’s ability to handle security incidents. Are incidents reported, investigated, and resolved effectively? Are lessons learned incorporated into the ISMS?
Challenge: Ineffective incident response.
Solution: Review incident records and interview incident response team members. - Examine Internal Audit Process
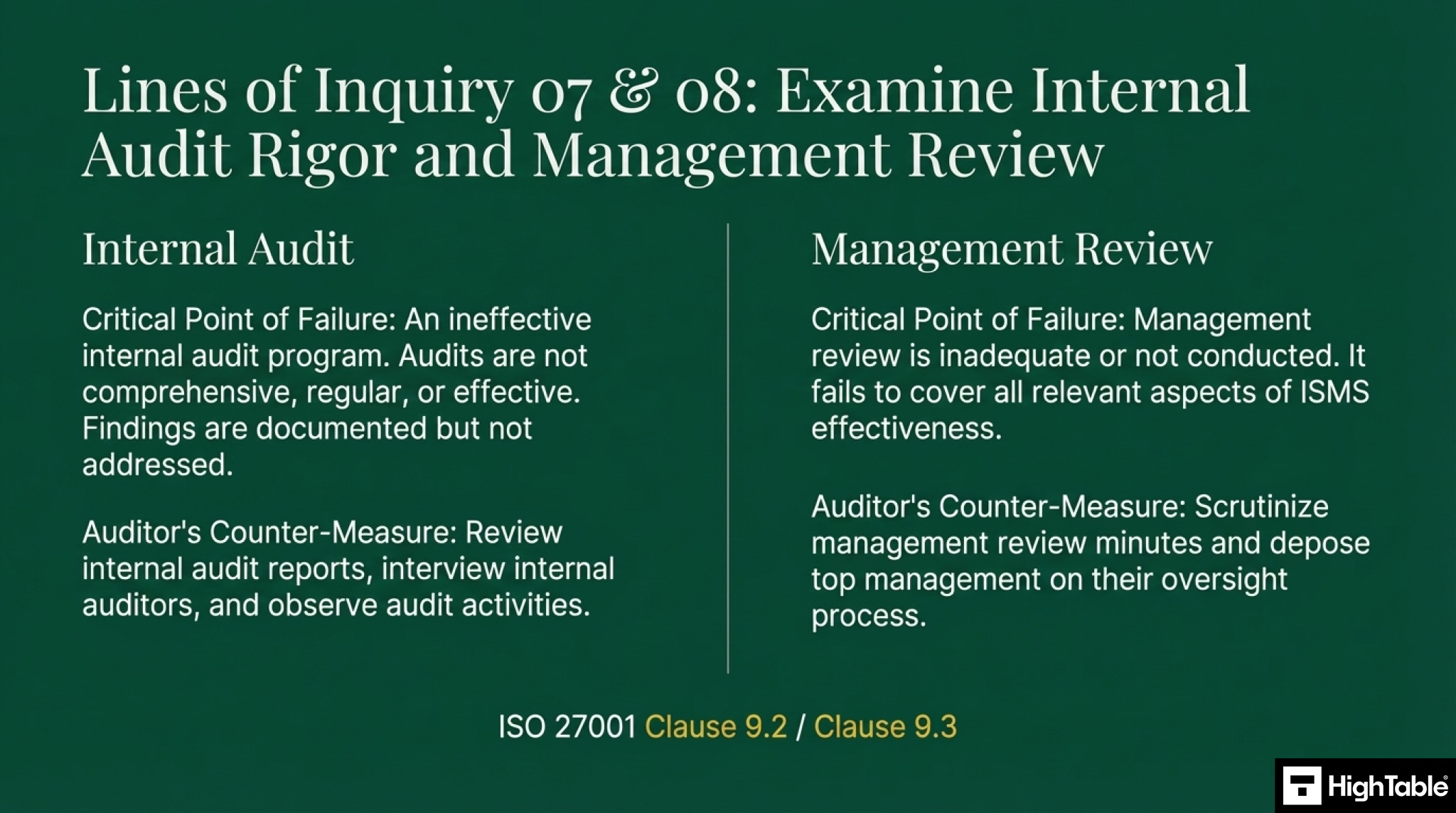
Review the internal audit program. Is it comprehensive? Are audits conducted regularly and effectively? Are findings documented and addressed?
Challenge: Ineffective internal audits.
Solution: Review internal audit reports, interview internal auditors, and observe audit activities. - Verify Management Review
Check if management reviews are conducted regularly. Do they cover all relevant aspects of the ISMS, including the effectiveness of the toolkit and the ISMS itself?
Challenge: Management review not conducted or inadequate.
Solution: Review management review minutes and interview top management. - Review Continual Improvement
Assess the organisation’s approach to continual improvement of the ISMS. Are they actively looking for ways to improve the system and are they implementing changes effectively?
Challenge: Lack of continual improvement.
Solution: Review change management records and interview process owners. - Check Toolkit Maintenance
While you don’t audit the toolkit itself, you can check if the organisation’s use of the toolkit is maintained. Are they keeping up with updates to ISO 27001 or best practices? Are they reviewing the toolkit’s resources periodically?
Challenge: Toolkit becomes outdated or unused.
Solution: Interview the ISMS manager and review document version control.
An Auditors Guide to ISO 27001 Toolkit Integrity