Overview
The Cryptographic Control And Encryption Policy is a high level policy that ensures the proper and effective use of encryption to protect the confidentiality and integrity of confidential information.
What is the ISO 27001 Cryptographic Control And Encryption Policy Template?
The ISO 27001 Cryptographic Control And Encryption Policy Template sets out what you do for the use of cryptography and encryption in your organisation. It sets out clearly what is and what is not allowed. It fully meets the requirements of the ISO 27001:2022 Standard.
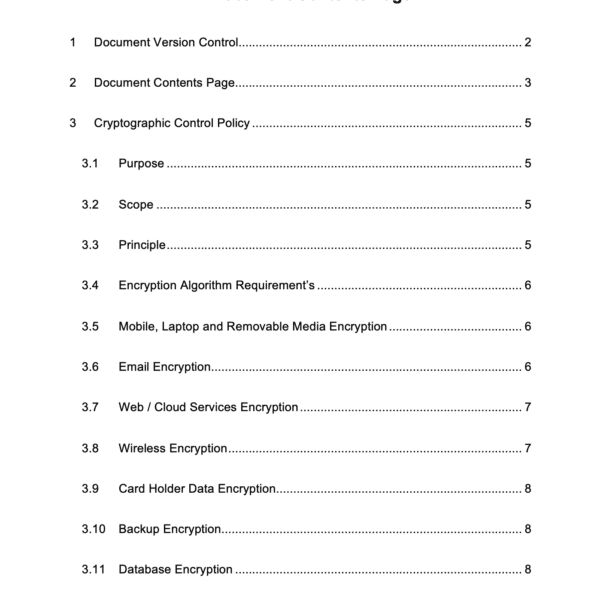
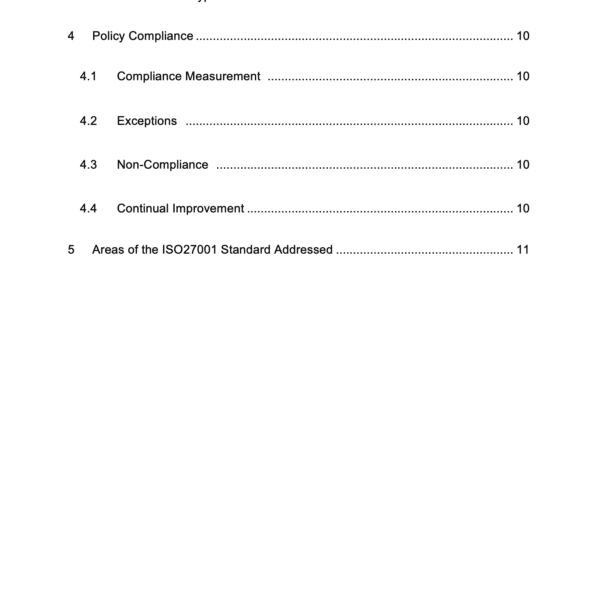
Cryptographic Control And Encryption Policy Template Contents
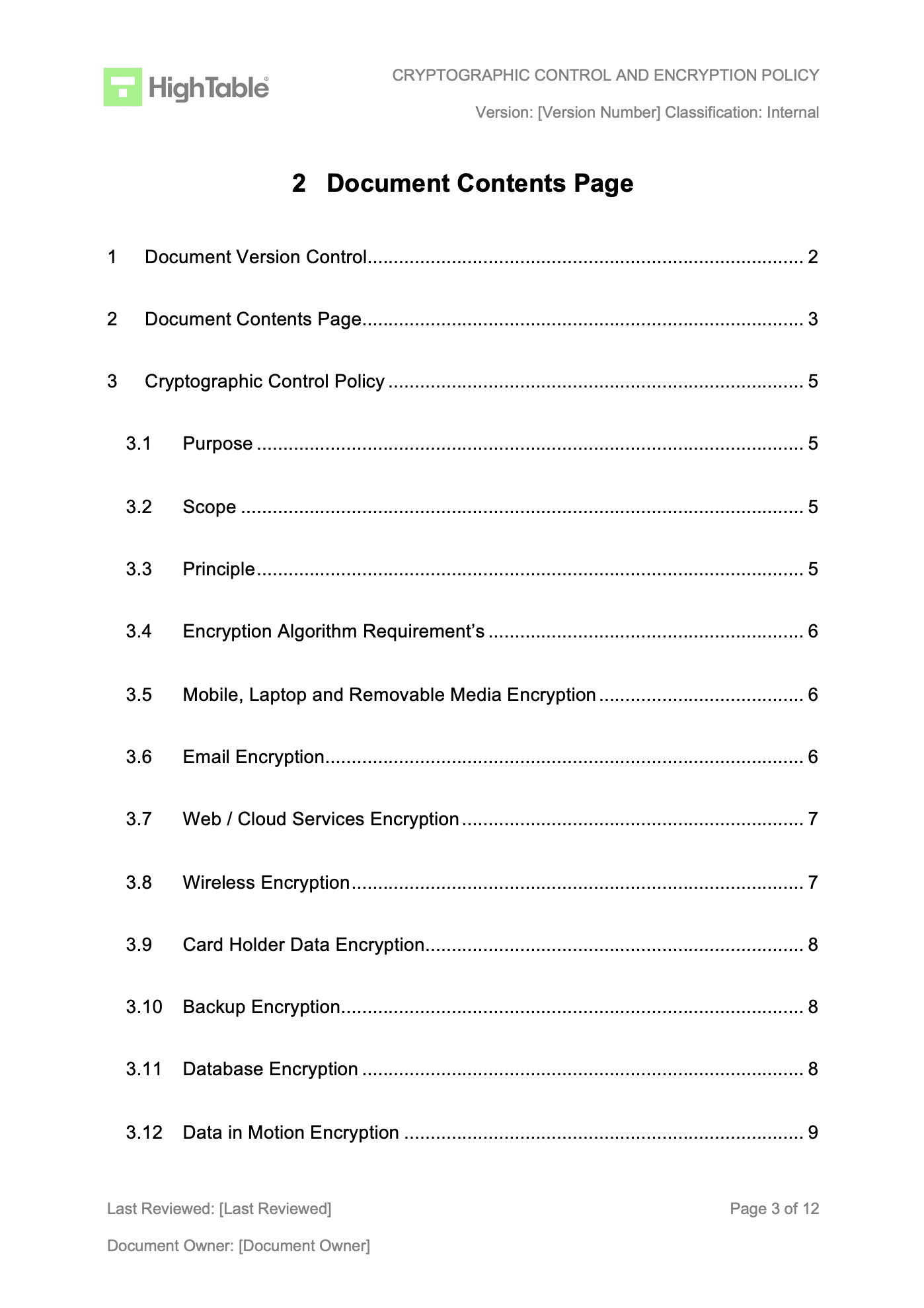
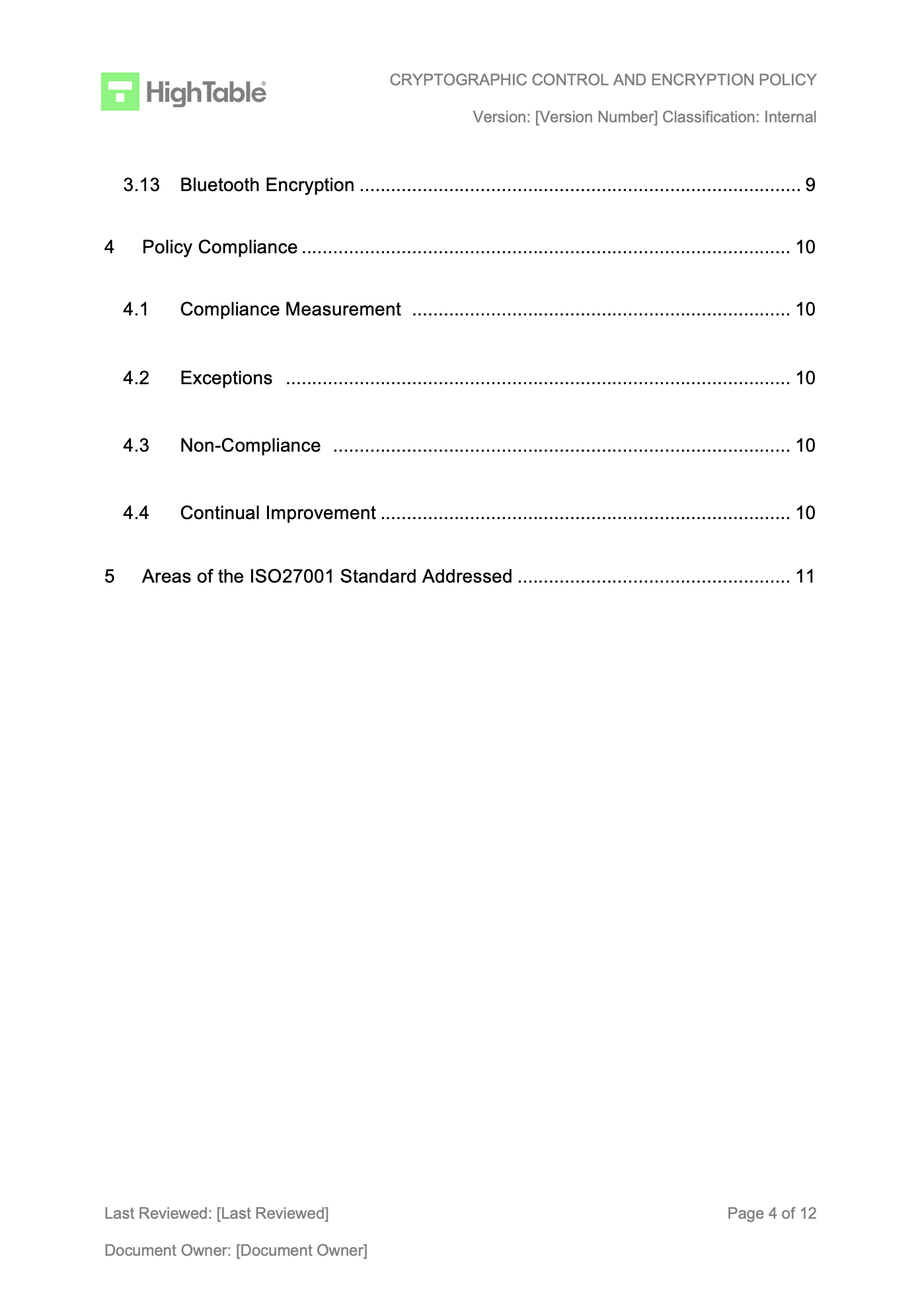
The contents of the Cryptographic Control And Encryption Policy Template are:
Document Version Control Document Contents Page Cryptographic Control Policy Purpose Scope Principle Encryption Algorithm Requirement’s Mobile, Laptop and Removable Media Encryption Email Encryption Web / Cloud Services Encryption Wireless Encryption Card Holder Data Encryption Backup Encryption Database Encryption Data in Motion Encryption Bluetooth Encryption Policy Compliance Compliance Measurement Exceptions Non-Compliance Continual Improvement Areas of the ISO 27001 Standard Addressed
Cryptographic Control And Encryption Policy Template Example
ISO 27001 Cryptographic Control and Encryption Policy Template FAQ
The ISO 27001 Cryptographic Control And Encryption Policy Template is in Microsoft Word format
Anyone that wants to save time and money and have a pre populated ISO 27001 Cryptographic Control And Encryption Policy that fully meets the requirements of the ISO 27001 standard and is ready to go.
The ISO 27001 Cryptographic Control And Encryption Policy template is all ready written so you change the logo, brand it has you and you are ready to go. You can customise it based on your own requirements and needs.
It is 100% complete. It just requires a fast rebrand, checking and some minor additions that are clearly sign posted and marked.
Yes. It fully meets the 2022 updated requirements to the ISO 27001 standard. It is also backward compatible with previous versions of the standard.
It is available as an immediate download once payment has been received.
No. The ISO 27001 Cryptographic Control And Encryption Policy Template is designed to be easy to implement and easy to configure. It comes with an easy to follow step by step guide. You are provided with a free hour of training if you need it.
The ISO 27001 Cryptographic Control And Encryption Policy meets the requirements of ISO 27001 Annex A 5.1 Policies for Information Security ISO 27001 Annex A 8.24 Use of Cryptography
We offer a free 30 minute 1-to-1 consultation as well as a free weekly ISO 27001 Q and A call and the unique ability to purchase consulting by the hour.
It depends on what you are trying to achieve. It works as a stand alone policy but is designed to be part of a pack of information security policies that meet the needs of your business. The Ultimate ISO 27001 Toolkit is everything you need for ISO 27001 Certification.
You can get all of the required ISO 27001 Policies in the ISO 27001 Policy Template Bundle. The policy is sold stand alone as it serves a specific purpose and often people just want this one policy. When you deploy information security policies into your organisation you may not need all of the policies so we make them available individually. The benefits of having individual policies are: They can be shared only with the people that need the information They can be allocated an owner to update them You can deploy only the policies you need. In addition the 2022 update to the ISO 27001 standard explicitly calls out having a headline policy and subordinate policies.
We estimate that on average it will take you less than 1 hour. The templates require information that you know so there is nothing complicated.
The benefits of using the ISO 27001 Cryptographic Control And Encryption Policy template are: Save time: the policy is already fully populated and ready to go Meet the requirements of the standard: the policy template is mapped directly to the requirements of the ISO 27001:2022 standard Save money: you will not have to pay consultants to research and write the policy for you
Payments are handled entirely through Stripe. They are very secure. We do not handle the payment transaction. We do not store, process or transmit your card holder data.